- Table of Contents
-
- 08-Security Configuration Guide
- 00-Preface
- 01-AAA configuration
- 02-802.1X configuration
- 03-MAC authentication configuration
- 04-Portal configuration
- 05-Web authentication configuration
- 06-Triple authentication configuration
- 07-Port security configuration
- 08-Password control configuration
- 09-Keychain configuration
- 10-Public key management
- 11-PKI configuration
- 12-IPsec configuration
- 13-SSH configuration
- 14-SSL configuration
- 15-Attack detection and prevention configuration
- 16-TCP attack prevention configuration
- 17-IP source guard configuration
- 18-ARP attack protection configuration
- 19-ND attack defense configuration
- 20-uRPF configuration
- 21-MFF configuration
- 22-FIPS configuration
- 23-MACsec configuration
- 24-802.1X client configuration
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 20-uRPF configuration | 157.29 KB |
Contents
Restrictions and guidelines: uRPF configuration
Display and maintenance commands for uRPF
IPv6 uRPF application scenario
Restrictions and guidelines: IPv6 uRPF configuration
Enabling IPv6 uRPF on an interface
Display and maintenance commands for IPv6 uRPF
Configuring uRPF
About uRPF
Unicast Reverse Path Forwarding (uRPF) protects a network against source address spoofing attacks, such as DoS and DDoS attacks.
uRPF application scenario
Attackers send packets with a forged source address to access a system that uses IPv4-based authentication, in the name of authorized users or even the administrator. Even if the attackers or other hosts cannot receive any response packets, the attacks are still disruptive to the attacked target.
Figure 1 Source address spoofing attack
As shown in Figure 1, an attacker on Router A sends the server (Router B) requests with a forged source IP address 2.2.2.1 at a high rate. Router B sends response packets to IP address 2.2.2.1 (Router C). Consequently, both Router B and Router C are attacked. If the administrator disconnects Router C by mistake, the network service is interrupted.
Attackers can also send packets with different forged source addresses or attack multiple servers simultaneously to block connections or even break down the network.
uRPF can prevent these source address spoofing attacks. It checks whether an interface that receives a packet is the output interface of the FIB entry that matches the source address of the packet. If not, uRPF considers it a spoofing attack and discards the packet.
uRPF check modes
uRPF supports strict and loose modes.
Strict uRPF check
To pass strict uRPF check, the source address of a packet and the receiving interface must match the destination address and output interface of a FIB entry. In some scenarios (for example, asymmetrical routing), strict uRPF might discard valid packets.
Strict uRPF is often deployed between a PE and a CE.
Loose uRPF check
To pass loose uRPF check, the source address of a packet must match the destination address of a FIB entry. Loose uRPF can avoid discarding valid packets, but might let go attack packets.
Loose uRPF is often deployed between ISPs, especially in asymmetrical routing.
uRPF extended functions
Using the default route in uRPF check
When a default route exists, all packets that fail to match a specific FIB entry match the default route during uRPF check and thus are permitted to pass. To avoid this situation, you can disable uRPF from using any default route to discard such packets. If you allow using the default route (set by using allow-default-route), uRPF permits packets that only match the default route.
By default, uRPF discards packets that can only match a default route. Typically, you do not need to configure the allow-default-route keyword on a PE device because it has no default route pointing to the CE. If you enable uRPF on a CE interface and the CE interface has a default route pointing to the PE, specify the allow-default-route keyword.
Network application
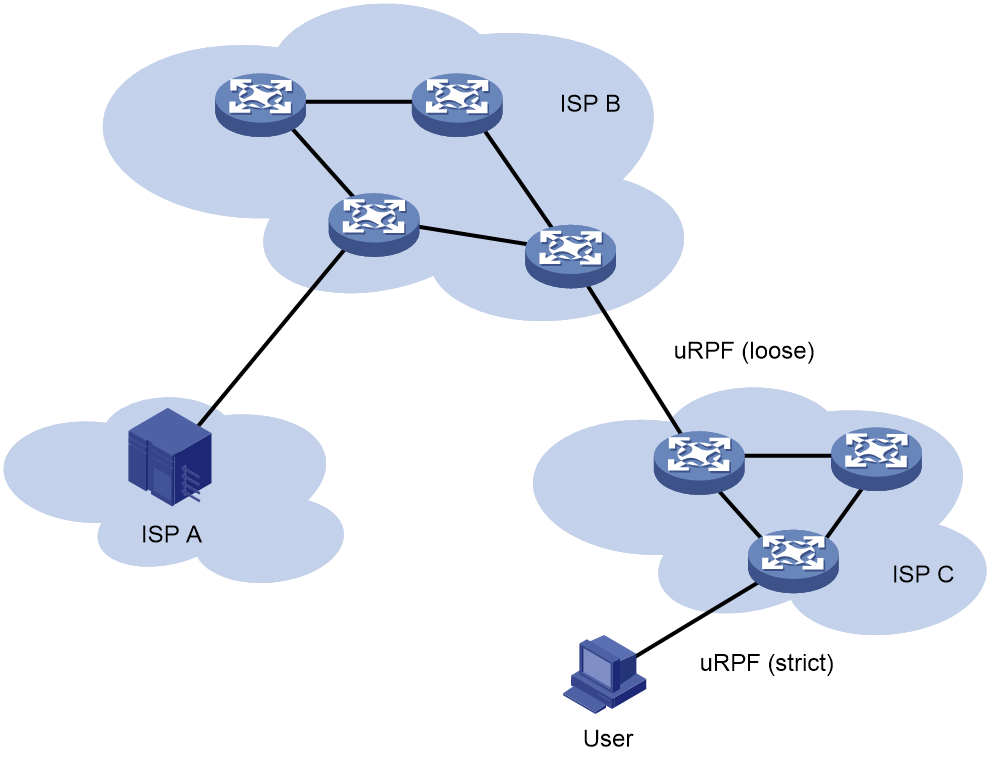
As shown in Figure 2, strict uRPF check is configured between an ISP network and a customer network. Loose uRPF check is configured between ISPs.
Restrictions and guidelines: uRPF configuration
If you enable uRPF on an interface, you can use the display ip interface command to display statistics about packets discarded by uRPF (displayed as "Drops" and "Suppressed drops").
Do not configure the allow-default-route keyword for loose uRPF check. Otherwise, uRPF might fail to work.
Do not configure both strict uRPF check and loose IPv6 uRPF check, or loose uRPF check and strict IPv6 uRPF check on an interface.
Do not use strict uRPF if ECMP routing is available in the network. Service packets that travel along ECMP routes cannot pass the strict uRPF check and will be dropped.
Enabling uRPF on an interface
1. Enter system view.
system-view
2. Enter Layer 3 interface view.
interface interface-type interface-number
3. Enable uRPF.
ip urpf { loose [ allow-default-route ] | strict [ allow-default-route ] }
By default, uRPF is disabled.
Display and maintenance commands for uRPF
Execute display commands in any view.
|
Task |
Command |
|
Display uRPF configuration. |
display ip urpf interface interface-type interface-number [ slot slot-number ] |
Configuring IPv6 uRPF
About IPv6 uRPF
IPv6 Unicast Reverse Path Forwarding (uRPF) protects a network against source address spoofing attacks, such as DoS and DDoS attacks.
IPv6 uRPF application scenario
Attackers send packets with a forged source address to access a system that uses IPv6-based authentication, in the name of authorized users or even the administrator. Even if the attackers or other hosts cannot receive any response packets, the attacks are still disruptive to the attacked target.
Figure 3 Source address spoofing attack
As shown in Figure 3, an attacker on Router A sends the server (Router B) requests with a forged source IPv6 address 2000::1 at a high rate. Router B sends response packets to IPv6 address 2000::1 (Router C). Consequently, both Router B and Router C are attacked. If the administrator disconnects Router C by mistake, the network service is interrupted.
Attackers can also send packets with different forged source addresses or attack multiple servers simultaneously to block connections or even break down the network.
IPv6 uRPF can prevent these source address spoofing attacks. It checks whether an interface that receives a packet is the output interface of the FIB entry that matches the source address of the packet. If not, IPv6 uRPF considers it a spoofing attack and discards the packet.
IPv6 uRPF check modes
IPv6 uRPF supports strict and loose check modes.
Strict IPv6 uRPF check
To pass strict IPv6 uRPF check, the source address of a packet and the receiving interface must match the destination address and output interface of an IPv6 FIB entry. In some scenarios (for example, asymmetrical routing), strict IPv6 uRPF might discard valid packets.
Strict IPv6 uRPF is often deployed between a PE and a CE.
Loose IPv6 uRPF check
To pass loose IPv6 uRPF check, the source address of a packet must match the destination address of an IPv6 FIB entry. Loose IPv6 uRPF can avoid discarding valid packets, but might let go attack packets.
Loose IPv6 uRPF is often deployed between ISPs, especially in asymmetrical routing.
IPv6 uRPF extended functions
Using the default route in IPv6 uRPF check
When a default route exists, all packets that fail to match a specific IPv6 FIB entry match the default route during IPv6 uRPF check and thus are permitted to pass. If you allow using the default route (by using allow-default-route), IPv6 uRPF permits packets that only match the default route.
By default, IPv6 uRPF discards packets that can only match a default route. Typically, you do not need to configure the allow-default-route keyword on a PE device because it has no default route pointing to the CE device. If you enable IPv6 uRPF on a CE interface and the CE interface has a default route pointing to the PE, specify the allow-default-route keyword.
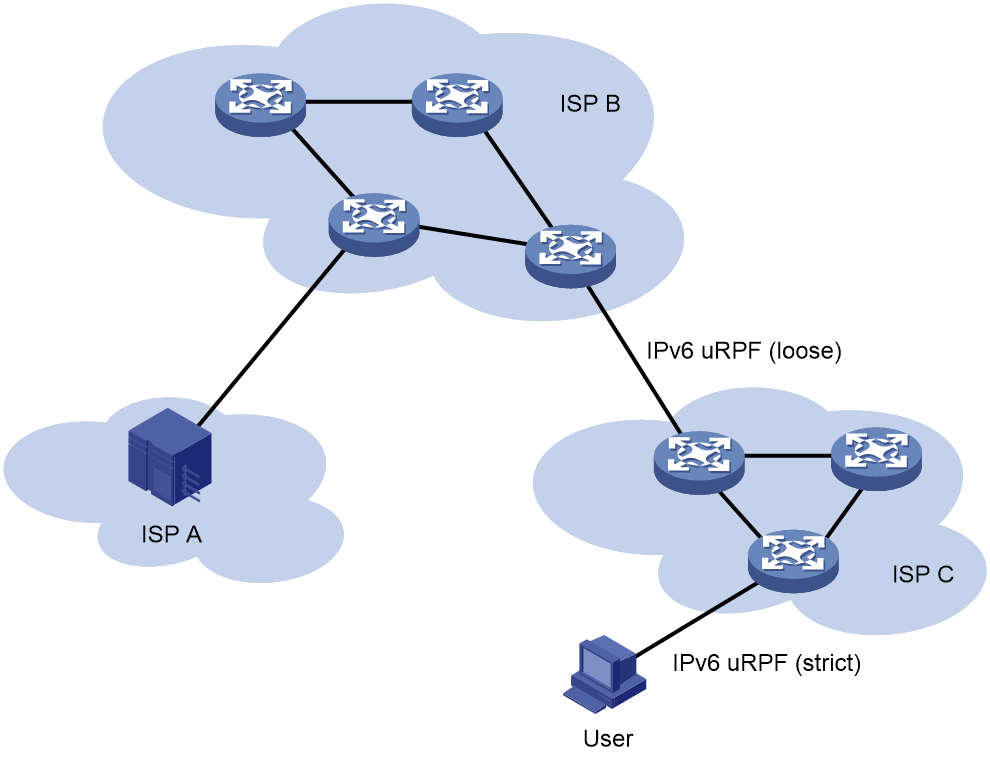
Network application
As shown in Figure 4, strict IPv6 uRPF check is configured between an ISP network and a customer network. Loose IPv6 uRPF check is configured between ISPs.
Restrictions and guidelines: IPv6 uRPF configuration
If you enable IPv6 uRPF on an interface, you can use the display ipv6 interface command to view statistics about packets discarded by IPv6 uRPF (displayed as "Drops" and "Suppressed drops").
Do not configure the allow-default-route keyword for loose IPv6 uRPF check. Otherwise, IPv6 uRPF might fail to work.
Do not configure both strict IPv6 uRPF check and loose uRPF check, or loose IPv6 uRPF check and strict uRPF check on an interface.
Do not use strict IPv6 uRPF if ECMP routing is available in the network. Service packets that travel along ECMP routes cannot pass the strict uRPF check and will be dropped.
Enabling IPv6 uRPF on an interface
1. Enter system view.
system-view
2. Enter Layer 3 interface view.
interface interface-type interface-number
3. Enable IPv6 uRPF.
ipv6 urpf { loose | strict } [ allow-default-route ]
By default, IPv6 uRPF is disabled.
Display and maintenance commands for IPv6 uRPF
Execute display commands in any view.
|
Task |
Command |
|
Display IPv6 uRPF configuration. |
display ipv6 urpf interface interface-type interface-number [ slot slot-number ] |