- Table of Contents
-
- 09-Configuration Examples
- 01-Web Login Configuration Examples
- 02-Internet Access Through a Static IP Address Configuration Examples
- 03-Internet access through PPPoE configuration examples
- 04-License Configuration Examples
- 05-Signature Library Upgrade Configuration Examples
- 06-Software Upgrade Examples
- 06-Software Upgrade Examples (only for F50X0-D and F5000-AK5X5 firewalls)
- 07-Routing deployment configuration examples
- 08-Transparent deployment configuration examples
- 09-Static routing configuration examples
- 10-RIP configuration examples
- 11-OSPF configuration examples
- 12-BGP configuration examples
- 13-Policy-based routing configuration examples
- 14-Security Policy Configuration Examples
- 15-APR-Based Security Policy Configuration Examples
- 16-Object Group Configuration Examples
- 17-User identification configuration examples
- 18-Attack defense configuration examples
- 19-IPCAR Configuration Examples
- 20-IPS Configuration Examples
- 21-URL Filtering Configuration Examples
- 22-Anti-Virus Configuration Examples
- 23-File Filtering Configuration Examples
- 24-Data Filtering Configuration Examples
- 25-WAF Configuration Examples
- 26-IP Reputation Configuration Examples
- 27-APT Defense Configuration Examples
- 28-NetShare Control Configuration Examples
- 29-Bandwidth Management Configuration Examples
- 30-IPsec configuration examples
- 31-SSL VPN IP access configuration examples
- 31-SSL VPN TCP access configuration examples
- 31-SSL VPN Web access configuration examples
- 32-L2TP Configuration Examples
- 33-NAT configuration examples
- 34-NPTv6 Configuration Examples
- 35-Policy-based NAT configuration examples
- 36-NAT hairpin configuration examples
- 37-NAT Flow Logging Configuration Examples
- 38-Inbound Link Load Balancing Configuration Examples
- 39-Outbound Link Load Balancing Configuration Examples
- 40-Server Load Balancing Configuration Examples
- 41-Transparent DNS Proxy Configuration Examples
- 42-High Availability Group Configuration Examples
- 43-Context Configuration Examples
- 43-Context Configuration Examples(only for F50X0-D and F5000-AK5X5 firewalls)
- 44-IRF configuration examples
- 44-IRF configuration examples(only for F50X0-D and F5000-AK5X5 firewalls)
- 45-DHCP configuration examples
- 46-DNS configuration examples
- 47-Server Connection Detection Configuration Examples
- 48-Connection Limit Configuration Examples
- 49-Public key management configuration examples
- 50-SSL Decryption Configuration Examples
- 51-MAC Address Learning Through a Layer 3 Device Configuration Examples
- 52-4G Configuration Examples
- 53-WLAN Configuration Examples
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 43-Context Configuration Examples | 203.51 KB |
Context configuration examples
Contents
· Example: Configuring contexts
The following information provides context configuration examples.
This document is not restricted to specific software or hardware versions. Procedures and information in the examples might be slightly different depending on the software or hardware version of the device.
The configuration examples were created and verified in a lab environment, and all the devices were started with the factory default configuration. When you are working on a live network, make sure you understand the potential impact of every command on your network.
The following information is provided based on the assumption that you have basic knowledge of the context feature.
When you assign VLANs to contexts, follow these restrictions and guidelines:
· For contexts without the VLAN-unshared attribute, you can only assign VLANs to them and cannot use the vlan command to create VLANs for them. Before the assignment, you must create the VLANs on the default context.
· You cannot assign the following VLANs to a context without the VLAN-unshared attribute:
¡ VLAN 1.
¡ Default VLANs of interfaces.
¡ VLANs for which you have created VLAN interfaces.
When you assign interfaces to contexts, follow these restrictions and guidelines:
· Subinterfaces, VLAN interfaces, and aggregate interfaces can be assigned to a context only in shared mode.
· After assigning a subinterface to a context, you cannot assign its primary interface to a context. After assigning a primary interface to a context, you cannot assign its subinterfaces to a context.
· Do not assign member interfaces of an aggregate interface to a context in shared mode.
· After assigning an interface to contexts in shared mode, you cannot assign the interface to contexts in exclusive mode before reclaiming the interface.
· Do not assign IRF physical interfaces to a non-default context.
· If a subinterface of a Layer 3 interface is a member interface of a Reth interface, do not assign the Layer 3 interface to a non-default context.
Network configuration
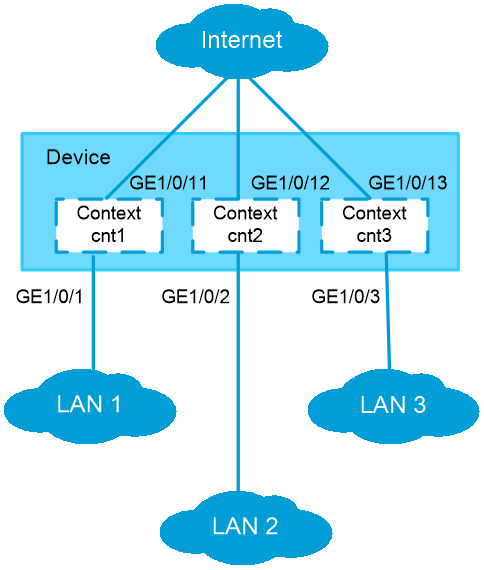
As shown in Figure 1, configure contexts for the LANs as follows:
· LAN 1 has a large number of users and complicated services. Configure context cnt1 for LAN 1. Assign 60% disk space and 60% memory space to the context and set the CPU weight to 8. Assign GigabitEthernet 1/0/1 and GigabitEthernet 1/0/11 to the context.
· LAN 2 has a normal scale of users. Configure context cnt2 for LAN 2. Leave the context to use the default amount of disk space and the default amount of memory space. Assign GigabitEthernet 1/0/2 and GigabitEthernet 1/0/12 to the context.
· LAN 3 has a small number of users. Configure context cnt3 for LAN 3. Assign 30% disk space and 30% memory space to the context and set the CPU weight to 3. Assign GigabitEthernet 1/0/3 and GigabitEthernet 1/0/13 to the context.
Software versions used
This configuration example was created and verified on R8860 of the F1000-AI-55 device.
Procedure
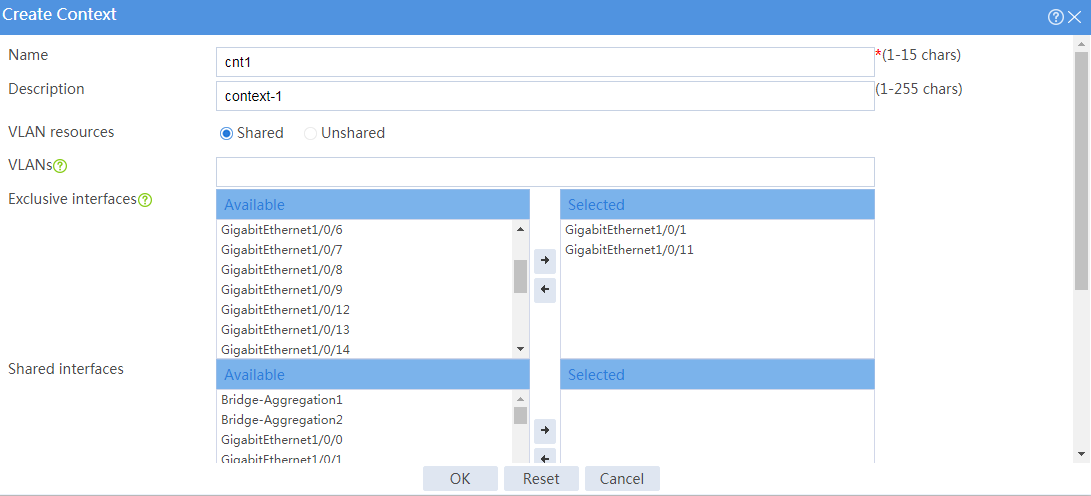
1. Configure context cnt1:
# On the top navigation bar, click System.
# From the navigation pane, select Virtualization Advanced Settings > Contexts > Contexts.
# Click Create.
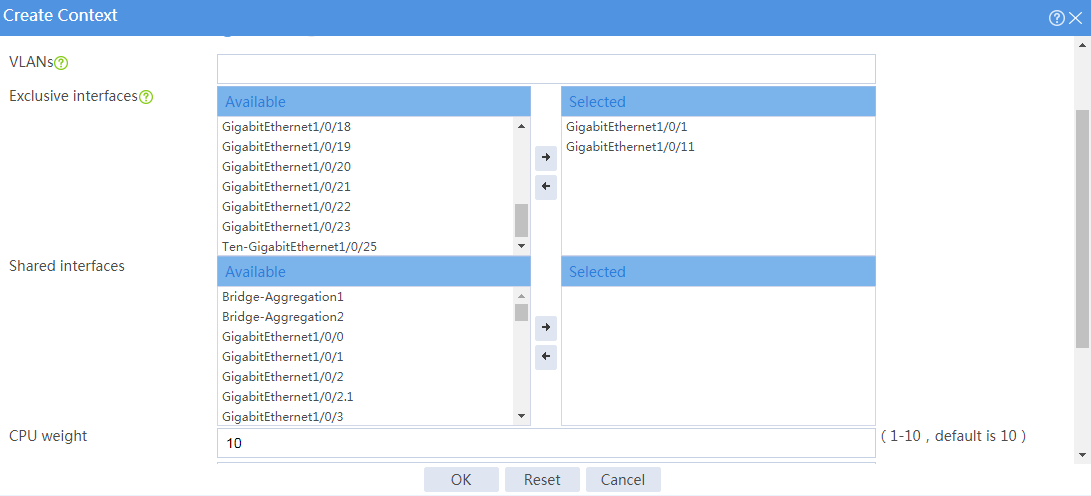
# Configure context cnt1 as shown in Figure 2.
# Click OK.
# Select context cnt1 from the context list and click Start.
Figure 3 Starting context cnt1
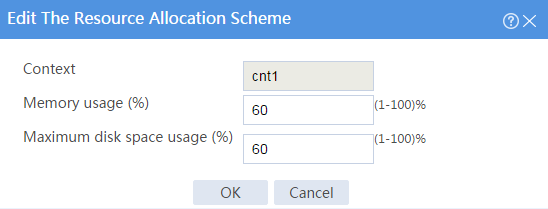
# From the navigation pane, select Virtualization Advanced Settings > Contexts > Resource Allocation.
# Click context cnt1 and edit the resource allocation scheme for the context as shown in Figure 4.
# Click OK.
Figure 4 Editing the resource allocation scheme
2. Configure context cnt2 and cnt3 in the same way you configure context cnt1.
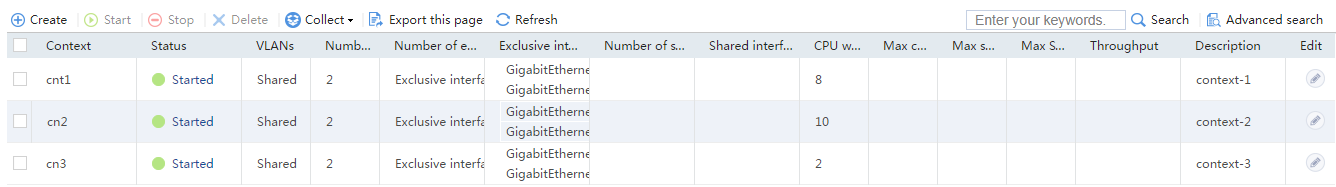
Verifying the configuration
1. On the top navigation bar, click System.
2. From the navigation pane, select Virtualization Advanced Settings > Contexts > Contexts.
3. Verify that the contexts are listed and their settings are as configured.
Figure 5 Viewing contexts
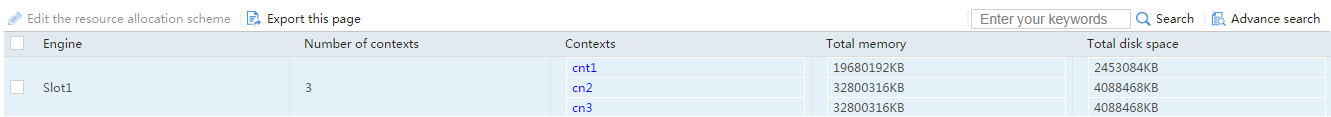
4. From the navigation pane, select Virtualization Advanced Settings > Contexts > Resource Allocation to view the amounts of memory and disk resources allocated to contexts.
Figure 6 Viewing context resource allocation
5. From the navigation pane, select Virtualization Advanced Settings > Contexts > Resource Usage to view the resource usage of contexts
Figure 7 Viewing resource usage of contexts