- Table of Contents
-
- 05-Web configuration examples (AC+fit AP)
- 01-Telnet Access Control Configuration Example
- 02-IPv6 Telnet Access Control Configuration Example
- 03-Web Access Control Configuration Example
- 04-User Role Assignment for Local Web Authentication Users Configuration Example
- 05-SSH Local Authentication Configuration Example
- 06-SSH User Remote Password Authentication Configuration Example
- 07-IPv6 SSH User Remote Password Authentication Configuration Example
- 08-Password Control Configuration Example
- 09-Licensing Configuration Example
- 10-Automatic License Installation Configuration Example
- 11-Layer 2 Static Link Aggregation Configuration Example
- 12-Layer 2 Dynamic Link Aggregation Configuration Example
- 13-PPPoE Client Configuration Example
- 14-Static IPv6 Address Configuration Example
- 15-IPv6 Static Routing Configuration Example
- 16-Static IPv4 DNS Configuration Example
- 17-Static IPv6 DNS Configuration Example
- 18-IGMP Snooping Configuration Example
- 19-MLD Snooping Configuration Example
- 20-IPv4 DNS Proxy Configuration Example
- 21-IPv6 DNS Proxy Configuration Example
- 22-Static NAT Configuration Example
- 23-Dynamic NAT Configuration Example
- 24-IPv4 ACL-Based Packet Filter Configuration Example
- 25-IPv6 ACL-Based Packet Filter Configuration Example
- 26-ARP Attack Protection Configuration Example
- 27-ARP Proxy Configuration Example
- 28-Dynamic IPv4 DNS Configuration Example
- 29-Dynamic IPv6 DNS Configuration Example
- 30-WLAN Access Configuration Example
- 31-Different Wireless Services on Different Radios Configuration Example
- 32-CAPWAP Tunnel Establishment Through DHCP Configuration Example
- 33-CAPWAP Tunnel Establishment Through DHCPv6 Configuration Example
- 34-CAPWAP Tunnel Establishment Through DNS Configuration Example
- 35-CAPWAP Tunnel Establishment Through DNSv6 Configuration Example
- 36-Auto AP Configuration Example
- 37-AP Group Configuration Example
- 38-Radio Management Configuration Example
- 39-Load Balancing Group-Based Session-Mode Load Balancing Configuration Example
- 40-Radio-Based Session-Mode Load Balancing Configuration Example
- 41-A-MPDU and A-MSDU Configuration Example
- 42-Device Classification and Countermeasure Configuration Example
- 43-Malformed Packet Detection and Flood Attack Detection Configuration Example
- 44-Signature-Based Attack Detection Configuration Example
- 45-802.1X RADIUS-Based AAA Configuration Example
- 46-VLAN Interface-Based Direct Portal Authentication Configuration Example
- 47-Service Template-Based Direct Portal Authentication Configuration Example
- 48-Wireless Spectrum Analysis Configuration Example
- 49-Auto DFS Configuration Examples
- 50-Auto TPC Configuration Examples
- 51-Whitelist-Based Client Access Control Configuration Example
- 52-Blacklist-Based Client Access Control Configuration Example
- 53-CAC Configuration Example
- 54-WLAN Probe Configuration Example
- 55-Intra-AC Roaming Configuration Example
- 56-Bonjour Gateway Configuration Example
- 57-IPv4 Multicast Optimization Configuration Examples
- 58-IPv6 Multicast Optimization Configuration Examples
- 59-Ping Configuration Example
- 60-Local Packet Capture Configuration Example
- 61-Remote Packet Capture Configuration Example
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 05-SSH Local Authentication Configuration Example | 80.77 KB |
|
|
|
H3C Access Controllers |
|
Comware 7 SSH Local Authentication |
|
Configuration Example |
Copyright © 2022 New H3C Technologies Co., Ltd. All rights reserved.
No part of this manual may be reproduced or transmitted in any form or by any means without prior written consent of New H3C Technologies Co., Ltd.
Except for the trademarks of New H3C Technologies Co., Ltd., any trademarks that may be mentioned in this document are the property of their respective owners.
The information in this document is subject to change without notice.
Example: Configuring SSH local authentication
Configuring the VLAN and the VLAN interface
Configure the administrator account
Overview
The following information provides an example for configuring the device as an Stelnet server that provides local authentication for login users.
Prerequisites
The following information applies to Comware 7-based access controllers. Procedures and information in the examples might be slightly different depending on the software or hardware version of the H3C access controllers.
The configuration examples were created and verified in a lab environment, and all the devices were started with the factory default configuration. When you are working on a live network, make sure you understand the potential impact of every command on your network.
The following information is provided based on the assumption that you have basic knowledge of AAA and SSH.
Example: Configuring SSH local authentication
Network configuration
As shown in Figure 1, the device is the gateway of the enterprise network. Use SSH to ensure security of the device management.
Configure the device as an Stelnet server and the host as an Stelnet client. The Stelnet server uses password authentication to authenticate the Stelnet client. The username and password of the Stelnet client are saved on the Stelnet server.
After the network administrator logs in to the device from the host through Stelnet, the administrator can configure and manage the device.
Procedures
Enabling the Stelnet service
1. Click the System View tab at the bottom of the page.
2. From the navigation pane, select Network Configuration > Management Protocols.
3. Click the SSH tab.
4. Enable the Stelnet service.
Configuring the VLAN and the VLAN interface
1. Click the System View tab at the bottom of the page.
2. From the navigation pane, select Network Configuration > VLAN.
3. Click the Create VLANs
button ![]() to create VLAN 2.
to create VLAN 2.
4. Click the Edit button ![]() for
VLAN 2.
for
VLAN 2.
5. Add GigabitEthernet 1/0/2 to the untagged port list.
6. Select Configure VLAN interface, and assign an IP address to VLAN-interface 2.
7. Click Apply.
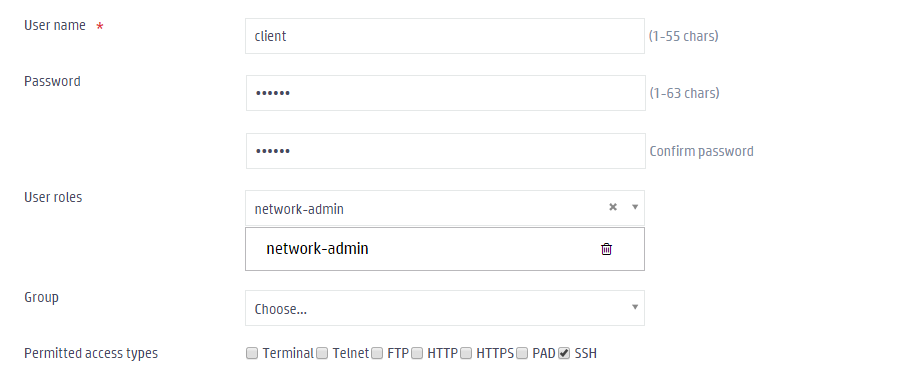
Configure the administrator account
1. Click the System View tab at the bottom of the page.
2. From the navigation pane, select System > Administrators.
4. Configure the administrator account as follows:
a. Set the username and password to client and aabbcc, respectively.
b. Select network-admin from the user roles list.
c. Select SSH for the permitted access types parameter.
Figure 2 Configure the administrator account
5. Click Apply.
Verifying the configuration
This example uses PuTTY0.58 as the SSH client software to verify the configuration.
1. Execute PuTTY on the host.
2. Enter the IP address of the AC in the Host Name (or IP address) field.
3. Click Open.
4. Verify that you can use username client and password aabbcc to log in to the configuration page of the AC.
Related documentation
H3C Access Controllers Web-Based Configuration Guide