- Table of Contents
-
- 07-Layer 3—IP Services Configuration Guide
- 00-Preface
- 01-ARP configuration
- 02-IP addressing configuration
- 03-DHCP configuration
- 04-DNS configuration
- 05-NAT configuration
- 06-NAT66 configuration
- 07-IP forwarding basics configuration
- 08-Fast forwarding configuration
- 09-Multi-CPU packet distribution configuration
- 10-Adjacency table configuration
- 11-IRDP configuration
- 12-IP performance optimization configuration
- 13-UDP helper configuration
- 14-IPv6 basics configuration
- 15-DHCPv6 configuration
- 16-IPv6 fast forwarding configuration
- 17-AFT configuration
- 18-Tunneling configuration
- 19-GRE configuration
- 20-ADVPN configuration
- 21-WAAS configuration
- 22-Lighttpd service configuration
- 23-Web caching configuration
- 24-STUN configuration
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 05-NAT configuration | 772.10 KB |
Contents
Destination address translation
Device access with overlapping addresses
Configuring outbound bidirectional NAT for internal-to-external access through domain name
Configuring interface-based NAT
Restrictions and guidelines: interface-based NAT configuration
Interface-based NAT tasks at a glance
Configuring static NAT on an interface
Restrictions and guidelines for static NAT configuration on an interface
Configuring outbound one-to-one static NAT
Configuring outbound net-to-net static NAT
Configuring object group-based outbound static NAT
Configuring inbound one-to-one static NAT
Configuring inbound net-to-net static NAT
Configuring object group-based inbound static NAT
Configuring dynamic NAT on an interface
Restrictions and guidelines dynamic NAT configuration on an interface
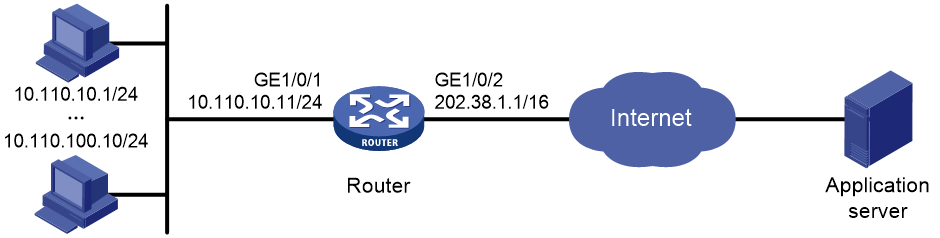
Configuring outbound dynamic NAT
Configuring inbound dynamic NAT
Configuring NAT server mappings on an interface
Restrictions and guidelines for NAT server mapping configuration on an interface
Configuring common NAT server mappings
Configuring load sharing NAT server mappings
Configuring ACL-based NAT server mappings
Configuring NAT444 on an interface
Restrictions and guidelines for NAT444 configuration on an interface
Configuring static port block mapping for NAT444
Configuring dynamic port block mapping for NAT444
Enabling port block global sharing
Configuring DS-Lite B4 address translation on an interface
Configuring the HA group for NAT
Configuring the HA group in active/standby mode for interface-based NAT
Configuring the HA group in dual-active mode for interface-based NAT
Enabling sending ICMP error messages for NAT failures
Configuring NAT session logging
Configuring NAT444 user logging
Enabling logging for IP usage of a NAT address group in NO-PAT mode
Configuring NAT in specific networks
Enabling NAT reply redirection
Enabling the deletion of timestamps in TCP SYN and SYN ACK packets
Enabling NAT session recreation after link switchover
Display and maintenance commands for NAT
Example: Configuring outbound one-to-one static NAT
Example: Configuring outbound dynamic NAT (non-overlapping addresses)
Example: Configuring outbound bidirectional NAT
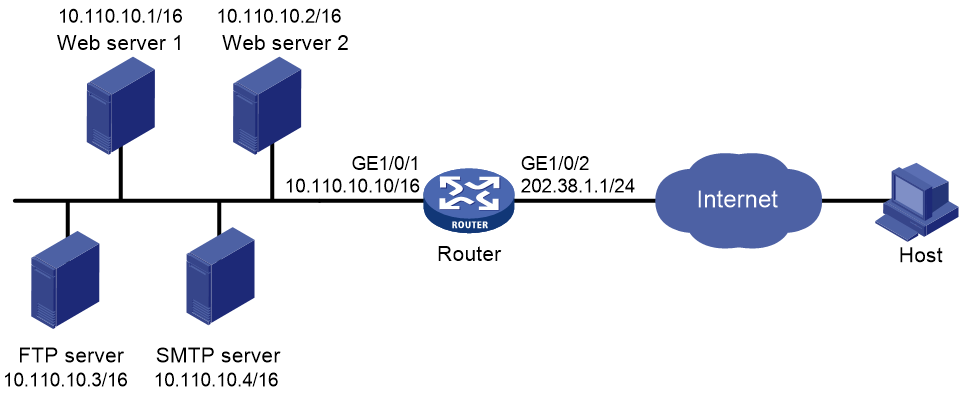
Example: Configuring NAT Server for external-to-internal access
Example: Configuring NAT Server for external-to-internal access through domain name
Example: Configuring NAT server for external-to-internal access through domain name
Example: Configuring NAT hairpin in C/S mode
Example: Configuring NAT hairpin in P2P mode
Example: Configuring twice NAT
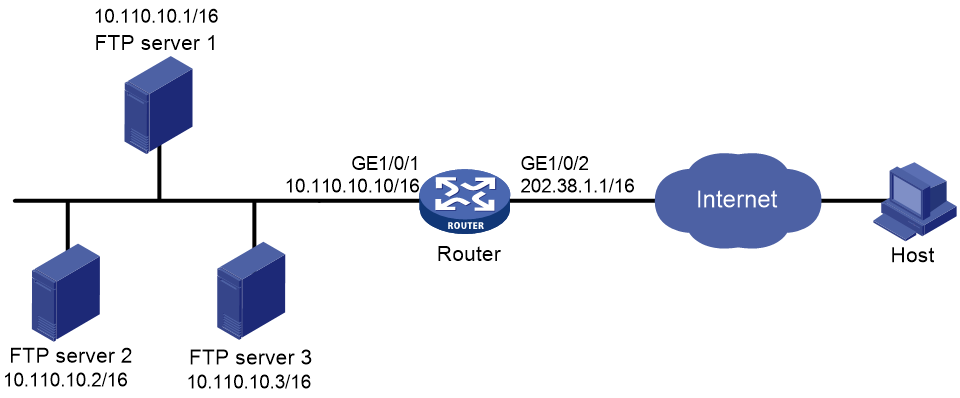
Example: Configuring load sharing NAT Server
Example: Configuring NAT DNS mapping
Example: Configuring static port block mapping for NAT444
Example: Configuring dynamic port block mapping for NAT444
Example: Configuring DS-Lite B4 address translation
Example: Configuring NAT444 gateway unified with portal user authentication
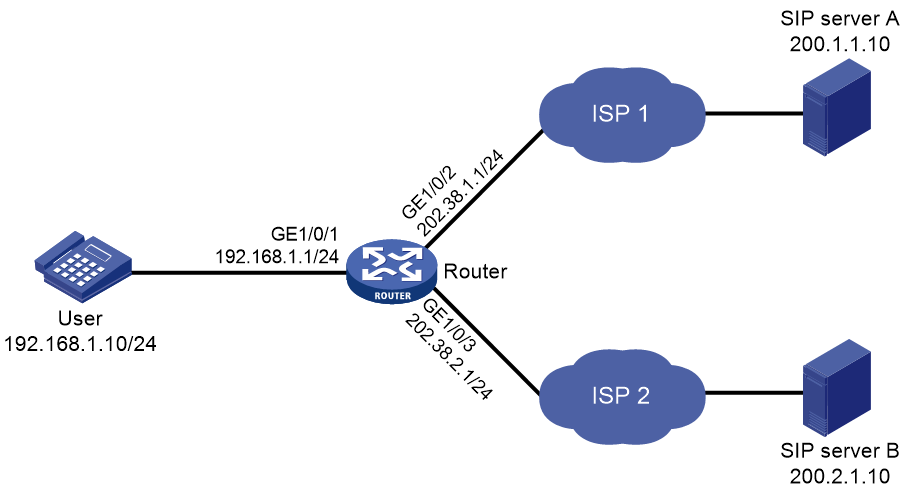
Example: Configuring SIP on a network with two output interfaces
NAT overview
Network Address Translation (NAT) translates an IP address in the IP packet header to another IP address. Typically, NAT is configured on gateways to enable private hosts to access external networks and external hosts to access private network resources such as a Web server.
Restrictions and guidelines
The global NAT policy has priority over interface-based NAT. If both are configured, a packet is translated based on the global NAT policy when the packet matches an ACL rule in the global NAT policy. The interface-based source and destination address translation rules do not take effect. As a best practice, do not configure the global NAT and interface-based NAT policies both.
A NATed packet will not be AFTed.
Basic NAT concepts
The following describes basic NAT concepts:
· NAT device—A device configured with NAT. Typically, NAT is configured on the edge device that connects the internal and external networks.
· NAT interface—An interface configured with NAT.
· NAT rule—Rules that define how to perform address translation.
· NAT address—A public IP address used for address translation, and this address is reachable from the external network. The NAT address can be manually assigned or dynamically obtained.
· NAT entry—Stores the mapping between a private IP address and a public IP address. For more information, see "NAT entries."
· Easy IP—Uses the IP address of an interface as the NAT address. The IP address of the interface can be manually assigned or be obtained through DHCP or PPPoE.
· Global NAT—Uses NAT rules configured for the global NAT policy to translate packets.
· Interface-based NAT—Uses NAT rules configured on a per interface basis to translate packets.
Basic NAT operating mechanism
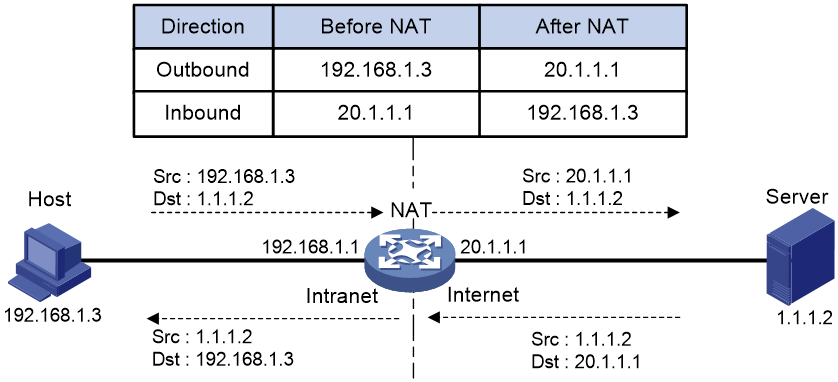
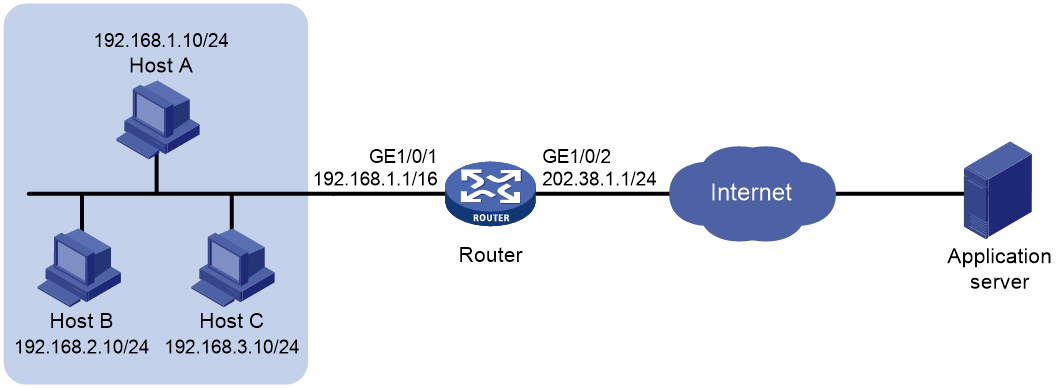
Figure 1 shows the basic NAT operating mechanism.
2. Upon receiving a response from the server, NAT translates the destination public address to the private address, and forwards the packet to the host.
The NAT operation is transparent to the terminals (the host and the server). NAT hides the private network from the external users and shows that the IP address of the internal host is 20.1.1.1.
NAT control
You can use ACLs to implement NAT control. The match criteria in the ACLs include the source IP address, source port number, destination IP address, destination port number, transport layer protocol, and VPN instance. Only packets permitted by an ACL are processed by NAT.
NAT translation methods
Static NAT
Static NAT creates a fixed mapping between a private address and a public address. It supports connections initiated from internal users to external network and from external users to the internal network. Static NAT applies to regular communications.
Source address translation
Source address translation is dynamic NAT translation that uses an address pool to translate addresses. It applies to the scenario where a large number of internal users access the external network.
The NO-PAT, port-based PAT, and port block-based PAT modes are supported.
NO-PAT
Not Port Address Translation (NO-PAT) translates a private IP address to an IP public address. The public IP address cannot be used by another internal host until it is released.
NO-PAT supports all IP packets.
Port-based PAT
Port Address Translation (PAT) translates multiple private IP addresses to a single public IP address by mapping the private IP address and source port to the public IP address and a unique port. PAT supports TCP and UDP packets, and ICMP request packets.
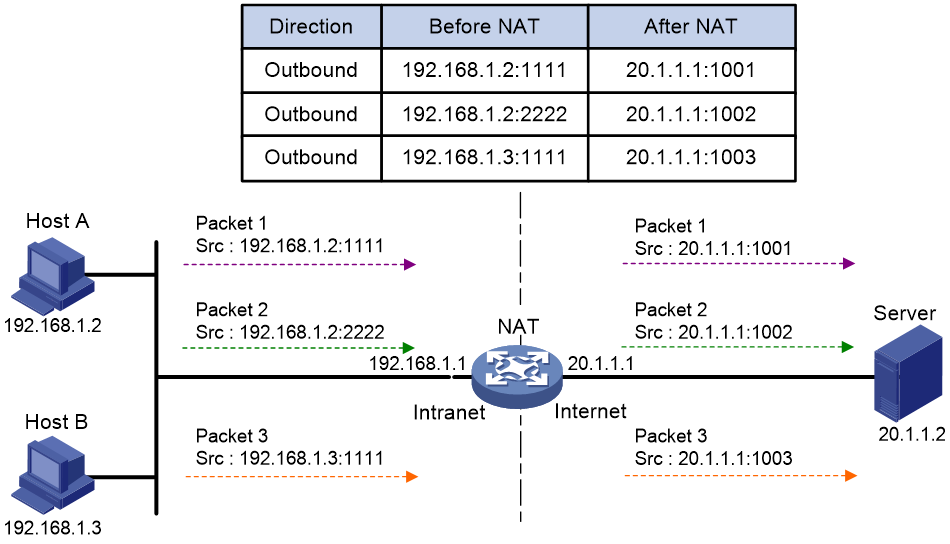
Figure 2 PAT operation
As shown in Figure 2, PAT translates the source IP addresses of the three packets to the same IP public address and translates their port numbers to different port numbers. Upon receiving a response, PAT translates the destination address and port number of the response, and forwards it to the target host.
PAT supports the following mappings:
· Endpoint-Independent Mapping (EIM)—Uses the same IP and port mapping (EIM entry) for packets from the same source IP and port to any destinations. EIM allows external hosts to initiate connections to the translated IP addresses and ports of internal hosts. It allows internal hosts behind different NAT gateways to access each other.
· Address and Port-Dependent Mapping (APDM)—Uses different IP and port mappings for packets from the same source IP and port to different destination IP addresses and ports. APDM allows an external host to initiate connections to an internal host only under the condition that the internal host has previously accessed the external host. It is secure, but it does not allow internal hosts behind different NAT gateways to access each other.
Port block-based NAT
Port block-based NAT is a PAT translation based on port ranges. It maps multiple private IP addresses to one public IP address and uses a different port block for each private IP address. For example, the private IP address 10.1.1.1 of an internal host is mapped to the public IP address 202.1.1.1 and port block 10001 to 10256. When the internal host accesses public hosts, the source IP address 10.1.1.1 is translated to 202.1.1.1, and the source ports are translated to ports in the port block 10001 to 10256.
Port block-based NAT includes static and dynamic mappings. It applies to NAT444 and DS-Lite networks.
Static port block mapping
The NAT gateway computes a static port block mapping before address translation. The mapping is between a private IP address and a public IP address with a port block.
When an internal user initiates a connection to the external network, the system performs the following operations:
· Locates a static mapping based on the private IP address of the user and obtains the public IP address and the port block in the mapping.
· Selects a public port number in the port block.
· Translates the private IP address to the public IP address and assigns the selected public port number.
The NAT gateway uses private IP addresses, public IP addresses, a port range, and a port block size to compute static mappings:
1. Divides the port range by the port block size to get the number of available port blocks for each public IP address.
This value is the base number for mapping.
2. Sorts the port blocks in ascending order of the start port number in each block.
3. Sorts the private IP addresses and the public IP addresses separately in ascending order.
4. Maps the first base number of private IP addresses to the first public IP address and its port blocks in ascending order.
For example, the number of available port blocks of each public IP address is m. The first m private IP addresses are mapped to the first public IP address and the m port blocks in ascending order. The next m private IP addresses are mapped to the second IP address and the m port blocks in ascending order. The other static port block mappings are created by analogy.
Dynamic port block mapping
When an internal user initiates a connection to the external network, the dynamic port block-based NAT operates as follows:
1. Uses ACLs to implement translation control. It processes only packets that match an ACL permit rule.
2. Creates a mapping from the internal user's private IP address to a public IP address and a port block.
3. Translates the private IP address to the public IP address, and the source ports to ports in the selected port block for subsequent connections from the private IP address.
4. Withdraws the port block and deletes the dynamic port block mapping when all connections from the private IP address are disconnected.
Dynamic port block mapping supports port block extending. If the ports in the port block for a private address are all occupied, dynamic port block mapping translates the source port to a port in an extended port block.
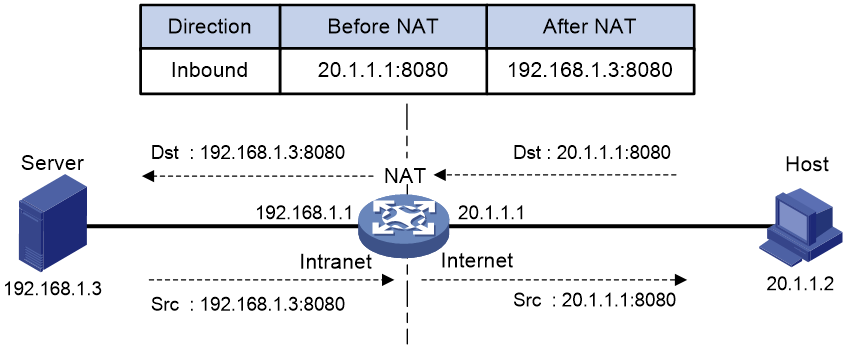
Destination address translation
Destination address translation maps a public address and port number to the private IP address and port number of an internal server. This feature allows servers in the private network to provide services for external users.
Figure 3 shows how destination address translation works:
1. Upon receiving a request from the host, NAT translates the public destination IP address and port number to the private IP address and port number of the internal server.
2. Upon receiving a response from the server, NAT translates the private source IP address and port number to the public IP address and port number.
Figure 3 Destination address translation operation
NAT entries
NAT session entry
NAT creates a NAT session entry for a session and creates an address mapping for the first packet in the session.
A NAT session entry contains extended NAT information, such as interface and translation method. Subsequent packets of the session are translated by using this entry.
· If the direction of the subsequent packets is the same as the direction of the first translated packet, NAT performs the source and destination address translation the same as the first packet.
· If the direction of the subsequent packets is opposite to the direction of the first translated packet, NAT perform reverse address translation. For example, if the source address of the first packet is translated, then the destination address of the subsequent packets is translated.
The session management module maintains the updating and aging of NAT session entries. For information about session management, see Security Configuration Guide.
EIM entry
If EIM is configured on the NAT device, the PAT mode will first create a NAT session entry, and then an EIM entry. The EIM entry is a 3-tuple entry, and it maps a private address/port to a public address/port. The EIM entry ensures:
· Subsequent new connections originating from the same source IP and port uses the same translation as the initial connection.
· Translates the address for new connections initiated from external hosts to the NAT address and port number based on the EIM entry.
An EIM entry ages out after all related NAT session entries age out.
NO-PAT entry
A NO-PAT entry maps a private address to a public address. The same mapping applies to subsequent connections originating from the same source IP.
A NO-PAT entry can also be created during the ALG process for NAT. For information about NAT ALG, see "NAT ALG."
A NO-PAT entry ages out after all related NAT session entries age out.
Port block-based entry
A port block-based entry maps a private IP address to a public IP address and a port block.
Port block-based entries include static and dynamic port block mappings. For information about these mappings, see "Static port block mapping" and "Dynamic port block mapping."
VRF-aware NAT
VRF-aware NAT allows users from different VRF (VPN instances) to access external networks and to access each other.
1. Upon receiving a request from a user in a VRF to an external network, NAT performs the following tasks:
¡ Translates the private source IP address and port number to a public IP address and port number.
¡ Records the VRF information, such as the VRF name.
2. When a response packet arrives, NAT performs the following tasks:
¡ Translates the destination public IP address and port number to the private IP address and port number.
¡ Forwards the packet to the target VRF.
The NAT Server feature supports VRF-aware NAT for external users to access the servers in a VPN instance. For example, to enable a host at 10.110.1.1 in VPN 1 to provide Web services for Internet users, configure NAT Server to use 202.110.10.20 as the public IP address of the Web server.
VRF-aware NAT is supported only in the global NAT policy in the current software version.
NAT hairpin
NAT hairpin allows internal hosts to access each other through NAT. The source and destination IP address of the packets are translated on the interface connected to the internal network.
NAT hairpin includes P2P and C/S modes:
· P2P—Allows internal hosts to access each other through NAT. The internal hosts first register their public addresses to an external server. Then, the hosts communicate with each other by using the registered IP addresses.
· C/S—Allows internal hosts to access internal servers through NAT addresses.
NAT ALG
NAT ALG (Application Level Gateway) translates address or port information in the application layer payloads to ensure connection establishment.
For example, an FTP application includes a data connection and a control connection. The IP address and port number for the data connection depend on the payload information of the control connection. This requires NAT ALG to translate the address and port information for data connection establishment.
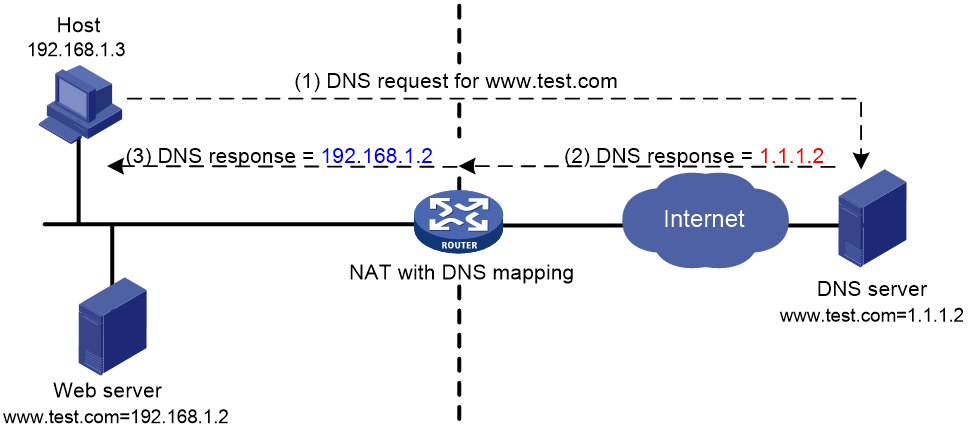
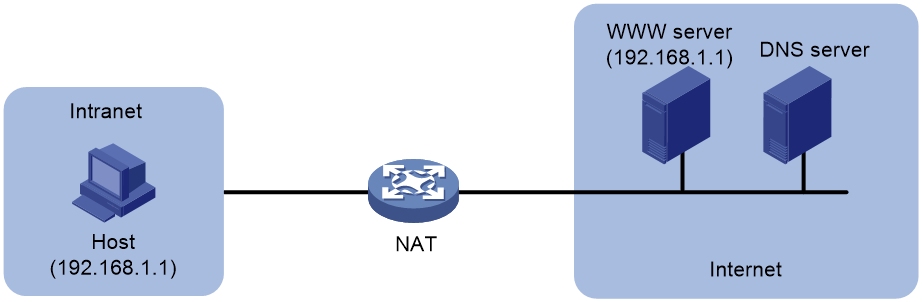
NAT DNS mapping
The DNS server is typically on the public network. For the users on the public network to access an internal server, you can configure the NAT Server feature on the NAT device. The NAT Server maps the public IP address and port number to the private IP address and port number of the internal server. Then the public users can access the internal server through the server's domain name or public IP address.
When a user is in the private network, the user cannot access the internal server by using the domain name of the server. This is because the DNS response contains the public IP address of the server. In this case, you can configure NAT DNS mapping to solve the problem.
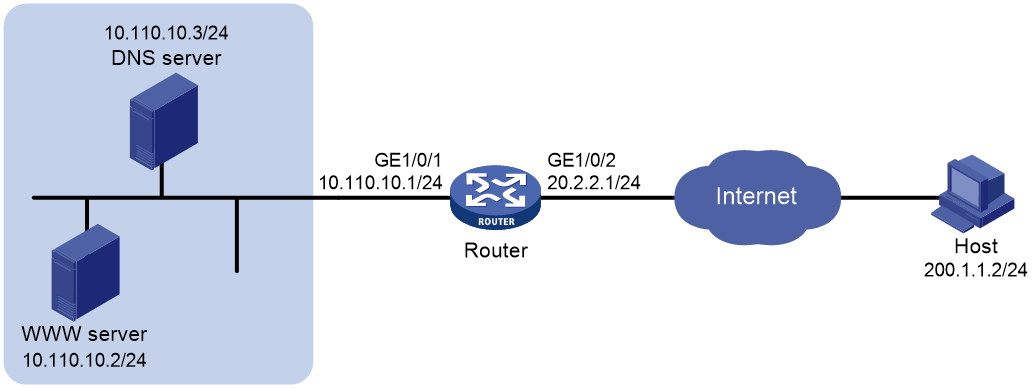
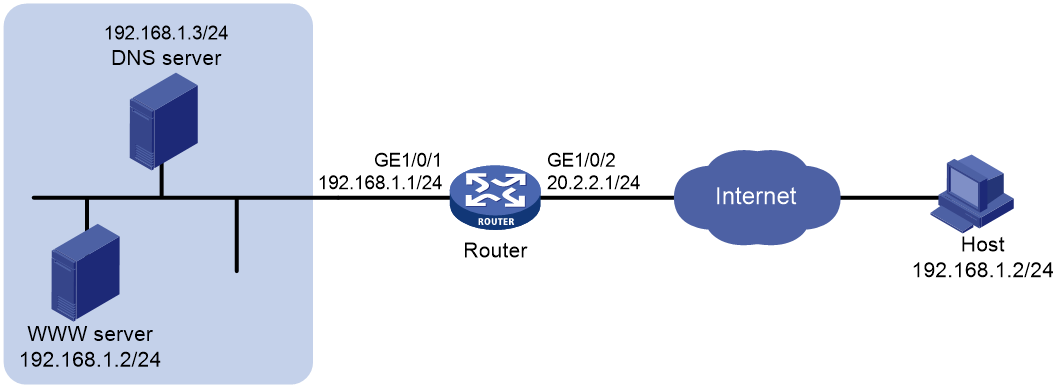
As shown in Figure 4, NAT DNS mapping works as follows:
1. The host sends a DNS request containing the domain name of the internal Web server.
2. Upon receiving the DNS response, the NAT device performs a DNS mapping lookup by using the domain name in the response. A NAT DNS mapping maps the domain name to the public IP address, public port number, and the protocol type for the internal server.
3. If a match is found, the NAT continues to compare the public address, public port number, and the protocol type with the NAT Server configuration. The NAT Server configuration maps the public IP address and port number to the private IP address and port number for the internal server.
4. If a match is found, NAT translates the public IP address in the response into the private IP address of the Web server.
5. The internal host receives the DNS response, and obtains the private IP address of the Web server.
NAT444
About NAT444
NAT444 provides carrier-grade NAT by unifying the NAT444 gateway, AAA server, and log server. NAT444 introduces a second layer of NAT on the carrier side, with few changes on the customer side and the application server side. With port block assignment, NAT444 supports user tracking. It has become a preferred solution for carriers in transition to IPv6.
The NAT444 solution can be centralized and distributed deployment.
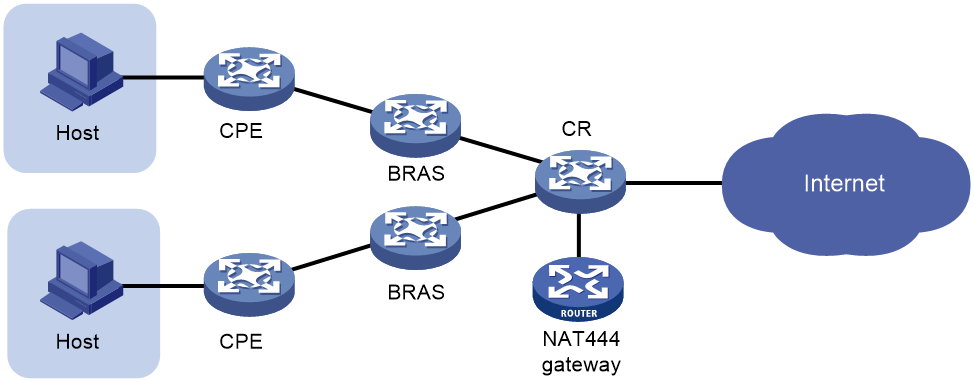
Centralized NAT444 deployment
Centralized NAT444 deployment is implemented by installing a NAT processing slot on the CR device or by connecting a NAT444 device to the CR.
As shown in Figure 5, when an internal user accesses the external network, NAT444 is implemented as follows:
1. The CPE device performs the first NAT.
2. After the user passes AAA authentication on the BRAS device, this user is assigned a private IP address.
3. When the packet destined to the external network, the NAT444 gateway performs the second NAT.
Figure 5 Centralized NAT444 deployment
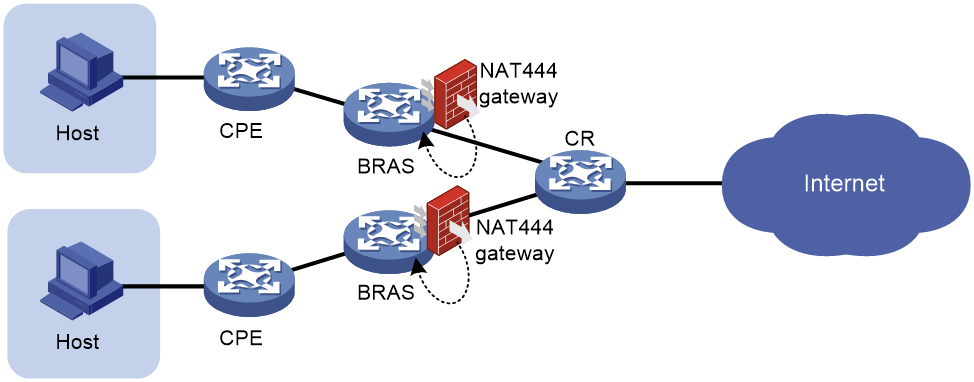
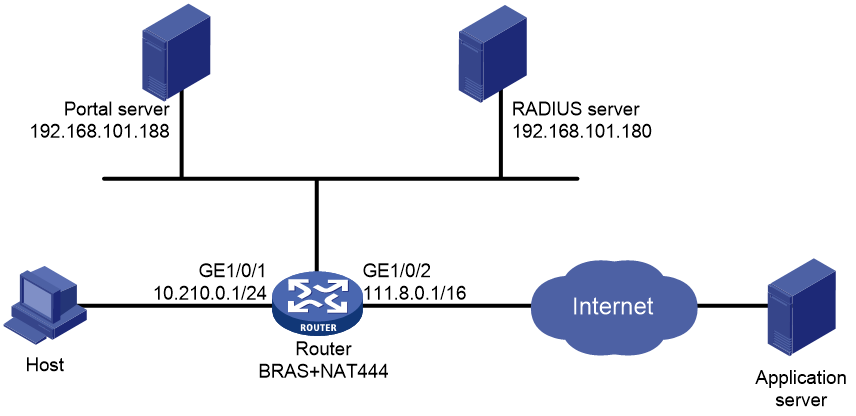
Distributed NAT444 deployment
Distributed NAT444 deployment is implemented by installing a NAT processing slot on the BRAS device. This deployment also requires the unification of NAT444 gateway and the BRAS device. To unify the NAT444 gateway and BRAS device, specify the user address type in the ISP domain.
As shown in Figure 6, the NAT444 gateway and BRAS device function as follows after the unification:
1. After a user passes authentication and obtains a private address, the NAT444 gateway immediately assigns a public IP address and a port block to the user.
If the NAT444 resources have been used up, the BRAS logs off the user, which ensures accurate accounting on the AAA server.
2. The NAT444 gateway sends the port block mapping to the BRAS device.
3. The BRAS device records the mapping and reports it to the AAA server.
The AAA server maintains one mapping for each online user until the user goes offline. The unification ensures that the AAA server maintains mappings for all users and provides user tracing without requiring an extra log server.
Only the unification between the NAT444 gateway and the PPP service is supported in the current software version.
Figure 6 Distributed NAT444 deployment
Device access with overlapping addresses
Configuring twice NAT
As shown in Figure 7, two hosts are in different VPN instances with overlapping addresses. For the hosts to access each other, both the source and destination addresses of packets between the two VPNs need to be translated. Configure static NAT on both interfaces connected to the VPNs on the NAT device.
1. Configure a static outbound NAT mapping between 192.168.1.1 in VPN 1 and 172.16.1.1 in VPN 2.
2. Configure a static outbound NAT mapping between 192.168.1.1 in VPN 2 and 172.16.2.1 in VPN 1.
3. When the twice NAT takes effect, the hosts can access each other.
Figure 7 VPN access with overlapping address
Configuring outbound bidirectional NAT for internal-to-external access through domain name
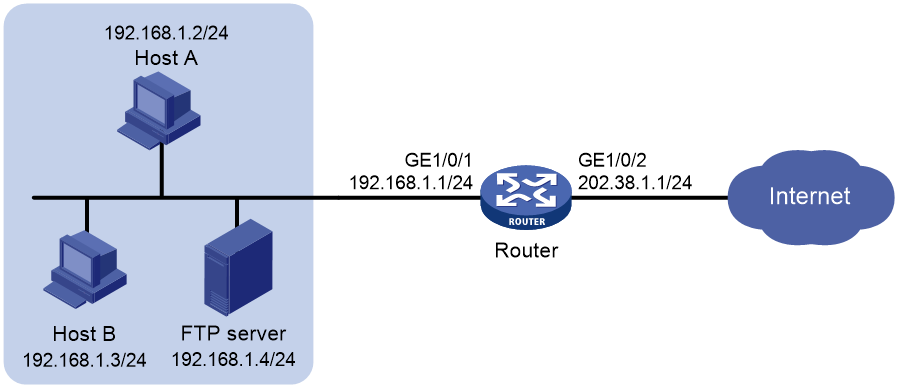
As shown in Figure 8, the IP address of the Web server overlaps with the private host at 192.168.1.0/24. Configure dynamic NAT ALG and outbound dynamic NAT to allow the internal host to access the external Web server by using the server's domain name.
1. The host sends a DNS request to the DNS server in the external network.
2. After receiving a DNS reply, the NAT device with NAT ALG configured translates the Web server's IP address in the DNS reply payload to a dynamically assigned public address 10.1.1.1.
3. Configure inbound dynamic NAT ALG to make sure the internal host reaches the Web server instead of another internal host. NAT ALG can translate the Web server's IP address in the DNS reply payload to a dynamically assigned public address 10.1.1.1.
4. After receiving the DNS reply from the NAT device, the host sends a packet with the source IP address 192.168.1.1 and destination IP address 10.1.1.1.
5. The NAT device with outbound dynamic NAT configured translates the source IP address of the packet to a dynamically assigned public address 20.1.1.1. NAT ALG translates the destination IP address of the packet to the IP address of the Web server.
Figure 8 Internal-to-external access through domain name
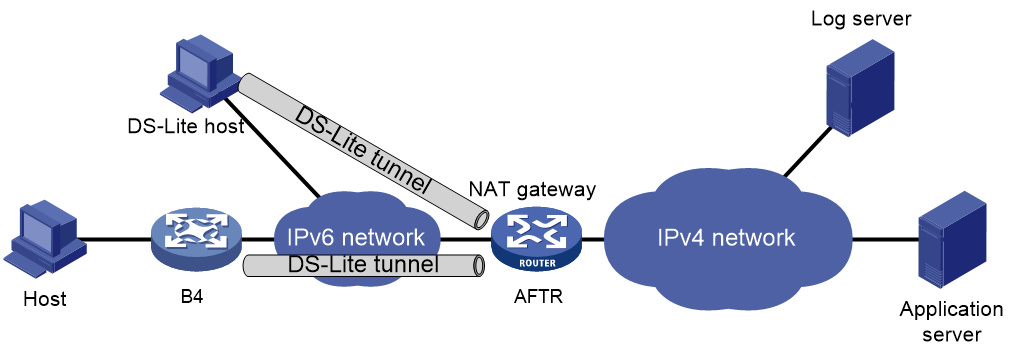
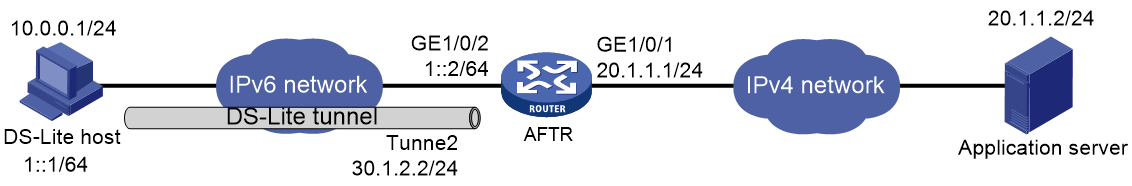
NAT in the DS-Lite network
DS-Lite combines tunneling and NAT to allow an IPv4 private network to access the IPv4 public network over an IPv6 network. For more information about DS-Lite, see "Configuring tunneling."
DS-Lite B4 address translation is configured on the AFTR and performs port block-based translation based on the IPv6 address of the B4 element. The B4 element refers to a B4 router or a DS-Lite host. DS-Lite B4 address translation dynamically maps a public IPv4 address and a port block to the IPv6 address of the B4 element. The DS-Lite host or hosts behind the B4 router use the mapped public IPv4 address and port block to access the public IPv4 network.
DS-Lite B4 address translation supports user tracing for DS-Lite hosts based on the port block.
Only dynamic port block mapping is supported for B4 address translation.
Figure 9 DS-Lite B4 address translation
Configuring interface-based NAT
Restrictions and guidelines: interface-based NAT configuration
The general restrictions and guidelines are as follows:
· You can use an ACL in a NAT rule to identify the IP addresses to be translated. The match criteria include the source IP address, source port number, destination IP address, destination port number, transport layer protocol, and VPN instance.
· If NAT is configured on only one output interface in a dual uplink network, do not add the two output interfaces to the same security zone. Doing so will cause communication interruption. For more information about security zone, see Security Configuration Guide.
· If you perform all the translation methods on an interface, the NAT rules are sorted in the following descending order:
a. NAT Server.
b. Static NAT.
c. NAT444 static port blocking mapping.
d. Dynamic NAT, NAT444 dynamic port block mapping, and DS-Lite B4 address translation.
Dynamic NAT, NAT444 dynamic port block mapping, and DS-Lite B4 address translation have the same priority. Dynamic NAT rules and NAT444 dynamic port block mapping rules are sorted in descending order of ACL numbers and are effective for IPv4 packets. DS-Lite B4 address translation rules are effective for IPv6 packets.
When you configure BRAS unification, follow these restrictions and guidelines:
· Supported user address types are private IPv4 address, private-DS address, and DS-Lite address.
· If the NAT444 configuration changes after users get online, the public IP addresses and port numbers used by the users also change. The change cannot be synchronized to the AAA server, affecting user tracing accuracy. As a best practice, log off the users immediately after you change the NAT444 configuration. When the users come online again, NAT444 creates new mappings for them.
Interface-based NAT tasks at a glance
To configure NAT, perform the following tasks:
1. Configuring an address translation method on an interface
¡ Configuring static NAT on an interface
¡ Configuring dynamic NAT on an interface
¡ Configuring NAT server mappings on an interface
¡ Configuring NAT444 on an interface
¡ Configuring DS-Lite B4 address translation on an interface
2. (Optional.) Configuring NAT hairpin
3. (Optional.) Configuring NAT ALG
4. (Optional.) Configuring NAT DNS mapping
5. (Optional.) Configuring high availability for NAT
¡ Configuring the HA group for NAT
¡ Enabling sending ICMP error messages for NAT failures
6. (Optional.) Configuring NAT logging
7. (Optional.) Configuring NAT in specific networks
¡ Enabling NAT reply redirection
¡ Enabling the deletion of timestamps in TCP SYN and SYN ACK packets
¡ Enabling NAT session recreation after link switchover
Configuring static NAT on an interface
Restrictions and guidelines for static NAT configuration on an interface
Typically, configure inbound static NAT with outbound dynamic NAT, NAT Server, or outbound static NAT to implement source address translation and destination address translation.
Prerequisites
Before configuring static NAT, you must perform the following tasks:
· Configure an ACL to identify the IP addresses to be translated. For more information about ACLs, see ACL and QoS Configuration Guide.
· Manually add a route for inbound static NAT. Use local-ip or local-network as the destination address, and use global-ip, an address in global-network, or the next hop directly connected to the output interface as the next hop.
Configuring outbound one-to-one static NAT
About this task
For address translation from a private IP address to a public IP address, configure outbound one-to-one static NAT on the interface connected to the external network.
· When the source IP address of an outgoing packet matches the local-ip, the source IP address is translated into the global-ip.
· When the destination IP address of an incoming packet matches the global-ip, the destination IP address is translated into the local-ip.
Restrictions and guidelines
If multiple outbound one-to-one static mappings uses different ACL rules, you can map a private address to different public addresses.
If you do not specify the acl keyword for a one-to-one mapping NAT rule, the rule can process reversible traffic. If the acl keyword is specified for the NAT rule, you must specify the reversible keyword for the rule to process reversible traffic.
Procedure
1. Enter system view.
system-view
2. Configure a one-to-one mapping for outbound static NAT.
nat static outbound local-ip [ vpn-instance local-vpn-instance-name ] global-ip [ vpn-instance global-vpn-instance-name ] [ acl { ipv4-acl-number | name ipv4-acl-name } [ reversible ] ] [ vrrp virtual-router-id ] [ rule rule-name ] [ priority priority ] [ disable ] [ counting ] [ packet-type-ignore ] [ description text ]
3. (Optional.) Rearrange outbound one-to-one mapping NAT rules to adjust their priorities.
nat static outbound rule move nat-rule-name1 { after | before } nat-rule-name2
4. Enter interface view.
interface interface-type interface-number
5. Enable static NAT on the interface.
nat static enable
By default, static NAT is disabled.
Configuring outbound net-to-net static NAT
About this task
For address translation from a private network to a public network, configure outbound net-to-net static NAT on the interface connected to the external network.
· When the source IP address of an outgoing packet matches the private address range, the source IP address is translated into a public address in the public address range.
· When the destination IP address of an incoming packet matches the public address range, the destination IP address is translated into a private address in the private address range.
Procedure
1. Enter system view.
system-view
2. Configure a net-to-net mapping for outbound static NAT.
nat static outbound net-to-net local-start-address local-end-address [ vpn-instance local-vpn-instance-name ] global global-network { mask-length | mask } [ vpn-instance global-vpn-instance-name ] [ acl { ipv4-acl-number | name ipv4-acl-name } [ reversible ] ] [ vrrp virtual-router-id ] [ rule rule-name ] [ priority priority ] [ disable ] [ counting ]
3. (Optional.) Change the priority of the outbound net-to-net static NAT rule.
nat static outbound net-to-net rule move nat-rule-name1 { after | before } nat-rule-name2
By default, an outbound net-to-net static NAT rule appearing earlier on the rule list has a higher priority for packet matching.
4. Enter interface view.
interface interface-type interface-number
5. Enable static NAT on the interface.
nat static enable
By default, static NAT is disabled.
Configuring object group-based outbound static NAT
About this task
Configure object group-based outbound static NAT on the interface connected to the external network to translate private IP addresses into public IP addresses.
· When the source address of an outgoing packet matches the private address object group, the source address is translated into a public address in the public address object group.
· When the destination address of an incoming packet matches the public address object group, the destination address is translated into a private address in the private address object group.
Restrictions and guidelines
If you specify the acl keyword, NAT processes only packets permitted by the ACL.
For an object group-based outbound static NAT mapping to take effect, make sure the following requirements are met:
· One address object group contains only one host object or subnet object.
· A subnet object cannot have excluded addresses.
Procedure
1. Enter system view.
system-view
2. Configure an object group-based outbound static NAT mapping.
nat static outbound object-group local-object-group-name [ vpn-instance local-vpn-instance-name ] object-group global-object-group-name [ vpn-instance global-vpn-instance-name ] [ acl { ipv4-acl-number | name ipv4-acl-name } [ reversible ] ] [ vrrp virtual-router-id ] [ disable ] [ counting ]
By default, no mappings exist.
3. Enter interface view.
interface interface-type interface-number
4. Enable static NAT on the interface.
nat static enable
By default, static NAT is disabled.
Configuring inbound one-to-one static NAT
About this task
For address translation from a public IP address to a private IP address, configure inbound one-to-one static NAT.
· When the source IP address of an incoming packet matches the global-ip, the source IP address is translated into the local-ip.
· When the destination IP address of an outgoing packet matches the local-ip, the destination IP address is translated into the global-ip.
Procedure
1. Enter system view.
system-view
2. Configure a one-to-one mapping for inbound static NAT.
nat static inbound global-ip [ vpn-instance global-vpn-instance-name ] local-ip [ vpn-instance local-vpn-instance-name ] [ acl { ipv4-acl-number | name ipv4-acl-name } [ reversible ] ] [ rule rule-name ] [ priority priority ] [ disable ] [ counting ] [ packet-type-ignore ] [ description text ]
3. Enter interface view.
interface interface-type interface-number
4. Enable static NAT on the interface.
nat static enable
By default, static NAT is disabled.
Configuring inbound net-to-net static NAT
About this task
For address translation from a public network to a private network, configure inbound net-to-net static NAT.
· When the source IP address of an incoming packet matches the public address range, the source IP address is translated into a private address in the private address range.
· When the destination IP address of an outgoing packet matches the private address range, the destination IP address is translated into a public address in the public address range.
Procedure
1. Enter system view.
system-view
2. Configure a net-to-net mapping for inbound static NAT.
nat static inbound net-to-net global-start-address global-end-address [ vpn-instance global-vpn-instance-name ] local local-network { mask-length | mask } [ vpn-instance local-vpn-instance-name ] [ acl { ipv4-acl-number | name ipv4-acl-name } [ reversible ] ] [ rule rule-name ] [ priority priority ] [ disable ] [ counting ]
3. (Optional.) Change the priority of the inbound net-to-net static NAT rule.
nat static inbound net-to-net rule move nat-rule-name1 { after | before } nat-rule-name2
By default, an inbound net-to-net static NAT rule appearing earlier on the rule list has a higher priority for packet matching.
4. Enter interface view.
interface interface-type interface-number
5. Enable static NAT on the interface.
nat static enable
By default, static NAT is disabled.
Configuring object group-based inbound static NAT
About this task
Configure object group-based inbound static NAT to translate public IP addresses into private IP addresses.
· When the destination address of an outgoing packet matches the private address object group, the destination address is translated into a public address in the public address object group.
· When the source address of an incoming packet matches the public address object group, the source address is translated into a private address in the private address object group.
Restrictions and guidelines
If you specify the acl keyword, NAT processes only packets permitted by the ACL.
For an object group-based inbound static NAT mapping to take effect, make sure the following requirements are met:
· One address object group contains only one host object or subnet object.
· A subnet object cannot have excluded addresses.
For an inbound static mapping, if its private IPv4 object group contains a host address, the host address cannot be on the same subnet as the interface configured with this mapping.
Procedure
1. Enter system view
system-view
2. Configure an object group-based inbound static NAT mapping.
nat static inbound object-group global-object-group-name [ vpn-instance global-vpn-instance-name ] object-group local-object-group-name [ vpn-instance local-vpn-instance-name ] [ acl { ipv4-acl-number | name ipv4-acl-name } [ reversible ] ] [ disable ] [ counting ]
By default, no NAT mappings exist.
3. Enter interface view.
interface interface-type interface-number
4. Enable static NAT on the interface.
nat static enable
By default, static NAT is disabled.
Configuring dynamic NAT on an interface
Restrictions and guidelines dynamic NAT configuration on an interface
You can configure multiple inbound or outbound dynamic NAT rules.
· A NAT rule with an ACL takes precedence over a rule without any ACL.
· If two ACL-based dynamic NAT rules are configured, the rule with the higher ACL number has higher priority.
Prerequisites
Before configuring dynamic NAT, you must perform the following tasks:
· Configure an ACL to identify the IP addresses to be translated. For more information about ACLs, see ACL and QoS Configuration Guide.
· Determine whether to enable the Easy IP feature. If you use the IP address of an interface as the NAT address, you are configuring Easy IP.
· Determine a public IP address pool for address translation.
· Determine whether to translate port numbers. Use NO-PAT to translate only IP addresses and PAT to translate both IP addresses and port numbers.
Configuring outbound dynamic NAT
About this task
To translate private IP addresses into public IP addresses, configure outbound dynamic NAT on the interface connected to the external network.
Procedure
1. Enter system view.
system-view
2. Create a NAT address group and enter its view.
nat address-group group-id [ name group-name ]
3. Add an address range to the address group.
address start-address end-address
You can add multiple address ranges to an address group.
The address ranges must not overlap.
4. Return to system view.
quit
5. Enter interface view.
interface interface-type interface-number
6. Configure outbound dynamic NAT. Choose the options to configure as needed:
¡ Configure NO-PAT.
nat outbound [ ipv4-acl-number | name ipv4-acl-name ] address-group { group-id | name group-name } [ vpn-instance vpn-instance-name ] no-pat [ reversible ] [ rule rule-name ] [ priority priority ] [ disable ] [ counting ] [ description text ]
¡ Configure PAT.
nat outbound [ ipv4-acl-number | name ipv4-acl-name ][ address-group { group-id | name group-name } ] [ vpn-instance vpn-instance-name ] [ port-preserved ] [ rule rule-name ] [ priority priority ] [ disable ] [ counting ] [ description text ]
You can configure multiple outbound dynamic NAT rules on an interface.
|
Parameter |
Description |
|
address-group |
If you do not specify this keyword, the IP address of the interface is used as the NAT address. Easy IP is implemented. |
|
no-pat reversible |
If you specify these keywords, you enable reverse address translation. Reverse address translation uses existing NO-PAT entries to translate the destination address for connections actively initiated from the external network to the internal network. The destination address is translated into the private IP address in the matching NO-PAT entry. |
7. (Optional.) Configure a PAT mapping mode.
a. Return to system view.
quit
b. Configure a PAT mapping mode.
nat mapping-behavior endpoint-independent [ acl { ipv4-acl-number | name ipv4-acl-name } ]
The default mapping mode is Address and Port-Dependent Mapping.
This command takes effect only on outbound dynamic NAT for PAT.
8. (Optional.) Rearrange outbound dynamic NAT rules to adjust their priorities.
nat outbound rule move nat-rule-name1 { after | before } nat-rule-name2
Configuring inbound dynamic NAT
Restrictions and guidelines
Do not configure inbound dynamic NAT alone. Typically, inbound dynamic NAT functions with outbound dynamic NAT, NAT Server, or outbound static NAT to implement source address translation and destination address translation.
As a best practice, manually create a route because it takes time to automatically add routes.
Procedure
1. Enter system view.
system-view
2. Create a NAT address group and enter its view.
nat address-group group-id [ name group-name ]
3. Add an address range to the address group.
address start-address end-address
You can add multiple address ranges to an address group.
The address ranges in address groups must not overlap.
4. Return to system view.
quit
5. Enter interface view.
interface interface-type interface-number
6. Configure inbound dynamic NAT.
nat inbound { ipv4-acl-number | name ipv4-acl-name } address-group { group-id | name group-name } [ vpn-instance vpn-instance-name ] [ no-pat [ reversible ] [ add-route ] ] [ rule rule-name ] [ priority priority ] [ disable ] [ counting ] [ description text ]
You can configure multiple inbound dynamic NAT rules on an interface.
|
Parameter |
Description |
|
no-pat reversible |
If you specify these keywords, you enable reverse address translation. Reverse address translation uses existing NO-PAT entries to translate the destination address for connections actively initiated from the external network to the internal network. The destination address is translated into the private IP address in the matching NO-PAT entry. |
|
add-route |
This keyword enables the device to automatically add a route destined for the private address when an inbound dynamic NAT rule is matched. The output interface is the NAT interface, and the next hop is the source address before translation. If you do not specify this keyword, you must manually add the route. |
7. (Optional.) Rearrange inbound dynamic NAT rules to adjust their priorities.
nat inbound rule move nat-rule-name1 { after | before } nat-rule-name2
Configuring NAT server mappings on an interface
About NAT server mappings
Typically, the NAT Server feature is configured on the interface connected to the external network to allow servers in the internal network or an MPLS VPN instance to provide services for external users. A NAT server mapping (also called NAT server rule) maps a public IP address and port number to the private IP address and port number of the internal server.
The NAT Server feature can be implemented by configuring the following server mappings:
· Common NAT server mapping—Maps the private IP address and the port number of the internal server to a public IP address and a port number. This method allows external hosts to access the internal server by using the specified public IP address.
· Load sharing NAT server mapping—You can add multiple internal servers to an internal server group so that these servers provide the same service for external hosts. The NAT device chooses one internal server based on the weight and number of connections of the servers to respond to a request from an external host to the public address of the internal server group.
· ACL-based NAT server mapping—An extension of common NAT server mapping. A common NAT server mapping maps the private IP address of the internal server to a single public IP address. An ACL-based NAT server mapping maps the private IP address of the internal server to a set of public IP addresses defined by an ACL. If the destination address of a packet matches a permit rule in the ACL, the destination address is translated into the private IP address of the internal server.
· Object group-based server mapping—Uses the address object group and service object group as the packet match criteria. The destination IP addresses and port numbers of the matching packets are translated to the same address and port number. For more information about object groups, see Security Configuration Guide.
Restrictions and guidelines for NAT server mapping configuration on an interface
In a scenario where Real-Time Transport Protocol (RTP) is used to transmit audio and video flows, the server and client send Real-Time Control Protocol (RTCP) packets periodically during the course of a session. If the server is on the private network, you must specify the reversible keyword when executing the nat server command. If you do not specify the reversible keyword, the NAT device discards the RTCP packets sent to the client on the public network and audio and video transmission services fail.
When you configure a load shared NAT server mapping, you must make sure a user uses the same public address and public port to access the same service on an internal server. For this purpose, make sure value N in the following mappings is equal to or less than the number of servers in the internal server group:
· One public address and N consecutive public port numbers are mapped to one internal server group.
· N consecutive public addresses and one public port number are mapped to one internal server group.
When you roll back configuration in a version that supports the automatic NAT rule name assignment, a rollback failure message is displayed if the no automatically assigned names exist in the replacement configuration file.
For example, the system compares the configuration in the replacement configuration file and the configuration after the rollback and displays a rollback failure message in the following conditions:
· The replacement configuration file has the following configuration: nat server global 112.1.1.1 inside 192.168.20.1.
· The NAT rule configuration after the rollback is nat server global 112.1.1.1 inside 192.168.20.1 rule NAT server rule_10 (NAT server rule_10 indicating an NAT rule name automatically assigned by the system).
In this case, the NAT rule configuration in the replacement configuration file has been issued and you can ignore this failure message.
Configuring common NAT server mappings
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Configure common NAT server mappings. Choose the options to configure as needed:
¡ A single public address with a single or no public port:
nat server [ protocol pro-type ] global{ global-address | current-interface | interface interface-type interface-number } [ global-port ] [ vpn-instance global-vpn-instance-name ] inside local-address [ local-port ] [ vpn-instance local-vpn-instance-name ] [ acl { ipv4-acl-number | name ipv4-acl-name } ] [ reversible ] [ vrrp virtual-router-id ] [ rule rule-name ] [ disable ] [ counting ] [ description text ]
¡ A single public address with consecutive public ports:
nat server protocol pro-type global{ global-address | current-interface | interface interface-type interface-number } global-port1 global-port2 [ vpn-instance global-vpn-instance-name ] inside { { local-address | local-address1 local-address2 } local-port | local-address local-port1 local-port2 } [ vpn-instance local-vpn-instance-name ] [ acl { ipv4-acl-number | name ipv4-acl-name } ] [ vrrp virtual-router-id ] [ rule rule-name ] [ disable ] [ counting ] [ description text ]
¡ Consecutive public addresses with no public port:
nat server protocol pro-type global global-address1 global-address2 [ vpn-instance global-vpn-instance-name ] inside { local-address | local-address1 local-address2 } [ local-port ] [ vpn-instance local-vpn-instance-name ] [ acl { ipv4-acl-number | name ipv4-acl-name } ] [ vrrp virtual-router-id ] [ rule rule-name ] [ disable ] [ counting ] [ description text ]
¡ Consecutive public addresses with a single public port:
nat server protocol pro-type global global-address1 global-address2 global-port [ vpn-instance global-vpn-instance-name ] inside { local-address [ local-port1 local-port2 ] | [ local-address | local-address1 local-address2 ] [ local-port ] } [ vpn-instance local-vpn-instance-name ] [ acl { ipv4-acl-number | name ipv4-acl-name } ] [ vrrp virtual-router-id ] [ rule rule-name ] [ disable ] [ counting ] [ description text ]
You can configure multiple NAT server mappings on an interface.
Support for the vrrp virtual-router-id option depends on the device model. For more information, see the command reference.
Configuring load sharing NAT server mappings
1. Enter system view.
system-view
2. Create a NAT server group and enter its view.
nat server-group group-id
By default, no NAT server groups exist.
3. Add an internal server into the group.
inside ip inside-ip port port-number [ weight weight-value ]
You can add multiple internal servers to a group.
4. Return to system view.
quit
5. Enter interface view.
interface interface-type interface-number
6. Configure a load sharing NAT server mapping.
nat server protocol pro-type global { { global-address | nat server protocol pro-type global { { global-address | current-interface | interface interface-type interface-number } { global-port | global-port1 global-port2 } | global-address1 global-address2 global-port } [ vpn-instance global-vpn-instance-name ] inside server-group group-id[ vpn-instance local-vpn-instance-name ] [ acl { ipv4-acl-number | name ipv4-acl-name } ] [ vrrp virtual-router-id ] [ rule rule-name ] [ disable ] [ counting ] [ description text ]
You can configure multiple load sharing NAT server mappings on an interface.
Configuring ACL-based NAT server mappings
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Configure an ACL-based NAT server mapping.
nat server global { ipv4-acl-number | name ipv4-acl-name } inside local-address [ local-port ] [ vpn-instance local-vpn-instance-name ] [ vrrp virtual-router-id ] [ rule rule-name ] [ priority priority ] [ disable ] [ counting ] [ description text ]
You can configure multiple NAT server mappings on an interface.
4. (Optional.) Rearrange ACL-based NAT server mappings to adjust their priorities.
nat server rule move nat-rule-name1 { after | before } nat-rule-name2
Configuring NAT444 on an interface
About NAT444
NAT444 provides outbound address translation, and it is configured on the interface connected to the public network. By configuring NAT444 address translation on the NAT444 gateway, multiple private IP addresses are mapped to one public IP address and a different port block is used for each private IP address
Restrictions and guidelines for NAT444 configuration on an interface
To configure dynamic port block mapping for NAT444, you must configure port block parameters in the NAT address group.
Configuring static port block mapping for NAT444
1. Enter system view.
system-view
2. Create a NAT port block group, and enter its view.
nat port-block-group group-id
3. Add a private IP address range to the port block group.
local-ip-address start-address end-address [ vpn-instance vpn-instance-name ]
You can add multiple private IP address ranges to one port block group, but they cannot overlap.
4. Add a public IP address range to the port block group.
global-ip-pool start-address end-address
You can add multiple public IP address ranges to one port block group, but they cannot overlap.
5. Configure the port range for the public IP addresses.
port-range start-port-number end-port-number
By default, the port range is 1 to 65535.
6. Set the port block size.
block-size block-size
By default, the port block size is 256.
7. Return to system view.
quit
8. Enter interface view.
interface interface-type interface-number
9. Configure a static outbound port block mapping rule on the interface.
nat outbound port-block-group group-id [ rule rule-name ] [ counting ]
By default, no port block mapping rule is configured on an interface.
You can configure multiple port block mapping rules on one interface.
10. (Optional.) Configure a PAT mapping mode.
a. Return to system view.
quit
b. Configure a PAT mapping mode.
nat mapping-behavior endpoint-independent [ acl { ipv4-acl-number | name ipv4-acl-name } ]
The default mapping mode is Address and Port-Dependent Mapping.
Configuring dynamic port block mapping for NAT444
Restrictions and guidelines
You can use one of the following methods to add IP addresses to a NAT address group:
· Method 1—Adding one or multiple address ranges.
· Method 2—Adding the IP address of the specified interface. This method supports the cooperation between dynamic NAT port block mappings and Easy IP and supports user tracing.
Only one method is supported for a NAT address group.
Use Method 2 if the IP address after translation is the IP address of the interface connected to the external network and the IP address is dynamically obtained through DHCP or PPPoE. This method avoids the inaccurate NAT IP address information caused by the IP address change of the interface.
Procedure
1. Enter system view.
system-view
2. (Optional.) Configure a PAT mapping mode.
nat mapping-behavior endpoint-independent [ acl { ipv4-acl-number | name ipv4-acl-name } ]
The default mapping mode is Address and Port-Dependent Mapping.
3. Create a NAT address group, and enter its view.
nat address-group group-id [ name group-name ]
4. Add addresses to the NAT address group. Choose one option as needed:
¡ Add IP address ranges to the NAT address group.
address start-address end-address
You can add multiple public IP address ranges to an address group.
The IP address ranges in address groups cannot overlap.
¡ Add the IP address of an interface to the NAT address group.
address interface interface-type interface-number
By default, no interface address exists in the NAT address group.
You can specify only one interface for a NAT address group.
5. (Optional.) Configure the port range for the public IP addresses.
port-range start-port-number end-port-number
By default, the port range is 1 to 65535.
The configuration takes effect only on PAT translation mode.
6. Configure port block parameters.
port-block block-size block-size [ extended-block-number extended-block-number ]
By default, no port block parameters exist.
The configuration takes effect only on PAT translation mode.
7. Return to system view.
quit
8. Enter interface view.
interface interface-type interface-number
9. Configure PAT for outbound dynamic NAT.
nat outbound [ ipv4-acl-number | name ipv4-acl-name ] [ address-group { group-id | name group-name } ] [ vpn-instance vpn-instance-name ] [ port-preserved ] [ rule rule-name ] [ priority priority ] [ disable ] [ counting ] [ description text ]
By default, no outbound dynamic NAT rules exist.
The port-preserved keyword does not take effect on dynamic NAT444.
10. (Optional.) Enable dynamic port block mapping synchronization.
a. Return to system view.
quit
b. Enable dynamic port block mapping synchronization.
nat port-block synchronization enable
By default, dynamic port block mapping synchronization is disabled.
Support for this command depends on the device model. For more information, see the command reference.
Enabling port block global sharing
About this task
When multiple interfaces have dynamic NAT port block mapping configured, the interfaces might create different port block mappings for packets from the same IP address. You can use this command to configure the interfaces to use the same port block mapping for translating packets from the same IP address.
Procedure
1. Enter system view
system-view
2. Enable port block global sharing.
nat port-block global-share enable
By default, port block global sharing is disabled.
Configuring DS-Lite B4 address translation on an interface
About this task
DS-Lite B4 address translation is configured on the AFTR's interface connected to the external network. It uses an IPv6 ACL to identify packets to be NATed.
DS-Lite B4 address translation supports only the dynamic port block mapping method.
Prerequisites
Before configuring DS-Lite B4 address translation, make sure the B4 element and the AFTR can reach each other through IPv6.
Procedure
1. Enter system view.
system-view
2. (Optional.) Configure a PAT mapping mode.
nat mapping-behavior endpoint-independent [ acl { ipv4-acl-number | name ipv4-acl-name } ]
The default mapping mode is Address and Port-Dependent Mapping.
3. Create a NAT address group, and enter its view.
nat address-group group-id [ name group-name ]
4. Add a public IP address range to the NAT address group.
address start-address end-address
You can add multiple public IP address ranges to an address group.
The IP address ranges in address groups cannot overlap.
5. Configure the port range for the public IP addresses.
port-range start-port-number end-port-number
By default, the port range is 1 to 65535.
The configuration takes effect only on PAT translation mode.
6. Configure port block parameters.
port-block block-size block-size [ extended-block-number extended-block-number ]
By default, no port block parameters exist.
The configuration takes effect only on PAT translation mode.
7. Return to system view.
quit
8. Enter interface view.
interface interface-type interface-number
9. Configure DS-Lite B4 address translation.
nat outbound ds-lite-b4 { ipv6-acl-number | name ipv6-acl-name } address-group group-id
By default, DS-Lite B4 address translation is not configured.
Configuring NAT hairpin
About this task
NAT hairpin allows internal hosts to access each other or allows internal hosts to access internal servers. The source and destination IP addresses of the packets are translated on the interface connected to the internal network.
Restrictions and guidelines
NAT hairpin works in conjunction with the following address translation methods:
· NAT Server and outbound dynamic NAT.
· NAT Server and outbound static NAT.
To provide service correctly, you must configure NAT hairpin on the same interface module as its collaborative NAT features.
When NAT hairpin works in conjunction with NAT Server, you must configure NAT server mappings in one of the following methods with a protocol type specified:
· Configuring common NAT server mappings
· Configuring load sharing NAT server mappings
To configure the P2P mode, you must configure outbound PAT on the interface connected to the external network and enable the EIM mapping mode.
Procedure
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Enable NAT hairpin.
nat hairpin enable
By default, NAT hairpin is disabled.
Configuring NAT ALG
About this task
NAT ALG translates address or port information in the application layer payload to ensure connection establishment.
For example, an FTP application includes a data connection and a control connection. The IP address and port number for the data connection depend on the payload information of the control connection. This requires NAT ALG to translate the address and port information to establish the data connection.
Procedure
1. Enter system view
system-view
2. Configure NAT ALG for a protocol or all protocols.
nat alg { all | dns | ftp | h323 | icmp-error | ils | mgcp | nbt | pptp | rsh | rtsp | sccp | sctp | sip | sqlnet | tftp | xdmcp }
By default, NAT ALG is enabled for DNS, FTP, ICMP error messages, PPTP, and RTSP, and is disabled for the other supported protocols.
Configuring NAT DNS mapping
About this task
NAT DNS mapping is applicable to scenarios that internal users accesses an interval server by using the domain name of the server when the DNS server is located at the external network. In the scenario, NAT DNS mapping cooperates with DNS ALG and NAT server mappings.
1. The DNS reply from the external DNS server contains only the domain name and public IP address of the internal server in the payload.
2. The NAT device might have multiple NAT server mappings with the same public IP address but different private IP addresses. DNS ALG might find an incorrect internal server by using only the public IP address. With a NAT DNS mapping is configured, DNS ALG obtains the correct public IP address, public port number, and protocol type of the internal server by using the domain name.
3. A NAT server mapping maps the public IP and port to the private IP and port of the internal server.
4. The NAT device sends the DNS reply to the internal user.
Restrictions and guidelines
NAT DNS mapping works in conjunction with NAT Server. NAT DNS mapping maps the domain name of an internal server to the public IP address, public port number, and protocol type of the internal server. NAT Server maps the public IP and port to the private IP and port of the internal server.
Procedure
1. Enter system view.
system-view
2. Enable NAT ALG for DNS.
nat alg dns
By default, NAT ALG is enabled for DNS.
3. Configure a NAT DNS mapping.
nat dns-map domain domain-name protocol pro-type { interface interface-type interface-number | ip global-ip } port global-port
You can configure multiple NAT DNS mappings.
Enabling NAT port halving
About this task
After you enable NAT port halving in HA load balancing, each port block will be equally divided between the two devices. The two devices will use different ports to translate packets from the same IP address, avoiding port assignment conflicts.
Hardware and feature compatibility
|
Hardware |
Feature compatibility |
|
MSR610 |
Yes |
|
MSR810, MSR810-W, MSR810-W-DB, MSR810-LM, MSR810-W-LM, MSR810-10-PoE, MSR810-LM-HK, MSR810-W-LM-HK, MSR810-LM-CNDE-SJK, MSR810-CNDE-SJK, MSR810-EI, MSR810-LM-EA, MSR810-LM-EI |
Yes |
|
MSR810-LMS, MSR810-LUS |
No |
|
MSR810-SI, MSR810-LM-SI |
No |
|
MSR810-LMS-EA, MSR810-LME |
No |
|
MSR1004S-5G, MSR1004S-5G-CN |
Yes |
|
MSR1104S-W, MSR1104S-W-CAT6, MSR1104S-5G-CN, MSR1104S-W-5G-CN |
Yes |
|
MSR2600-6-X1, MSR2600-15-X1, MSR2600-15-X1-T |
Yes |
|
MSR2600-10-X1 |
No |
|
MSR 2630 |
No |
|
MSR3600-28, MSR3600-51 |
No |
|
MSR3600-28-SI, MSR3600-51-SI |
No |
|
MSR3600-28-X1, MSR3600-28-X1-DP, MSR3600-51-X1, MSR3600-51-X1-DP |
No |
|
MSR3600-28-G-DP, MSR3600-51-G-DP |
No |
|
MSR3610-I-DP, MSR3610-IE-DP, MSR3610-IE-ES, MSR3610-IE-EAD, MSR-EAD-AK770, MSR3610-I-IG, MSR3610-IE-IG |
Yes |
|
MSR3610-X1, MSR3610-X1-DP, MSR3610-X1-DC, MSR3610-X1-DP-DC, MSR3620-X1, MSR3640-X1 |
No |
|
MSR 3610, MSR 3620, MSR 3620-DP, MSR 3640, MSR 3660 |
No |
|
MSR3610-G, MSR3620-G |
No |
|
MSR3640-G |
No |
|
MSR3640-X1-HI |
Yes |
|
Hardware |
Feature compatibility |
|
MSR810-W-WiNet, MSR810-LM-WiNet |
Yes |
|
MSR830-4LM-WiNet |
Yes |
|
MSR830-5BEI-WiNet, MSR830-6EI-WiNet, MSR830-10BEI-WiNet |
Yes |
|
MSR830-6BHI-WiNet, MSR830-10BHI-WiNet |
Yes |
|
MSR2600-6-WiNet |
Yes |
|
MSR2600-10-X1-WiNet |
No |
|
MSR2630-WiNet |
No |
|
MSR3600-28-WiNet |
No |
|
MSR3610-X1-WiNet |
No |
|
MSR3610-WiNet, MSR3620-10-WiNet, MSR3620-DP-WiNet, MSR3620-WiNet, MSR3660-WiNet |
No |
|
Hardware |
Feature compatibility |
|
MSR860-6EI-XS |
Yes |
|
MSR860-6HI-XS |
Yes |
|
MSR2630-XS |
Yes |
|
MSR3600-28-XS |
No |
|
MSR3610-XS |
No |
|
MSR3620-XS |
No |
|
MSR3610-I-XS |
Yes |
|
MSR3610-IE-XS |
Yes |
|
MSR3620-X1-XS |
No |
|
MSR3640-XS |
No |
|
MSR3660-XS |
No |
|
Hardware |
Feature compatibility |
|
MSR810-LM-GL |
Yes |
|
MSR810-W-LM-GL |
Yes |
|
MSR830-6EI-GL |
Yes |
|
MSR830-10EI-GL |
Yes |
|
MSR830-6HI-GL |
Yes |
|
MSR830-10HI-GL |
Yes |
|
MSR1004S-5G-GL |
Yes |
|
MSR2600-6-X1-GL |
Yes |
|
MSR3600-28-SI-GL |
No |
Restrictions and guidelines
Do not use this feature when the HA group works in active/standby mode or when the device works in standalone mode.
Procedure
1. Enter system view.
system-view
2. Enable NAT port halving.
nat port-load-balance enable slot slot-number
By default, NAT port halving is disabled.
Configuring the HA group for NAT
About the HA group for NAT
If only one NAT device is deployed in the internal network, internal users cannot access the external network when the NAT device fails. To avoid this situation, configure the HA group for NAT. In the HA group plan, the two devices in an HA group are capable of processing NAT services. Session entries, session relation entries, NAT port block entries, and NAT configurations are synchronized through the HA channel. When one device fails, the other device takes over.
Operating mechanism
Typically, the master device in the VRRP group processes NAT services in the HA network. The following example illustrates how the HA group in active/standby mode ensures uninterrupted NAT services when the master device fails.
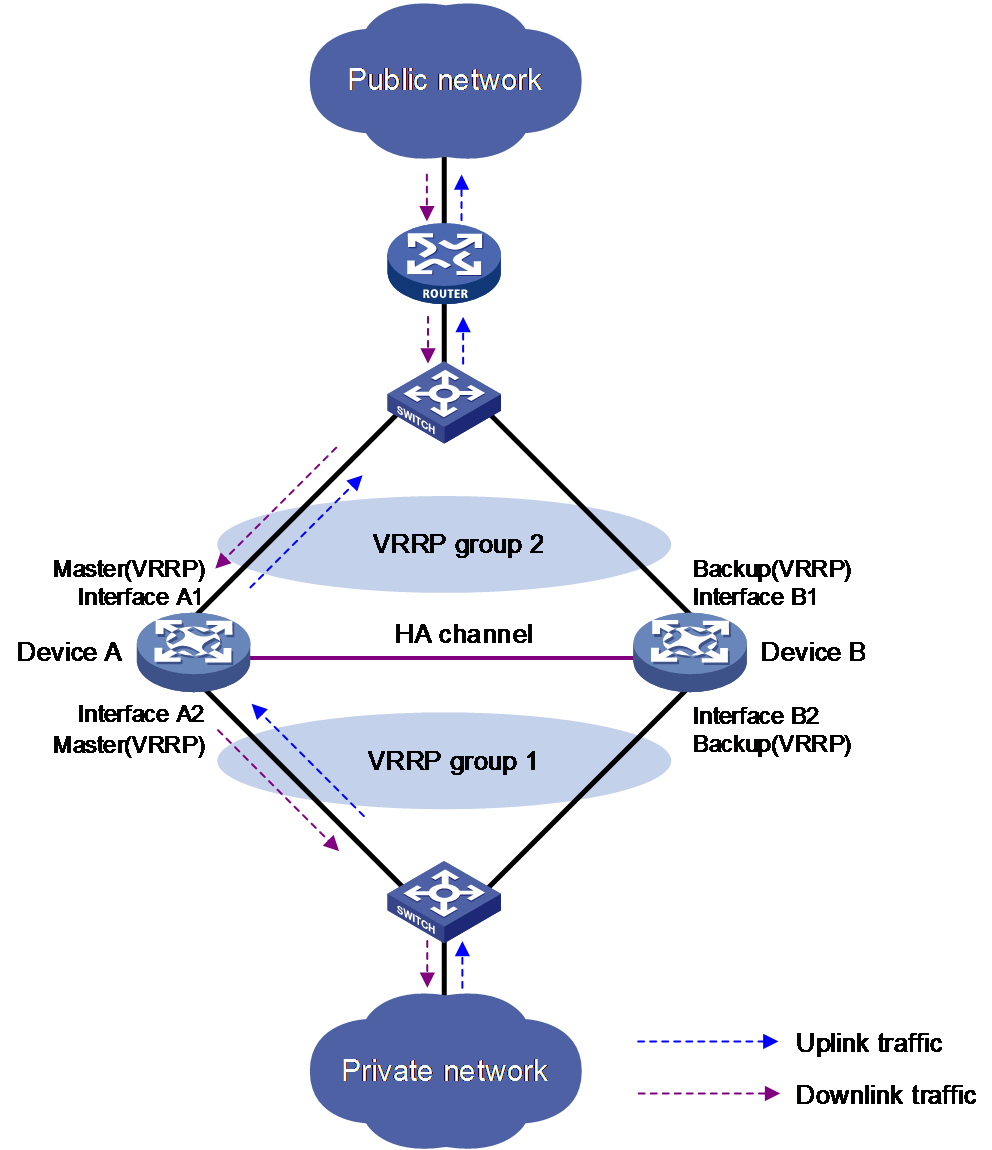
As shown in Figure 10, Device A acts as the primary device and Device B acts as the secondary device in an HA group. Device A synchronizes its session entries, session relation entries, and port block entries to Device B in real time through the HA channel. Downlinks of Device A and Device B are in VRRP group 1 and uplinks of Device A and Device B are in VRRP group 2. VRRP groups are associated with the HA group. RBM selects Device A as the master device for address translation based on the link status or forwarding capability of Device A.
When the two devices receive ARP requests for MAC addresses corresponding to public IP addresses in the NAT address group or port block group, Device A uses the virtual MAC address of the VRRP group to answer the requests. This mechanism ensures that Device A performs address translation for forward and reverse traffic.
Figure 10 HA group in active/standby mode
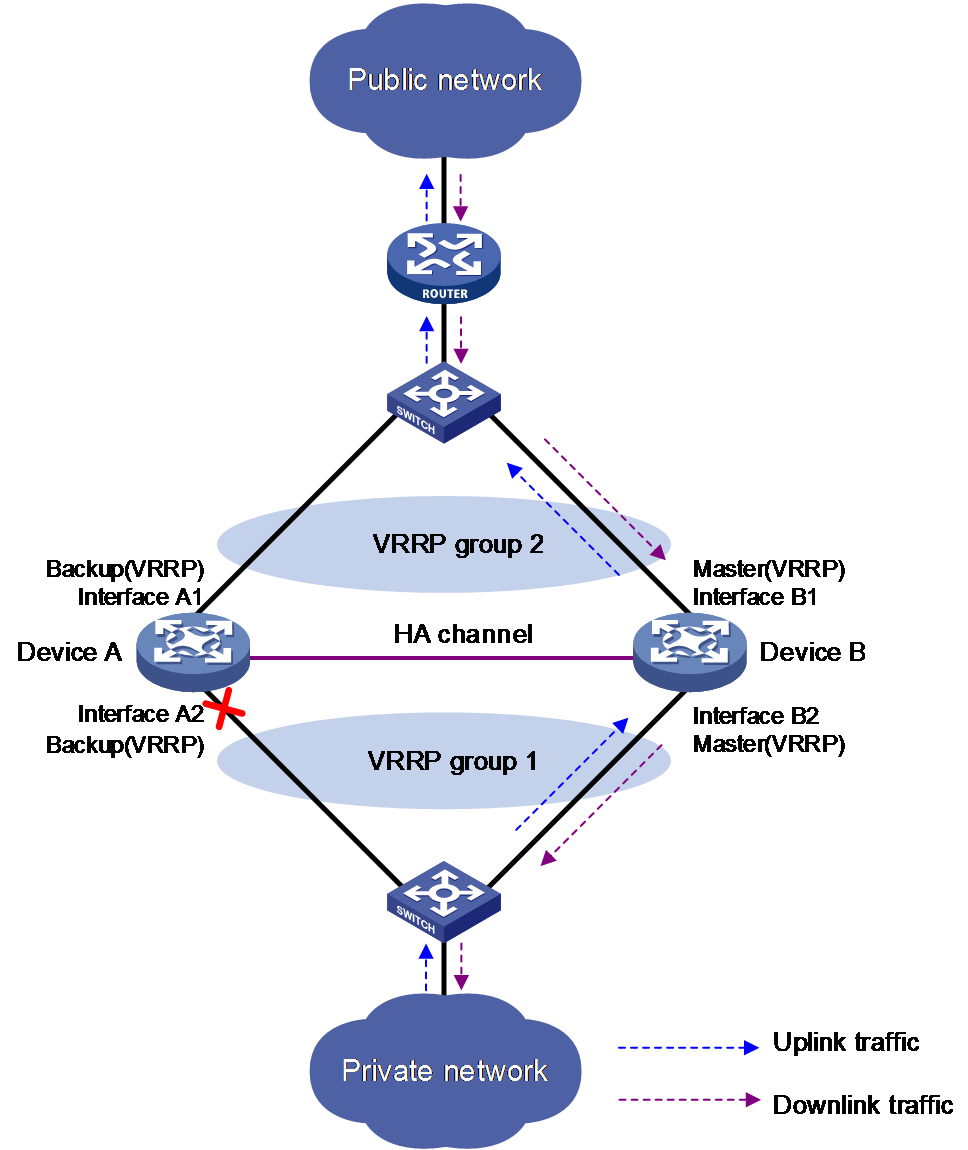
As shown in Figure 11, when Interface A2 of Device A fails, Device B becomes the master device in the VRRP group. Because Device B has NAT configuration information and service entries, NAT services are not interrupted after link switchover.
Figure 11 Traffic switchover in active/standby mode
Configuring the HA group in active/standby mode for interface-based NAT
About this task
In an active/standby HA network, some translation rules for static, source, or destination address translation issue the translated public IP addresses or the public IP addresses of internal servers to the address management module. Then, both the active and standby devices advertise the mappings between the public IP addresses and MAC addresses of their own physical interfaces to all nodes in the same LAN. As a result, the upstream Layer 3 device directly connected to the HA group might incorrectly send downlink packets to a VRRP backup device, causing service anomalies.
To avoid such an issue, bind address translation methods to the VRRP group in use. This ensures that only the VRRP master device responds to the ARP requests for the translated public IP addresses or the public IP addresses of internal servers. The MAC addresses in the responses are the virtual MAC address of the VRRP group.
Hardware and feature compatibility
|
Hardware |
Feature compatibility |
|
MSR610 |
Yes |
|
MSR810, MSR810-W, MSR810-W-DB, MSR810-LM, MSR810-W-LM, MSR810-10-PoE, MSR810-LM-HK, MSR810-W-LM-HK, MSR810-LM-CNDE-SJK, MSR810-CNDE-SJK, MSR810-EI, MSR810-LM-EA, MSR810-LM-EI |
Yes |
|
MSR810-LMS, MSR810-LUS |
No |
|
MSR810-SI, MSR810-LM-SI |
No |
|
MSR810-LMS-EA, MSR810-LME |
No |
|
MSR1004S-5G, MSR1004S-5G-CN |
Yes |
|
MSR1104S-W, MSR1104S-W-CAT6, MSR1104S-5G-CN, MSR1104S-W-5G-CN |
Yes |
|
MSR2600-6-X1, MSR2600-15-X1, MSR2600-15-X1-T |
Yes |
|
MSR2600-10-X1 |
No |
|
MSR 2630 |
No |
|
MSR3600-28, MSR3600-51 |
No |
|
MSR3600-28-SI, MSR3600-51-SI |
No |
|
MSR3600-28-X1, MSR3600-28-X1-DP, MSR3600-51-X1, MSR3600-51-X1-DP |
No |
|
MSR3600-28-G-DP, MSR3600-51-G-DP |
Yes |
|
MSR3610-I-DP, MSR3610-IE-DP, MSR3610-IE-ES, MSR3610-IE-EAD, MSR-EAD-AK770, MSR3610-I-IG, MSR3610-IE-IG |
Yes |
|
MSR3610-X1, MSR3610-X1-DP, MSR3610-X1-DC, MSR3610-X1-DP-DC, MSR3620-X1, MSR3640-X1 |
Yes |
|
MSR 3610, MSR 3620, MSR 3620-DP, MSR 3640, MSR 3660 |
Yes |
|
MSR3610-G, MSR3620-G |
Yes |
|
MSR3640-G |
Yes |
|
MSR3640-X1-HI |
Yes |
|
Hardware |
Feature compatibility |
|
MSR810-W-WiNet, MSR810-LM-WiNet |
Yes |
|
MSR830-4LM-WiNet |
Yes |
|
MSR830-5BEI-WiNet, MSR830-6EI-WiNet, MSR830-10BEI-WiNet |
Yes |
|
MSR830-6BHI-WiNet, MSR830-10BHI-WiNet |
Yes |
|
MSR2600-6-WiNet |
Yes |
|
MSR2600-10-X1-WiNet |
No |
|
MSR2630-WiNet |
No |
|
MSR3600-28-WiNet |
No |
|
MSR3610-X1-WiNet |
Yes |
|
MSR3610-WiNet, MSR3620-10-WiNet, MSR3620-DP-WiNet, MSR3620-WiNet, MSR3660-WiNet |
Yes |
|
Hardware |
Feature compatibility |
|
MSR860-6EI-XS |
Yes |
|
MSR860-6HI-XS |
Yes |
|
MSR2630-XS |
Yes |
|
MSR3600-28-XS |
No |
|
MSR3610-XS |
Yes |
|
MSR3620-XS |
Yes |
|
MSR3610-I-XS |
Yes |
|
MSR3610-IE-XS |
Yes |
|
MSR3620-X1-XS |
Yes |
|
MSR3640-XS |
Yes |
|
MSR3660-XS |
Yes |
|
Hardware |
Feature compatibility |
|
MSR810-LM-GL |
Yes |
|
MSR810-W-LM-GL |
Yes |
|
MSR830-6EI-GL |
Yes |
|
MSR830-10EI-GL |
Yes |
|
MSR830-6HI-GL |
Yes |
|
MSR830-10HI-GL |
Yes |
|
MSR1004S-5G-GL |
Yes |
|
MSR2600-6-X1-GL |
Yes |
|
MSR3600-28-SI-GL |
No |
Restrictions and guidelines
Execute the vrrp command on the primary device in the HA group.
Procedure
1. Enter system view.
system-view
2. Bind a translation method to a VRRP group. Choose the following steps to configure as needed.
3. Bind a VRRP group to the NAT address group.
a. Enter NAT address group view.
nat address-group group-id [ name group-name ]
b. Bind a VRRP group to the NAT address group.
vrrp vrid virtual-router-id
By default, a NAT address group is not bound to any VRRP group.
4. Bind a VRRP group to the NAT port block group.
a. Enter NAT port block group view.
nat port-block-group group-id
b. Bind a VRRP group to the NAT port block group.
vrrp vrid virtual-router-id
By default, a NAT port block group is not bound to any VRRP group.
5. Bind a VRRP group to the one-to-one mapping for outbound static NAT. For more information, see "Configuring outbound one-to-one static NAT."
6. Bind a VRRP group to the net-to-net mapping for outbound static NAT. For more information, see "Configuring outbound net-to-net static NAT."
7. Bind a VRRP group to the object group-based outbound static NAT mapping. For more information, see "Configuring object group-based outbound static NAT."
8. Bind a VRRP group to the internal server.
a. Enter interface view.
interface interface-type interface-number
b. Bind a VRRP group to the internal server.
For more information, see "Configuring common NAT server mappings," "Configuring load sharing NAT server mappings," and "Configuring ACL-based NAT server mappings."
Configuring the HA group in dual-active mode for interface-based NAT
About this task
On a dual-active HA network, upstream Layer 3 device directly connected to the HA group might incorrectly send downlink packets to a VRRP backup device, causing service anomalies.
To avoid such an issue, bind address translation methods to the VRRP group in use. This ensures that only the VRRP master device responds to the ARP requests for the translated public IP addresses or the public IP addresses of internal servers. The MAC addresses in the responses are the virtual MAC address of the VRRP group.
Hardware and feature compatibility
|
Hardware |
Feature compatibility |
|
MSR610 |
Yes |
|
MSR810, MSR810-W, MSR810-W-DB, MSR810-LM, MSR810-W-LM, MSR810-10-PoE, MSR810-LM-HK, MSR810-W-LM-HK, MSR810-LM-CNDE-SJK, MSR810-CNDE-SJK, MSR810-EI, MSR810-LM-EA, MSR810-LM-EI |
Yes |
|
MSR810-LMS, MSR810-LUS |
No |
|
MSR810-SI, MSR810-LM-SI |
No |
|
MSR810-LMS-EA, MSR810-LME |
No |
|
MSR1004S-5G, MSR1004S-5G-CN |
Yes |
|
MSR1104S-W, MSR1104S-W-CAT6, MSR1104S-5G-CN, MSR1104S-W-5G-CN |
Yes |
|
MSR2600-6-X1, MSR2600-15-X1, MSR2600-15-X1-T |
Yes |
|
MSR2600-10-X1 |
No |
|
MSR 2630 |
No |
|
MSR3600-28, MSR3600-51 |
No |
|
MSR3600-28-SI, MSR3600-51-SI |
No |
|
MSR3600-28-X1, MSR3600-28-X1-DP, MSR3600-51-X1, MSR3600-51-X1-DP |
No |
|
MSR3600-28-G-DP, MSR3600-51-G-DP |
Yes |
|
MSR3610-I-DP, MSR3610-IE-DP, MSR3610-IE-ES, MSR3610-IE-EAD, MSR-EAD-AK770, MSR3610-I-IG, MSR3610-IE-IG |
Yes |
|
MSR3610-X1, MSR3610-X1-DP, MSR3610-X1-DC, MSR3610-X1-DP-DC, MSR3620-X1, MSR3640-X1 |
Yes |
|
MSR 3610, MSR 3620, MSR 3620-DP, MSR 3640, MSR 3660 |
Yes |
|
MSR3610-G, MSR3620-G |
Yes |
|
MSR3640-G |
Yes |
|
MSR3640-X1-HI |
Yes |
|
Hardware |
Feature compatibility |
|
MSR810-W-WiNet, MSR810-LM-WiNet |
Yes |
|
MSR830-4LM-WiNet |
Yes |
|
MSR830-5BEI-WiNet, MSR830-6EI-WiNet, MSR830-10BEI-WiNet |
Yes |
|
MSR830-6BHI-WiNet, MSR830-10BHI-WiNet |
Yes |
|
MSR2600-6-WiNet |
Yes |
|
MSR2600-10-X1-WiNet |
No |
|
MSR2630-WiNet |
No |
|
MSR3600-28-WiNet |
No |
|
MSR3610-X1-WiNet |
Yes |
|
MSR3610-WiNet, MSR3620-10-WiNet, MSR3620-DP-WiNet, MSR3620-WiNet, MSR3660-WiNet |
Yes |
|
Hardware |
Feature compatibility |
|
MSR860-6EI-XS |
Yes |
|
MSR860-6HI-XS |
Yes |
|
MSR2630-XS |
Yes |
|
MSR3600-28-XS |
No |
|
MSR3610-XS |
Yes |
|
MSR3620-XS |
Yes |
|
MSR3610-I-XS |
Yes |
|
MSR3610-IE-XS |
Yes |
|
MSR3620-X1-XS |
Yes |
|
MSR3640-XS |
Yes |
|
MSR3660-XS |
Yes |
|
Hardware |
Feature compatibility |
|
MSR810-LM-GL |
Yes |
|
MSR810-W-LM-GL |
Yes |
|
MSR830-6EI-GL |
Yes |
|
MSR830-10EI-GL |
Yes |
|
MSR830-6HI-GL |
Yes |
|
MSR830-10HI-GL |
Yes |
|
MSR1004S-5G-GL |
Yes |
|
MSR2600-6-X1-GL |
Yes |
|
MSR3600-28-SI-GL |
No |
Restrictions and guidelines
Select one of the following configuration methods:
· The two devices share a NAT address group or port block group. To prevent different VRRP master devices from using the same IP-port mapping for different hosts, specify the PAT translation mode and execute the nat remote-backup port-alloc command on the HA primary device.
· As a best practice to prevent different VRRP master devices from using the same IP-port mapping for different hosts, configure the two devices to use different public IP addresses for address translation. For example, if the two devices use different NAT address groups or port block groups, user traffic with different source IP addresses is identified by ACLs in NAT rules. To enable different master devices to translate the forward user traffic, specify different gateway addresses for different internal users. To direct the reverse traffic to different VRRP master devices, bind NAT address groups or port block groups to different VRRP groups on the HA primary device.
Procedure
1. Enter system view.
system-view
2. Bind a translation method to a VRRP group. Choose the following steps to configure as needed.
3. Bind a VRRP group to the NAT address group.
a. Enter NAT address group view.
nat address-group group-id [ name group-name ]
b. Bind a VRRP group to the NAT address group.
vrrp vrid virtual-router-id
By default, a NAT address group is not bound to any VRRP group.
If you execute this command multiple times, the most recent configuration takes effect.
4. Bind a VRRP group to the NAT port block group.
a. Enter NAT port block group view.
nat port-block-group group-id
b. Bind a VRRP group to the NAT port block group.
vrrp vrid virtual-router-id
By default, a NAT port block group is not bound to any VRRP group.
If you execute this command multiple times, the most recent configuration takes effect.
5. (Optional.) Specify NAT port block ranges for the two devices in the HA group.
a. Return to system view.
quit
b. Specify NAT port ranges for the two devices in the HA group.
nat remote-backup port-alloc { primary | secondary }
By default, the two devices in the HA group share NAT port resources.
The following table describes port ranges indicated by the keywords:
|
Keyword |
Port ranges |
|
primary |
The first half of the port range. |
|
secondary |
The second half of the port range. |
6. Bind a VRRP group to the one-to-one mapping for outbound static NAT. For more information, see "Configuring outbound one-to-one static NAT."
7. Bind a VRRP group to the net-to-net mapping for outbound static NAT. For more information, see "Configuring outbound net-to-net static NAT."
8. Bind a VRRP group to the object group-based outbound static NAT mapping. For more information, see "Configuring object group-based outbound static NAT."
9. Bind a VRRP group to the internal server.
a. Enter interface view.
interface interface-type interface-number
b. Bind a VRRP group to the internal server.
For more information, see "Configuring common NAT server mappings," "Configuring load sharing NAT server mappings," and "Configuring ACL-based NAT server mappings."
Configuring NAT maintenance
Enabling sending ICMP error messages for NAT failures
About this task
By default, the device does not send ICMP error messages when NAT fails. Disabling sending ICMP error messages for NAT failures reduces useless packets, saves bandwidth, and avoids exposing the firewall IP address to the public network.
Restrictions and guidelines
Enable this feature for traceroute because the traceroute function requires ICMP error packets.
Procedure
1. Enter system view.
system-view
2. Enable sending ICMP error messages for NAT failures.
nat icmp-error reply
By default, no ICMP error messages are sent for NAT failures.
Configuring NAT logging
Configuring NAT session logging
About this task
NAT session logging records NAT session information, including translation information and access information.
A NAT device generates NAT session logs for the following events:
· NAT session establishment.
· NAT session removal. This event occurs when you add a configuration with a higher priority, remove a configuration, change ACLs, when a NAT session ages out, or when you manually delete a NAT session.
· Active NAT session logging. Active NAT flows refer to NAT sessions that exist within a period of time. When the specified interval for logging active NAT flows expires, the device records the existing NAT session information and generates a log.
Procedure
1. Enter system view.
system-view
2. Enable NAT logging.
nat log enable [ acl { ipv4-acl-number | name ipv4-acl-name } ]
By default, NAT logging is disabled.
3. Enable NAT session logging. Choose the options to configure as needed:
¡ For NAT session establishment events:
nat log flow-begin
¡ For NAT session removal events:
nat log flow-end
¡ For active NAT flows:
nat log flow-active minutes
By default, NAT session logging is disabled.
Configuring NAT444 user logging
About this task
NAT444 user logs are used for user tracing. The NAT444 gateway generates a user log whenever it assigns or withdraws a port block. The log includes the private IP address, public IP address, and port block. You can use the public IP address and port numbers to locate the user's private IP address from the user logs.
A NAT444 gateway generates NAT user logs when one of the following events occurs:
· A port block is assigned.
For the NAT444 static port block mapping, the NAT444 gateway generates a user log when it translates the first connection from a private IP address.
For the NAT444 dynamic port block mapping, the NAT444 gateway generates a user log when it assigns or extends a port block for a private IP address.
· A port block is withdrawn.
For the NAT444 static port block mapping, the NAT444 gateway generates a user log when all connections from a private IP address are disconnected.
For the NAT444 dynamic port block mapping, the NAT444 gateway generates a user log when all the following conditions are met:
¡ All connections from a private IP address are disconnected.
¡ The port blocks (including the extended ones) assigned to the private IP address are withdrawn.
¡ The corresponding mapping entry is deleted.
Prerequisites
Before configuring NAT444 user logging, you must configure the custom NAT444 log generation and outputting features. For more information, see the information center in Network Management and Monitoring Configuration Guide.
Procedure
1. Enter system view.
system-view
2. Enable NAT logging.
nat log enable [ acl { ipv4-acl-number | name ipv4-acl-name } ]
By default, NAT logging is disabled.
The acl keyword does not take effect on NAT444 user logging.
3. Enable NAT444 user logging. Choose the options to configure as needed:
¡ For port block assignment:
nat log port-block-assign
¡ For port block withdrawal:
nat log port-block-withdraw
By default, NAT444 user logging is disabled.
Configuring NAT alarm logging
About this task
Packets that need to be translated are dropped if the NAT resources are not enough. In NO-PAT, the NAT resources refer to the public IP addresses. In EIM PAT, the NAT resources refer to public IP addresses and ports. In NAT444, the NAT resources refer to public IP addresses, port blocks, or ports in port blocks. NAT alarm logging monitors the usage of NAT resources and outputs logs if the NAT resources are not enough.
For NAT444 dynamic port block mappings, an alarm log is generated upon the port block assignment failure or the failure that port resources cannot meet the user address translation requirement.
Restrictions and guidelines
The nat log alarm command take effect only after you use the nat log enable command to enable NAT logging.
Prerequisites
Before configuring NAT alarm logging, you must configure the custom NAT log generation and outputting features. For more information, see the information center in Network Management and Monitoring Configuration Guide.
Procedure
1. Enter system view.
system-view
2. Enable NAT logging.
nat log enable [ acl { ipv4-acl-number | name ipv4-acl-name } ]
By default, NAT logging is disabled.
The acl keyword does not take effect on NAT alarm logging.
3. Enable NAT alarm logging.
nat log alarm
By default, NAT alarm logging is disabled.
An NAT alarm log is output when NAT resources run out.
4. (Optional.) Set the NAT444 port block usage threshold.
nat log port-block usage threshold threshold-value
By default, the NAT444 port block usage threshold is 90%.
The system generates alarm logs if the port block usage exceeds the threshold.
Enabling logging for IP usage of a NAT address group in NO-PAT mode
About this task
The system generates a log if the IP usage of a NAT address group exceeds the threshold.
Restrictions and guidelines
This feature takes effect only after you enable NAT logging by using the nat log enable command.
Procedure
1. Enter system view.
system-view
2. Enable NAT logging.
nat log enable [ acl { ipv4-acl-number | name ipv4-acl-name } ]
By default, NAT logging is disabled.
The acl keyword does not take effect on the logging for IP usage of a NAT address group in NO-PAT mode.
3. Enable logging for the IP usage of a NAT address group in NO-PAT mode and set a threshold.
nat log no-pat ip-usage [ threshold value ]
By default, logging is disabled for the IP usage of a NAT address group.
Configuring NAT in specific networks
Enabling NAT reply redirection
About this task
In some network scenarios, the inbound dynamic NAT is configured with tunneling, and multiple tunnel interfaces use the same NAT address group. In this case, the device will translate the source IP addresses of packets from different tunnels into the same NAT address before forwarding them. When the forwarding interface receives the reply packets, the device, by default, will not look up the NAT session table. This will cause the incorrect forwarding of the reply packets. To solve the problem, you can enable the NAT reply redirection feature on the forwarding interface. NAT reply redirection allows the interface to use the NAT session table to translate the destination IP addresses for NAT reply packets and find the correct output interfaces for those NATed reply packets.
Procedure
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Enable NAT reply redirection.
nat redirect reply-route enable
By default, NAT reply redirection is disabled.
Enabling the deletion of timestamps in TCP SYN and SYN ACK packets
About this task
With this feature configured, the system deletes the timestamps from the TCP SYN and SYN ACK packets after dynamic address translation.
If PAT mode is configured on an interface by using nat inbound or nat outbound, and the tcp_timestams and tcp_tw_recycle function is configured on the TCP server, TCP connections might not be established. To solve the problem, you can shut down the tcp_tw_recycle function or configure the nat timestamp delete command.
Procedure
1. Enter system view.
system-view
2. Enable the deletion of timestamps in TCP SYN and SYN ACK packets
nat timestamp delete [ vpn-instance vpn-instance-name ]
By default, the deletion of timestamps in TCP SYN and SYN ACK packets is disabled.
You can enable this feature for multiple VPN instances by repeating the command with different VPN parameters.
Enabling NAT session recreation after link switchover
About this task
This feature is applicable to a WAN network where two interfaces of the NAT device are configured with outbound dynamic NAT rules using different address groups. When the link of one interface fails, traffic on this link is switched to the link of the other interface and the NAT device operates as follows:
· If the two interfaces are in different security zones, the NAT device deletes old session entries after link switchover. When user traffic later arrives, it triggers the NAT session recreation. This mechanism ensures that internal users can access the external network.
· If the two interfaces are in the same security zone, the NAT device retains old session entries after link switchover. Internal users cannot access the external network because the device uses old session entries to match the user traffic. To avoid this issue, enable this feature to ensure availability of NAT services.
Procedure
1. Enter system view.
system-view
2. Enable NAT session recreation after link switchover.
nat link-switch recreate-session
By default, NAT session recreation is disabled after link switchover.
Display and maintenance commands for NAT
Execute display commands in any view and reset commands in user view.
|
Task |
Command |
|
Display the NAT ALG status for all supported protocols |
display nat alg |
|
Display all NAT configuration information. |
display nat all |
|
Display NAT address group information. |
display nat address-group [ group-id ] |
|
Display NAT DNS mapping configuration. |
display nat dns-map |
|
Display information about NAT EIM entries. |
In standalone mode: display nat eim In IRF mode: display nat eim [ slot slot-number ] |
|
Display inbound dynamic NAT configuration. |
display nat inbound |
|
Display NAT logging configuration. |
display nat log |
|
Display information about NAT NO-PAT entries. |
In standalone mode: display nat no-pat In IRF mode: display nat no-pat [ slot slot-number ] |
|
Display IP usage of NAT address groups in NO-PAT mode. |
In standalone mode: display nat no-pat ip-usage [ address-group { group-id | name group-name } | object-group object-group-name ] In IRF mode: display nat no-pat ip-usage [ address-group { group-id | name group-name } | object-group object-group-name ] [ slot slot-number ] |
|
Display outbound dynamic NAT configuration. |
display nat outbound |
|
Display NAT server mappings. |
display nat server |
|
Display internal server group configuration. |
display nat server-group [ group-id ] |
|
Display NAT sessions. |
In standalone mode: display nat session [ [ responder ] { source-ip source-ip | destination-ip destination-ip } * [ vpn-instance vpn-instance-name ] ] [ verbose ] In IRF mode: display nat session [ [ responder ] { source-ip source-ip | destination-ip destination-ip } * [ vpn-instance vpn -instance-name ] ] [ slot slot-number ] [ verbose ] |
|
Display static NAT mappings. |
display nat static |
|
Display NAT statistics. |
In standalone mode: display nat statistics [ summary ] In IRF mode: display nat statistics [ summary ] [ slot slot-number ] |
|
Display static outbound port block mapping rules for NAT444 |
display nat outbound port-block-group |
|
Display NAT port block group configuration. |
display nat port-block-group [ group-id ] |
|
Display NAT port block mappings. |
In standalone mode: display nat port-block { dynamic [ address-group { group-id | name group-name } ] [ ds-lite-b4 ] | static [ port-block-group group-id ] } In IRF mode: display nat port-block { dynamic [ address-group { group-id | name group-name } ] [ ds-lite-b4 ] | static [ port-block-group group-id ] } [ slot slot-number ] |
|
In standalone mode: display nat port-block-usage [ address-group group-id ] In IRF mode: display nat port-block-usage [ address-group group-id ] [ slot slot-number ] |
|
|
Clear NAT counting statistics. |
reset nat count statistics { all | dynamic | policy | server | static | static-port-block } |
|
Clear NAT sessions. |
In standalone mode: reset nat session In IRF mode: reset nat session [ slot slot-number ] |
NAT configuration examples
Example: Configuring outbound one-to-one static NAT
Network configuration
Configure static NAT to allow the host at 10.110.10.8/24 to access the Internet.
Procedure
# Specify IP addresses for the interfaces on the router. (Details not shown.)
# Configure a one-to-one static NAT mapping between the private address 10.110.10.8 and the public address 202.38.1.100.
<Router> system-view
[Router] nat static outbound 10.110.10.8 202.38.1.100
# Enable static NAT on GigabitEthernet 1/0/2.
[Router] interface gigabitethernet 1/0/2
[Router-GigabitEthernet1/0/2] nat static enable
Verifying the configuration
# Verify that the host at 10.110.10.8/24 can access the server on the Internet. (Details not shown.)
# Display static NAT configuration.
[Router] display nat static
Static NAT mappings:
Totally 1 outbound static NAT mappings.
IP-to-IP:
Local IP : 10.110.10.8
Global IP : 202.38.1.100
Config status: Active
Interfaces enabled with static NAT:
Totally 1 interfaces enabled with static NAT.
Interface: GigabitEthernet1/0/2
Config status: Active
# Display NAT sessions.
[Router] display nat session verbose
Slot 0:
Total sessions found: 0
Slot 2:
Initiator:
Source IP/port: 10.110.10.8/42496
Destination IP/port: 202.38.1.111/2048
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: ICMP(1)
Inbound interface: GigabitEthernet1/0/1
Responder:
Source IP/port: 202.38.1.111/42496
Destination IP/port: 202.38.1.100/0
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: ICMP(1)
Inbound interface: GigabitEthernet1/0/2
State: ICMP_REPLY
Application: INVALID
Rule ID: -/-/-
Rule name:
Start time: 2012-08-16 09:30:49 TTL: 27s
Initiator->Responder: 5 packets 420 bytes
Responder->Initiator: 5 packets 420 bytes
Total sessions found: 1
Example: Configuring outbound dynamic NAT (non-overlapping addresses)
Network configuration
As shown in Figure 13, a company has a private address 192.168.0.0/16 and two public IP addresses 202.38.1.2 and 202.38.1.3. Configure outbound dynamic NAT to allow only internal users on subnet 192.168.1.0/24 to access the Internet.
Procedure
# Specify IP addresses for the interfaces on the router. (Details not shown.)
# Configure address group 0, and add an address range from 202.38.1.2 to 202.38.1.3 to the group.
<Router> system-view
[Router] nat address-group 0
[Router-address-group-0] address 202.38.1.2 202.38.1.3
[Router-address-group-0] quit
# Configure ACL 2000 to identify packets from subnet 192.168.1.0/24.
[Router] acl basic 2000
[Router-acl-ipv4-basic-2000] rule permit source 192.168.1.0 0.0.0.255
[Router-acl-ipv4-basic-2000] quit
# Enable outbound dynamic PAT on GigabitEthernet 1/0/2. The source IP addresses of the packets permitted by the ACL rule is translated into the addresses in address group 0.
[Router] interface gigabitethernet 1/0/2
[Router-GigabitEthernet1/0/2] nat outbound 2000 address-group 0
Verifying the configuration
# Verify that Host A can access the WWW server, while Host B cannot. (Details not shown.)
# Display all NAT configuration and statistics.
[Router] display nat all
NAT address group information:
Totally 1 NAT address groups.
Address group ID: 0:
Port range: 1-65535
Address information:
Start address End address
202.38.1.2 202.38.1.3
NAT outbound information:
Totally 1 NAT outbound rules.
Interface: GigabitEthernet1/0/2
ACL: 2000
Address group ID: 0
Port-preserved: N NO-PAT: N Reversible: N
Config status: Active
NAT logging:
Log enable : Disabled
Flow-begin : Disabled
Flow-end : Disabled
Flow-active : Disabled
Port-block-assign : Disabled
Port-block-withdraw : Disabled
Alarm : Disabled
NO-PAT IP usage : Disabled
NAT mapping behavior:
Mapping mode : Address and Port-Dependent
ACL : ---
Config status: Active
NAT ALG:
DNS : Enabled
FTP : Enabled
H323 : Enabled
ICMP-ERROR : Enabled
ILS : Enabled
MGCP : Enabled
NBT : Enabled
PPTP : Enabled
RTSP : Enabled
RSH : Enabled
SCCP : Enabled
SIP : Enabled
SQLNET : Enabled
TFTP : Enabled
XDMCP : Enabled
Static NAT load balancing: Disabled
# Display NAT sessions that are generated when Host A accesses the WWW server.
[Router] display nat session verbose
Slot 0:
Total sessions found: 0
Slot 2:
Initiator:
Source IP/port: 192.168.1.10/52992
Destination IP/port: 200.1.1.10/2048
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: ICMP(1)
Inbound interface: GigabitEthernet1/0/1
Responder:
Source IP/port: 200.1.1.10/4
Destination IP/port: 202.38.1.3/0
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: ICMP(1)
Inbound interface: GigabitEthernet1/0/2
State: ICMP_REPLY
Application: INVALID
Rule ID: -/-/-
Rule name:
Start time: 2012-08-15 14:53:29 TTL: 12s
Initiator->Responder: 1 packets 84 bytes
Responder->Initiator: 1 packets 84 bytes
Total sessions found: 1
Example: Configuring outbound bidirectional NAT
Network configuration
As shown in Figure 14, the private network where the Web server resides overlaps with the company private network 192.168.1.0/24. The company has two public IP addresses 202.38.1.2 and 202.38.1.3. Configure NAT to allow internal users to access the external Web server by using the server's domain name.
Requirements analysis
To meet the network configuration, you must perform the following tasks:
· Configure inbound dynamic NAT ALG to make sure the internal host reaches the Web server instead of another internal host. NAT ALG can translate the Web server's IP address in the DNS reply payload to a dynamically assigned public address.
· Configure outbound dynamic NAT to translate the source IP address of packets from an internal host to a dynamically assigned public address.
· Add a static route to the public IP address of the external Web server.
Procedure
# Specify IP addresses for the interfaces on the router. (Details not shown.)
# Enable NAT with ALG and DNS.
<Router> system-view
[Router] nat alg dns
# Configure ACL 2000 to identify packets from subnet 192.168.1.0/24.
[Router] acl basic 2000
[Router-acl-ipv4-basic-2000] rule permit source 192.168.1.0 0.0.0.255
[Router-acl-ipv4-basic-2000] quit
# Create address group 1.
[Router] nat address-group 1
# Add address 202.38.1.2 to the group.
[Router-address-group-1] address 202.38.1.2 202.38.1.2
[Router-address-group-1] quit
# Create address group 2.
[Router] nat address-group 2
# Add address 202.38.1.3 to the group.
[Router-address-group-2] address 202.38.1.3 202.38.1.3
[Router-address-group-2] quit
# Enable inbound NO-PAT on GigabitEthernet 1/0/2 to translate the source IP address in the DNS reply payload into the address in address group 1, and allow reverse translation.
[Router] interface gigabitethernet 1/0/2
[Router-GigabitEthernet1/0/2] nat inbound 2000 address-group 1 no-pat reversible
# Enable outbound PAT on GigabitEthernet 1/0/2 to translate the source address of outgoing packets into the address in address group 2.
[Router-GigabitEthernet1/0/2] nat outbound 2000 address-group 2
# Configure a static route to 202.38.1.2 with GigabitEthernet 1/0/2 as the output interface and 20.2.2.2 as the next hop. (The next hop address varies by network.)
[Router] ip route-static 202.38.1.2 32 gigabitethernet 1/0/2 20.2.2.2
Verifying the configuration
# Verify that Host A can access the Web server by using its domain name. (Details not shown.)
# Display all NAT configuration and statistics.
[Router] display nat all
NAT address group information:
Totally 2 NAT address groups.
Address group ID: 1
Port range: 1-65535
Address information:
Start address End address
202.38.1.2 202.38.1.2
Address group ID: 2
Port range: 1-65535
Address information:
Start address End address
202.38.1.3 202.38.1.3
NAT inbound information:
Totally 1 NAT inbound rules.
Interface: GigabitEthernet1/0/2
ACL: 2000
Address group ID: 1
Add route: N NO-PAT: Y Reversible: Y
Config status: Active
NAT outbound information:
Totally 1 NAT outbound rules.
Interface: GigabitEthernet1/0/2
ACL: 2000
Address group ID: 2
Port-preserved: N NO-PAT: N Reversible: N
Config status: Active
NAT logging:
Log enable : Disabled
Flow-begin : Disabled
Flow-end : Disabled
Flow-active : Disabled
Port-block-assign : Disabled
Port-block-withdraw : Disabled
Alarm : Disabled
NO-PAT IP usage : Disabled
NAT mapping behavior:
Mapping mode : Address and Port-Dependent
ACL : ---
Config status: Active
NAT ALG:
DNS : Enabled
FTP : Enabled
H323 : Enabled
ICMP-ERROR : Enabled
ILS : Enabled
MGCP : Enabled
NBT : Enabled
PPTP : Enabled
RTSP : Enabled
RSH : Enabled
SCCP : Enabled
SIP : Enabled
SQLNET : Enabled
TFTP : Enabled
XDMCP : Enabled
Static NAT load balancing: Disabled
# Display NAT sessions that are generated when Host A accesses the Web server.
[Router] display nat session verbose
Slot 0:
Total sessions found: 0
Slot 2:
Initiator:
Source IP/port: 192.168.1.10/1694
Destination IP/port: 202.38.1.2/8080
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: TCP(6)
Inbound interface: GigabitEthernet1/0/1
Responder:
Source IP/port: 192.168.1.10/8080
Destination IP/port: 202.38.1.3/1025
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: TCP(6)
Inbound interface: GigabitEthernet1/0/2
State: TCP_ESTABLISHED
Application: HTTP
Rule ID: -/-/-
Rule name:
Start time: 2012-08-15 14:53:29 TTL: 3597s
Initiator->Responder: 7 packets 308 bytes
Responder->Initiator: 5 packets 312 bytes
Total sessions found: 1
Example: Configuring NAT Server for external-to-internal access
Network configuration
As shown in Figure 15, two Web servers, one FTP server and one SMTP server, are in the internal network to provide services for external users. The internal network address is 10.110.0.0/16. The company has three public IP addresses from 202.38.1.1/24 to 202.38.1.3/24.
Configure the NAT Server feature to allow the external user to use public address 202.38.1.1/24 to access the internal servers.
Procedure
# Specify IP addresses for the interfaces on the router. (Details not shown.)
# Enter interface view of GigabitEthernet 1/0/2.
<Router> system-view
[Router] interface gigabitethernet 1/0/2
# Configure a NAT server mapping to allow external users to access the FTP server by using the address 202.38.1.1 and port 21.
[Router-GigabitEthernet1/0/2] nat server protocol tcp global 202.38.1.1 21 inside 10.110.10.3 ftp
# Configure a NAT server mapping to allow external users to access the Web server 1 by using the address 202.38.1.1 and port 80.
[Router-GigabitEthernet1/0/2] nat server protocol tcp global 202.38.1.1 80 inside 10.110.10.1 http
# Configure a NAT server mapping to allow external users to access the Web server 2 by using the address 202.38.1.1 and port 8080.
[Router-GigabitEthernet1/0/2] nat server protocol tcp global 202.38.1.1 8080 inside 10.110.10.2 http
# Configure a NAT server mapping to allow external users to access the SMTP server by using the address 202.38.1.1 and port number defined by SMTP.
[Router-GigabitEthernet1/0/2] nat server protocol tcp global 202.38.1.1 smtp inside 10.110.10.4 smtp
Verifying the configuration
# Verify that the host on the external network can access the internal servers by using the public addresses. (Details not shown.)
# Display all NAT configuration and statistics.
[Router] display nat all
NAT internal server information:
Totally 4 internal servers.
Interface: GigabitEthernet1/0/2
Protocol: 6(TCP)
Global IP/port: 202.38.1.1/21
Local IP/port : 10.110.10.3/21
Rule name : ServerRule_1
NAT counting : 0
Config status : Active
Interface: GigabitEthernet1/0/2
Protocol: 6(TCP)
Global IP/port: 202.38.1.1/25
Local IP/port : 10.110.10.4/25
Rule name : ServerRule_4
NAT counting : 0
Config status : Active
Interface: GigabitEthernet1/0/2
Protocol: 6(TCP)
Global IP/port: 202.38.1.1/80
Local IP/port : 10.110.10.1/80
Rule name : ServerRule_2
NAT counting : 0
Config status : Active
Interface: GigabitEthernet1/0/2
Protocol: 6(TCP)
Global IP/port: 202.38.1.1/8080
Local IP/port : 10.110.10.2/80
Rule name : ServerRule_3
NAT counting : 0
Config status : Active
NAT logging:
Log enable : Disabled
Flow-begin : Disabled
Flow-end : Disabled
Flow-active : Disabled
Port-block-assign : Disabled
Port-block-withdraw : Disabled
Alarm : Disabled
NO-PAT IP usage : Disabled
NAT mapping behavior:
Mapping mode : Address and Port-Dependent
ACL : ---
Config status: Active
NAT ALG:
DNS : Enabled
FTP : Enabled
H323 : Enabled
ICMP-ERROR : Enabled
ILS : Enabled
MGCP : Enabled
NBT : Enabled
PPTP : Enabled
RTSP : Enabled
RSH : Enabled
SCCP : Enabled
SIP : Enabled
SQLNET : Enabled
TFTP : Enabled
XDMCP : Enabled
Static NAT load balancing: Disabled
# Display NAT sessions that are generated when the host accesses the FTP server.
[Router] display nat session verbose
Slot 0:
Total sessions found: 0
Slot 2:
Initiator:
Source IP/port: 202.38.1.10/1694
Destination IP/port: 202.38.1.1/21
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: TCP(6)
Inbound interface: GigabitEthernet1/0/2
Responder:
Source IP/port: 10.110.10.3/21
Destination IP/port: 202.38.1.10/1694
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: TCP(6)
Inbound interface: GigabitEthernet1/0/1
State: TCP_ESTABLISHED
Application: FTP
Rule ID: -/-/-
Rule name:
Start time: 2012-08-15 14:53:29 TTL: 3597s
Initiator->Responder: 7 packets 308 bytes
Responder->Initiator: 5 packets 312 bytes
Total sessions found: 1
Example: Configuring NAT Server for external-to-internal access through domain name
Network configuration
As shown in Figure 16, Web server at 10.110.10.2/24 in the internal network provides services for external users. A DNS server at 10.110.10.3/24 is used to resolve the domain name of the Web server. The company has two public IP addresses: 202.38.1.2 and 202.38.1.3.
Configure NAT Server to allow external users to access the internal Web server by using the domain name.
Requirements analysis
To meet the network requirements, you must perform the following tasks:
· Configure a NAT server mapping to map the private IP address and port of the DNS server to a public address and port. The mapping allows the external host to access the internal DNS server for domain name resolution.
· Enable ALG for DNS and configure outbound dynamic NAT to translate the private IP address of the Web server in the payload of the DNS response packet into a public IP address.
Procedure
# Specify IP addresses for the interfaces on the router. (Details not shown.)
# Enable NAT with ALG for DNS.
<Router> system-view
[Router] nat alg dns
# Configure ACL 2000, and create a rule to permit packets only from 10.110.10.2 to pass through.
[Router] acl basic 2000
[Router-acl-ipv4-basic-2000] rule permit source 10.110.10.2 0
[Router-acl-ipv4-basic-2000] quit
# Create address group 1.
[Router] nat address-group 1
# Add address 202.38.1.3 to the group.
[Router-address-group-1] address 202.38.1.3 202.38.1.3
[Router-address-group-1] quit
# Configure a NAT server mapping on GigabitEthernet 1/0/2 to map the address 202.38.1.1 to 10.110.10.3. External users can access the internal DNS server.
[Router] interface gigabitethernet 1/0/2
[Router-GigabitEthernet1/0/2] nat server protocol udp global 202.38.1.2 inside 10.110.10.3 dns
# Enable outbound NO-PAT on GigabitEthernet 1/0/2. Use the address in address group 1 to translate the private address in DNS response payload, and allow reversible NAT.
[Router-GigabitEthernet1/0/2] nat outbound 2000 address-group 1 no-pat reversible
Verifying the configuration
# Verify that the host on the external network can access the internal Web server by using the server's domain name. (Details not shown.)
# Display all NAT configuration and statistics.
[Router] display nat all
NAT address group information:
Totally 1 NAT address groups.
Address group ID: 1
Port range: 1-65535
Address information:
Start address End address
202.38.1.3 202.38.1.3
NAT outbound information:
Totally 1 NAT outbound rules.
Interface: GigabitEthernet1/0/2
ACL: 2000
Address group ID: 1
Port-preserved: N NO-PAT: Y Reversible: Y
Config status: Active
NAT internal server information:
Totally 1 internal servers.
Interface: GigabitEthernet1/0/2
Protocol: 17(UDP)
Global IP/port: 202.38.1.2/53
Local IP/port : 10.110.10.3/53
Rule name : ServerRule_1
NAT counting : 0
Config status : Active
NAT logging:
Log enable : Disabled
Flow-begin : Disabled
Flow-end : Disabled
Flow-active : Disabled
Port-block-assign : Disabled
Port-block-withdraw : Disabled
Alarm : Disabled
NO-PAT IP usage : Disabled
NAT mapping behavior:
Mapping mode : Address and Port-Dependent
ACL : ---
Config status: Active
NAT ALG:
DNS : Enabled
FTP : Enabled
H323 : Enabled
ICMP-ERROR : Enabled
ILS : Enabled
MGCP : Enabled
NBT : Enabled
PPTP : Enabled
RTSP : Enabled
RSH : Enabled
SCCP : Enabled
SIP : Enabled
SQLNET : Enabled
TFTP : Enabled
XDMCP : Enabled
Static NAT load balancing: Disabled
# Display NAT sessions that are generated when Host accesses Web server.
[Router] display nat session verbose
Slot 0:
Total sessions found: 0
Slot 2:
Initiator:
Source IP/port: 200.1.1.2/1694
Destination IP/port: 202.38.1.3/8080
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: TCP(6)
Inbound interface: GigabitEthernet1/0/2
Responder:
Source IP/port: 10.110.10.2/8080
Destination IP/port: 200.1.1.2/1694
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: TCP(6)
Inbound interface: GigabitEthernet1/0/1
State: TCP_ESTABLISHED
Application: HTTP
Rule ID: -/-/-
Rule name:
Start time: 2012-08-15 14:53:29 TTL: 3597s
Initiator->Responder: 7 packets 308 bytes
Responder->Initiator: 5 packets 312 bytes
Total sessions found: 1
Example: Configuring NAT server for external-to-internal access through domain name
Network configuration
As shown in Figure 17, an intranet uses the subnet 192.168.1.0/24. The Web server at 192.168.1.2/24 provides Web services for external users and the DNS server at 192.168.1.3/24 resolves the domain name of the Web server. The company has 3 public addresses 202.38.1.2, 202.38.1.3, and 202.38.1.4.
Configure NAT to allow external host at 192.168.1.2 in the external network to use the domain name to access the internal Web server.
Requirements analysis
To meet the network requirements, you must perform the following tasks:
· Configure NAT Server to map the private IP address and port of the DNS server to a public IP address and port. NAT Server allows the external host to access the internal DNS server for domain name resolution.
· Configure outbound dynamic NAT and enable ALG for DNS. The Web server's IP address is the same as the external host's IP address. NAT with ALG can translate the Web server's private address in the payload of the DNS response packet to a dynamically assigned public address.
· Configure inbound dynamic NAT. The external host's IP address is the same as the Web server's IP address. Inbound dynamic NAT can translate the external host's IP address into a dynamically assigned public address.
· Add a static route to the public IP address of the external host with GigabitEthernet 1/0/2 as the output interface.
Procedure
# Specify IP addresses for the interfaces on the router. (Details not shown.)
# Enable NAT with ALG for DNS.
<Router> system-view
[Router] nat alg dns
# Configure ACL 2000 to identify packets from subnet 192.168.1.0/24.
[Router] acl basic 2000
[Router-acl-ipv4-basic-2000] rule permit source 192.168.1.0 0.0.0.255
[Router-acl-ipv4-basic-2000] quit
# Create address group 1.
[Router] nat address-group 1
# Add address 202.38.1.2 to the address group.
[Router-address-group-1] address 202.38.1.2 202.38.1.2
[Router-address-group-1] quit
# Create address group 2.
[Router] nat address-group 2
# Add address 202.38.1.3 to the address group.
[Router-address-group-2] address 202.38.1.3 202.38.1.3
[Router-address-group-2] quit
# Configure NAT Server on GigabitEthernet 1/0/2 to allow external hosts to access the internal DNS server by using the address 202.38.1.4.
[Router] interface gigabitethernet 1/0/2
[Router-GigabitEthernet1/0/2] nat server protocol udp global 202.38.1.4 inside 192.168.1.3 dns
# Enable outbound NO-PAT on GigabitEthernet 1/0/2 to translate IP address of the Web server in the DNS response payload into the address in address group 1, and allow reversible NAT.
[Router-GigabitEthernet1/0/2] nat outbound 2000 address-group 1 no-pat reversible
# Enable inbound PAT on GigabitEthernet 1/0/2 to translate the source address of packets going to the internal network to the address in address group 2.
[Router-GigabitEthernet1/0/2] nat inbound 2000 address-group 2
# Configure a static route to 202.38.1.3 with GigabitEthernet 1/0/2 as the output interface and 20.2.2.2 as the next hop. (The next hop address varies by network.)
[Router] ip route-static 202.38.1.3 32 gigabitethernet 1/0/2 20.2.2.2
Verifying the configuration
# Verify that the host on the external network can use the domain name to access the internal Web server whose address is the same as the host. (Details not shown.)
# Display all NAT configuration and statistics.
[Router] display nat all
NAT address group information:
Totally 2 NAT address groups.
Address group ID: 1
Port range: 1-65535
Address information:
Start address End address
202.38.1.2 202.38.1.2
Address group ID: 2
Port range: 1-65535
Address information:
Start address End address
202.38.1.3 202.38.1.3
NAT inbound information:
Totally 1 NAT inbound rules.
Interface: GigabitEthernet1/0/2
ACL: 2000
Address group ID: 2
Add route: N NO-PAT: N Reversible: N
Config status: Active
NAT outbound information:
Totally 1 NAT outbound rules.
Interface: GigabitEthernet1/0/2
ACL: 2000
Address group ID: 1
Port-preserved: N NO-PAT: Y Reversible: Y
Config status: Active
NAT internal server information:
Totally 1 internal servers.
Interface: GigabitEthernet1/0/2
Protocol: 17(UDP)
Global IP/port: 202.38.1.4/53
Local IP/port : 200.1.1.3/53
Rule name : ServerRule_1
NAT counting : 0
Config status : Active
NAT logging:
Log enable : Disabled
Flow-begin : Disabled
Flow-end : Disabled
Flow-active : Disabled
Port-block-assign : Disabled
Port-block-withdraw : Disabled
Alarm : Disabled
NO-PAT IP usage : Disabled
NAT mapping behavior:
Mapping mode : Address and Port-Dependent
ACL : ---
Config status: Active
NAT ALG:
DNS : Enabled
FTP : Enabled
H323 : Enabled
ICMP-ERROR : Enabled
ILS : Enabled
MGCP : Enabled
NBT : Enabled
PPTP : Enabled
RTSP : Enabled
RSH : Enabled
SCCP : Enabled
SIP : Enabled
SQLNET : Enabled
TFTP : Enabled
XDMCP : Enabled
Static NAT load balancing: Disabled
# Display NAT sessions that are generated when Host accesses the Web server.
[Router] display nat session verbose
Slot 0:
Total sessions found: 0
Slot 2:
Initiator:
Source IP/port: 192.168.1.2/1694
Destination IP/port: 202.38.1.2/8080
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: TCP(6)
Inbound interface: GigabitEthernet1/0/2
Responder:
Source IP/port: 192.168.1.2/8080
Destination IP/port: 202.38.1.3/1025
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: TCP(6)
Inbound interface: GigabitEthernet1/0/1
State: TCP_ESTABLISHED
Application: HTTP
Rule ID: -/-/-
Rule name:
Start time: 2012-08-15 14:53:29 TTL: 3597s
Initiator->Responder: 7 packets 308 bytes
Responder->Initiator: 5 packets 312 bytes
Total sessions found: 1
Example: Configuring NAT hairpin in C/S mode
Network configuration
As shown in Figure 18, the internal FTP server at 192.168.1.4/24 provides services for internal and external users. The private network uses two public IP addresses 202.38.1.1 and 202.38.1.2.
Configure NAT hairpin in C/S mode to allow external and internal users to access the internal FTP server by using public IP address 202.38.1.2.
Requirements analysis
To allow external hosts to access the internal FTP server by using a public IP address, configure NAT Server on the interface connected to the external network.
To allow internal hosts to access the internal FTP server by using a public IP address, perform the following tasks:
· Enable NAT hairpin on the interface connected to the internal network.
· Configure outbound NAT on the interface where the NAT server mapping is configured. The destination address is translated by matching the NAT server mapping. The source address is translated by matching the outbound NAT.
Procedure
# Specify IP addresses for the interfaces on the router. (Details not shown.)
# Configure ACL 2000 to identify packets from subnet 192.168.1.0/24.
<Router> system-view
[Router] acl basic 2000
[Router-acl-ipv4-basic-2000] rule permit source 192.168.1.0 0.0.0.255
[Router-acl-ipv4-basic-2000] quit
# Configure a NAT server mapping on GigabitEthernet 1/0/2 to map the IP address of the FTP server to a public address, allowing external users to access the internal FTP server.
[Router] interface gigabitethernet 1/0/2
[Router-GigabitEthernet1/0/2] nat server protocol tcp global 202.38.1.2 inside 192.168.1.4 ftp
# Enable outbound NAT with Easy IP on GigabitEthernet 1/0/2 so that NAT translates the source addresses of the packets from internal hosts into the IP address of GigabitEthernet 1/0/2.
[Router-GigabitEthernet1/0/2] nat outbound 2000
# Enable NAT hairpin on GigabitEthernet 1/0/1.
[Router] interface gigabitethernet 1/0/1
[Router-GigabitEthernet1/0/1] nat hairpin enable
Verifying the configuration
# Verify that both internal and external hosts can access the internal FTP server through the public address. (Details not shown.)
# Display all NAT configuration and statistics.
[Router] display nat all
NAT outbound information:
Totally 1 NAT outbound rules.
Interface: GigabitEthernet1/0/2
ACL: 2000
Address group ID: ---
Port-preserved: N NO-PAT: N Reversible: N
Config status: Active
NAT internal server information:
Totally 1 internal servers.
Interface: GigabitEthernet1/0/2
Protocol: 6(TCP)
Global IP/port: 202.38.1.2/21
Local IP/port : 192.168.1.4/21
Rule name : ServerRule_1
NAT counting : 0
Config status : Active
NAT logging:
Log enable : Disabled
Flow-begin : Disabled
Flow-end : Disabled
Flow-active : Disabled
Port-block-assign : Disabled
Port-block-withdraw : Disabled
Alarm : Disabled
NO-PAT IP usage : Disabled
NAT hairpinning:
Totally 1 interfaces enabled with NAT hairpinning.
Interface: GigabitEthernet1/0/1
Config status: Active
NAT mapping behavior:
Mapping mode : Address and Port-Dependent
ACL : ---
Config status: Active
NAT ALG:
DNS : Enabled
FTP : Enabled
H323 : Enabled
ICMP-ERROR : Enabled
ILS : Enabled
MGCP : Enabled
NBT : Enabled
PPTP : Enabled
RTSP : Enabled
RSH : Enabled
SCCP : Enabled
SIP : Enabled
SQLNET : Enabled
TFTP : Enabled
XDMCP : Enabled
Static NAT load balancing: Disabled
# Display NAT sessions that are generated when Host A accesses the FTP server.
[Router] display nat session verbose
Slot 0:
Total sessions found: 0
Slot 2:
Initiator:
Source IP/port: 192.168.1.2/1694
Destination IP/port: 202.38.1.2/21
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: TCP(6)
Inbound interface: GigabitEthernet1/0/1
Responder:
Source IP/port: 192.168.1.4/21
Destination IP/port: 202.38.1.1/1025
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: TCP(6)
Inbound interface: GigabitEthernet1/0/1
State: TCP_ESTABLISHED
Application: FTP
Rule ID: -/-/-
Rule name:
Start time: 2012-08-15 14:53:29 TTL: 3597s
Initiator->Responder: 7 packets 308 bytes
Responder->Initiator: 5 packets 312 bytes
Example: Configuring NAT hairpin in P2P mode
Network configuration
In the P2P application, internal clients must register their IP address to the external server and the server records the registered IP addresses and port numbers of the internal clients. An internal client must request the IP address and port number of another client from the external server before accessing the client.
Configure NAT hairpin so that:
· The internal clients can register the same public address to the external server.
· The internal clients can access each other through the IP address and port number obtained from the server.
Requirements analysis
To meet the network requirements, you must perform the following tasks:
· Configure outbound dynamic PAT on the interface connected to the external network, so the internal clients can access the external server for registration.
· Configure the mapping behavior for PAT as Endpoint-Independent Mapping because the registered IP address and port number should be accessible for any source address.
· Enable NAT hairpin on the interface connected to the internal network so that internal clients can access each other through the public address.
Procedure
# Specify IP addresses for the interfaces on the router. (Details not shown.)
# Configure ACL 2000 to identify packets from subnet 192.168.1.0/24.
<Router> system-view
[Router] acl basic 2000
[Router-acl-ipv4-basic-2000] rule permit source 192.168.1.0 0.0.0.255
[Router-acl-ipv4-basic-2000] quit
# Configure outbound dynamic PAT with Easy IP on GigabitEthernet 1/0/2. The IP address of GigabitEthernet 1/0/2 is used as the public address for the source address translation of the packets from internal to external.
[Router] interface gigabitethernet 1/0/2
[Router-GigabitEthernet1/0/2] nat outbound 2000
# Configure the Endpoint-Independent Mapping mode for PAT. For packets with the same source address and port number and permitted by ACL 2000, the source address and port number are translated to the same public address and port number.
[Router] nat mapping-behavior endpoint-independent acl 2000
# Enable NAT hairpin on GigabitEthernet 1/0/1.
[Router] interface gigabitethernet 1/0/1
[Router-GigabitEthernet1/0/1] nat hairpin enable
Verifying the configuration
# Verify that Host A, Host B, and Host C can access each other after they register their IP addresses and port numbers to the external server. (Details not shown.)
# Display all NAT configuration and statistics.
[Router] display nat all
NAT outbound information:
Totally 1 NAT outbound rules.
Interface: GigabitEthernet1/0/2
ACL: 2000
Address group ID: ---
Port-preserved: N NO-PAT: N Reversible: N
Config status: Active
NAT logging:
Log enable : Disabled
Flow-begin : Disabled
Flow-end : Disabled
Flow-active : Disabled
Port-block-assign : Disabled
Port-block-withdraw : Disabled
Alarm : Disabled
NO-PAT IP usage : Disabled
NAT hairpinning:
Totally 1 interfaces enabled with NAT hairpinning.
Interface: GigabitEthernet1/0/1
Config status: Active
NAT mapping behavior:
Mapping mode : Endpoint-Independent
ACL : 2000
Config status: Active
NAT ALG:
DNS : Enabled
FTP : Enabled
H323 : Enabled
ICMP-ERROR : Enabled
ILS : Enabled
MGCP : Enabled
NBT : Enabled
PPTP : Enabled
RTSP : Enabled
RSH : Enabled
SCCP : Enabled
SIP : Enabled
SQLNET : Enabled
TFTP : Enabled
XDMCP : Enabled
Static NAT load balancing: Disabled
# Display NAT sessions that are generated when Client A accesses Client B.
[Router] display nat session verbose
Slot 0:
Total sessions found: 0
Slot 2:
Initiator:
Source IP/port: 192.168.1.3/44929
Destination IP/port: 202.38.1.3/1
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: UDP(17)
Inbound interface: GigabitEthernet1/0/1
Responder:
Source IP/port: 192.168.1.2/69
Destination IP/port: 202.38.1.3/1024
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: UDP(17)
Inbound interface: GigabitEthernet1/0/1
State: UDP_READY
Application: TFTP
Rule ID: -/-/-
Rule name:
Start time: 2012-08-15 15:53:36 TTL: 46s
Initiator->Responder: 1 packets 56 bytes
Responder->Initiator: 1 packets 72 bytes
Total sessions found: 1
Example: Configuring twice NAT
Network configuration
As shown in Figure 20, two departments are in different VPN instances with overlapping addresses. Configure twice NAT so that Host A and Host B in different departments can access each other.
Requirements analysis
This is a typical application of twice NAT. Both the source and destination addresses of packets between the two VPNs need to be translated. Configure static NAT on both interfaces connected to the VPNs on the NAT device.
Procedure
# Specify VPN instances and IP addresses for the interfaces on the router. (Details not shown.)
# Configure a static outbound NAT mapping between 192.168.1.2 in vpn 1 and 172.16.1.2 in vpn 2.
<Router> system-view
[Router] nat static outbound 192.168.1.2 vpn-instance vpn1 172.16.1.2 vpn-instance vpn2
# Configure a static outbound NAT mapping between 192.168.1.2 in vpn 2 and 172.16.2.2 in vpn 1.
[Router] nat static outbound 192.168.1.2 vpn-instance vpn2 172.16.2.2 vpn-instance vpn1
# Enable static NAT on GigabitEthernet 1/0/2.
[Router] interface gigabitethernet 1/0/2
[Router-GigabitEthernet1/0/2] nat static enable
# Enable static NAT on GigabitEthernet 1/0/1.
[Router] interface gigabitethernet 1/0/1
[Router-GigabitEthernet1/0/1] nat static enable
Verifying the configuration
# Verify that Host A and Host B can access each other. The public address for Host A is 172.16.1.2 and that for Host B is 172.16.2.2. (Details not shown.)
# Display all NAT configuration and statistics.
[Router] display nat all
Static NAT mappings:
Totally 2 outbound static NAT mappings.
IP-to-IP:
Local IP : 192.168.1.2
Global IP : 172.16.1.2
Local VPN : vpn1
Global VPN : vpn2
Config status: Active
IP-to-IP:
Local IP : 192.168.1.2
Global IP : 172.16.2.2
Local VPN : vpn2
Global VPN : vpn1
Config status: Active
Interfaces enabled with static NAT:
Totally 2 interfaces enabled with static NAT.
Interface: GigabitEthernet1/0/1
Config status: Active
Interface: GigabitEthernet1/0/2
Config status: Active
NAT logging:
Log enable : Disabled
Flow-begin : Disabled
Flow-end : Disabled
Flow-active : Disabled
Port-block-assign : Disabled
Port-block-withdraw : Disabled
Alarm : Disabled
NO-PAT IP usage : Disabled
NAT mapping behavior:
Mapping mode : Address and Port-Dependent
ACL : ---
Config status: Active
NAT ALG:
DNS : Enabled
FTP : Enabled
H323 : Enabled
ICMP-ERROR : Enabled
ILS : Enabled
MGCP : Enabled
NBT : Enabled
PPTP : Enabled
RTSP : Enabled
RSH : Enabled
SCCP : Enabled
SIP : Enabled
SQLNET : Enabled
TFTP : Enabled
XDMCP : Enabled
Static NAT load balancing: Disabled
# Display NAT sessions that are generated when Host A accesses Host B.
[Router] display nat session verbose
Slot 0:
Total sessions found: 0
Slot 2:
Initiator:
Source IP/port: 192.168.1.2/42496
Destination IP/port: 172.16.2.2/2048
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: vpn1/-/-
Protocol: ICMP(1)
Inbound interface: GigabitEthernet1/0/1
Responder:
Source IP/port: 192.168.1.2/42496
Destination IP/port: 172.16.1.2/0
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: vpn2/-/-
Protocol: ICMP(1)
Inbound interface: GigabitEthernet1/0/2
State: ICMP_REPLY
Application: INVALID
Rule ID: -/-/-
Rule name:
Start time: 2012-08-16 09:30:49 TTL: 27s
Initiator->Responder: 5 packets 420 bytes
Responder->Initiator: 5 packets 420 bytes
Total sessions found: 1
Example: Configuring load sharing NAT Server
Network configuration
As shown in Figure 21, three FTP servers are in the intranet to provide FTP services for external users. Configure NAT so that these external users use the address 202.38.1.1/16 to access the servers and the three FTP servers implement load sharing.
Procedure
# Specify IP addresses for the interfaces on the router. (Details not shown.)
# Create NAT server group 0, and add members to the group.
<Router> system-view
[Router] nat server-group 0
[Router-nat-server-group-0] inside ip 10.110.10.1 port 21
[Router-nat-server-group-0] inside ip 10.110.10.2 port 21
[Router-nat-server-group-0] inside ip 10.110.10.3 port 21
[Router-nat-server-group-0] quit
# Associate NAT server group 0 with GigabitEthernet 1/0/2 so that servers in the server group can provide FTP services.
[Router] interface gigabitethernet 1/0/2
[Router-GigabitEthernet1/0/2] nat server protocol tcp global 202.38.1.1 ftp inside server-group 0
Verifying the configuration
# Verify that external hosts can access the internal FTP server group. (Details not shown.)
# Display all NAT configuration and statistics.
[Router] display nat all
NAT server group information:
Totally 1 NAT server groups.
Group Number Inside IP Port Weight
0 10.110.10.1 21 100
10.110.10.2 21 100
10.110.10.3 21 100
NAT internal server information:
Totally 1 internal servers.
Interface: GigabitEthernet1/0/2
Protocol: 6(TCP)
Global IP/port: 202.38.1.1/21
Local IP/port : server group 0
10.110.10.1/21 (Connections: 1)
10.110.10.2/21 (Connections: 2)
10.110.10.3/21 (Connections: 2)
Rule name : ServerRule_1
NAT counting : 0
Config status : Active
NAT logging:
Log enable : Disabled
Flow-begin : Disabled
Flow-end : Disabled
Flow-active : Disabled
Port-block-assign : Disabled
Port-block-withdraw : Disabled
Alarm : Disabled
NO-PAT IP usage : Disabled
NAT mapping behavior:
Mapping mode : Address and Port-Dependent
ACL : ---
Config status: Active
NAT ALG:
DNS : Enabled
FTP : Enabled
H323 : Enabled
ICMP-ERROR : Enabled
ILS : Enabled
MGCP : Enabled
NBT : Enabled
PPTP : Enabled
RTSP : Enabled
RSH : Enabled
SCCP : Enabled
SIP : Enabled
SQLNET : Enabled
TFTP : Enabled
XDMCP : Enabled
Static NAT load balancing: Disabled
# Display NAT sessions that are generated when external hosts access an internal FTP server.
[Router] display nat session verbose
Slot 0:
Total sessions found: 0
Slot 2:
Initiator:
Source IP/port: 202.38.1.25/53957
Destination IP/port: 202.38.1.1/21
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: TCP(6)
Inbound interface: GigabitEthernet1/0/2
Responder:
Source IP/port: 10.110.10.3/21
Destination IP/port: 202.38.1.25/53957
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: TCP(6)
Inbound interface: GigabitEthernet1/0/1
State: TCP_ESTABLISHED
Application: FTP
Rule ID: -/-/-
Rule name:
Start time: 2012-08-16 11:06:07 TTL: 26s
Initiator->Responder: 1 packets 60 bytes
Responder->Initiator: 2 packets 120 bytes
Total sessions found: 1
Example: Configuring NAT DNS mapping
Network configuration
As shown in Figure 22, the internal Web server at 10.110.10.1/16 and FTP server at 10.110.10.2/16 provide services for external user. The company has three public addresses 202.38.1.1 through 202.38.1.3. The DNS server at 202.38.1.4 is on the external network.
Configure NAT so that:
· The public IP address 202.38.1.2 is used by external users to access the Web and FTP servers.
· External users can use the public address or domain name of internal servers to access them.
· Internal users can access the internal servers by using their domain names.
Requirements analysis
To meet the network requirements, perform the following tasks:
· Configure a NAT server mapping to map the public IP addresses and port numbers of the internal servers to a public address and port numbers so that external users can access the internal servers.
· Configure NAT DNS and NAT ALG so that the public IP address of the internal server in the payload of the DNS response packet can be translated to the private IP address.
Procedure
# Specify IP addresses for the interfaces on the router. (Details not shown.)
# Enable NAT ALG for DNS.
<Router> system-view
[Router] nat alg dns
# Enter interface view of GigabitEthernet 1/0/2.
[Router] interface gigabitethernet 1/0/2
# Configure a NAT server mapping to allow external hosts to access the internal Web server by using the address 202.38.1.2.
[Router-GigabitEthernet1/0/2] nat server protocol tcp global 202.38.1.2 inside 10.110.10.1 http
# Configure a NAT server mapping to allow external hosts to access the internal FTP server by using the address 202.38.1.2.
[Router-GigabitEthernet1/0/2] nat server protocol tcp global 202.38.1.2 inside 10.110.10.2 ftp
# Enable outbound NAT with Easy IP on GigabitEthernet 1/0/2.
[Router-GigabitEthernet1/0/2] nat outbound
# Configure two DNS mappings by mapping the domain name www.server.com of the Web server to 202.38.1.2, and ftp.server.com of the FTP server to 202.38.1.2.
[Router] nat dns-map domain www.server.com protocol tcp ip 202.38.1.2 port http
[Router] nat dns-map domain ftp.server.com protocol tcp ip 202.38.1.2 port ftp
[Router] quit
Verifying the configuration
# Verify that both internal and external hosts can access the internal servers by using domain names. (Details not shown.)
# Display all NAT configuration and statistics.
[Router] display nat all
NAT outbound information:
Totally 1 NAT outbound rules.
Interface: GigabitEthernet1/0/2
ACL: ---
Address group ID: ---
Port-preserved: N NO-PAT: N Reversible: N
Config status: Active
NAT internal server information:
Totally 2 internal servers.
Interface: GigabitEthernet1/0/2
Protocol: 6(TCP)
Global IP/port: 202.38.1.2/21
Local IP/port : 10.110.10.2/21
Rule name : ServerRule_2
NAT counting : 0
Config status : Active
Interface: GigabitEthernet1/0/2
Protocol: 6(TCP)
Global IP/port: 202.38.1.2/80
Local IP/port : 10.110.10.1/80
Rule name : ServerRule_1
NAT counting : 0
Config status : Active
NAT DNS mapping information:
Totally 2 NAT DNS mappings.
Domain name: ftp.server.com
Global IP : 202.38.1.2
Global port: 21
Protocol : TCP(6)
Config status: Active
Domain name: www.server.com
Global IP : 202.38.1.2
Global port: 80
Protocol : TCP(6)
Config status: Active
NAT logging:
Log enable : Disabled
Flow-begin : Disabled
Flow-end : Disabled
Flow-active : Disabled
Port-block-assign : Disabled
Port-block-withdraw : Disabled
Alarm : Disabled
NO-PAT IP usage : Disabled
NAT mapping behavior:
Mapping mode: Address and Port-Dependent
ACL : ---
Config status: Active
NAT ALG:
DNS : Enabled
FTP : Enabled
H323 : Enabled
ICMP-ERROR : Enabled
ILS : Enabled
MGCP : Enabled
NBT : Enabled
PPTP : Enabled
RTSP : Enabled
RSH : Enabled
SCCP : Enabled
SIP : Enabled
SQLNET : Enabled
TFTP : Enabled
XDMCP : Enabled
Static NAT load balancing: Disabled
# Verify that NAT sessions have been created for external host access to internal Web server.
[Router] display nat session verbose
Slot 0:
Total sessions found: 0
Slot 2:
Initiator:
Source IP/port: 202.38.1.10/63593
Destination IP/port: 202.38.1.2/80
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: TCP(6)
Inbound interface: GigabitEthernet1/0/2
Responder:
Source IP/port: 10.110.10.1/80
Destination IP/port: 202.38.1.10/63593
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: TCP(6)
Inbound interface: GigabitEthernet1/0/1
State: TCP_ESTABLISHED
Application: HTTP
Rule ID: -/-/-
Rule name:
Start time: 2012-08-26 14:53:29 TTL: 11s
Initiator->Responder: 5 packets 1145 bytes
Responder->Initiator: 3 packets 1664 bytes
Total sessions found: 1
Example: Configuring static port block mapping for NAT444
Network configuration
As shown in Figure 23, configure static NAT444 to allow users at private IP addresses 10.110.10.1 to 10.110.10.10 to use public IP address 202.38.1.100 for accessing the Internet. Configure the port range as 10001 to 15000, and set the port block size to 500.
Procedure
# Specify IP addresses for the interfaces on the router. (Details not shown.)
# Create NAT port block group 1.
<Router> system-view
[Router] nat port-block-group 1
# Add the private IP addresses from 10.110.10.1 to 10.110.10.10 to the port block group.
[Router-port-block-group-1] local-ip-address 10.110.10.1 10.110.10.10
# Add the public IP address 202.38.1.100 to the port block group.
[Router-port-block-group-1] global-ip-pool 202.38.1.100 202.38.1.100
# Set the port block size to 500.
[Router-port-block-group-1] block-size 500
# Configure the port range as 10001 to 15000.
[Router-port-block-group-1] port-range 10001 15000
[Router-port-block-group-1] quit
# Configure a static outbound port block mapping on GigabitEthernet 1/0/2.
[Router] interface gigabitethernet 1/0/2
[Router-GigabitEthernet1/0/2] nat outbound port-block-group 1
[Router-GigabitEthernet1/0/2] quit
Verifying the configuration
# Verify that users at the private IP addresses can access the Internet. (Details not shown.)
# Display all NAT configuration and statistics.
[Router] display nat all
NAT logging:
Log enable : Disabled
Flow-begin : Disabled
Flow-end : Disabled
Flow-active : Disabled
Port-block-assign : Disabled
Port-block-withdraw : Disabled
Alarm : Disabled
NO-PAT IP usage : Disabled
NAT mapping behavior:
Mapping mode : Address and Port-Dependent
ACL : ---
Config status: Active
NAT ALG:
DNS : Enabled
FTP : Enabled
H323 : Enabled
ICMP-ERROR : Enabled
ILS : Enabled
MGCP : Enabled
NBT : Enabled
PPTP : Enabled
RTSP : Enabled
RSH : Enabled
SCCP : Enabled
SIP : Enabled
SQLNET : Enabled
TFTP : Enabled
XDMCP : Enabled
NAT port block group information:
Totally 1 NAT port block groups.
Port block group 1:
Port range: 10001-15000
Block size: 500
Local IP address information:
Start address End address VPN instance
10.110.10.1 10.110.10.10 ---
Global IP pool information:
Start address End address
202.38.1.100 202.38.1.100
NAT outbound port block group information:
Totally 1 outbound port block group items.
Interface: GigabitEthernet1/0/2
port-block-group: 1
Config status : Active
Static NAT load balancing: Disabled
# Display static port block mappings.
[Router] display nat port-block static
Slot 1:
Local VPN Local IP Global IP Port block Connections
--- 10.110.10.1 202.38.1.100 10001-10500 2
--- 10.110.10.2 202.38.1.100 10501-11000 0
--- 10.110.10.3 202.38.1.100 11001-11500 0
--- 10.110.10.4 202.38.1.100 11501-12000 0
--- 10.110.10.5 202.38.1.100 12001-12500 1
--- 10.110.10.6 202.38.1.100 12501-13000 0
--- 10.110.10.7 202.38.1.100 13001-13500 0
--- 10.110.10.8 202.38.1.100 13501-14000 0
--- 10.110.10.9 202.38.1.100 14001-14500 0
--- 10.110.10.10 202.38.1.100 14501-15000 0
Total mappings found: 10
Example: Configuring dynamic port block mapping for NAT444
Network configuration
As shown in Figure 24, a company uses private IP address on network 192.168.0.0/16 and public IP addresses 202.38.1.2 and 202.38.1.3. Configure dynamic NAT444 to the following requirements:
· Only users on subnet 192.168.1.0/24 can use public IP addresses 202.38.1.2 and 202.38.1.3 to access the Internet.
· The port range for the public IP addresses is 1024 to 65535.
· The port block size is 300.
· If the ports in the assigned port block are all used, extend another port block for users.
Procedure
# Specify IP addresses for the interfaces on the router. (Details not shown.)
# Create public address group 0.
<Router> system-view
[Router] nat address-group 0
# Add the public IP addresses 202.38.1.2 and 202.38.1.3 to the NAT address group.
[Router-address-group-0] address 202.38.1.2 202.38.1.3
# Configure the port range as 1024 to 65535.
[Router-address-group-0] port-range 1024 65535
# Set the port block size to 300 and the extended port block number to 1.
[Router-address-group-0] port-block block-size 300 extended-block-number 1
[Router-address-group-0] quit
# Configure an ACL to identify packets from subnet 192.168.1.0/24.
[Router] acl basic 2000
[Router-acl-ipv4-basic-2000] rule permit source 192.168.1.0 0.0.0.255
[Router-acl-ipv4-basic-2000] quit
# Configure dynamic outbound NAT on GigabitEthernet 1/0/2.
[Router] interface gigabitethernet 1/0/2
[Router-GigabitEthernet1/0/2] nat outbound 2000 address-group 0
Verifying the configuration
# Verify that Host A can access external servers, but Host B and Host C cannot. (Details not shown.)
# Display all NAT configuration and statistics.
[Router] display nat all
NAT address group information:
Totally 1 NAT address groups.
Address group ID: 0
Port range: 1024-65535
Port block size: 300
Extended block number: 1
Address information:
Start address End address
202.38.1.2 202.38.1.3
NAT outbound information:
Totally 1 NAT outbound rules.
Interface: GigabitEthernet1/0/2
ACL: 2000
Address group ID: 0
Port-preserved: N NO-PAT: N Reversible: N
Config status: Active
NAT logging:
Log enable : Disabled
Flow-begin : Disabled
Flow-end : Disabled
Flow-active : Disabled
Port-block-assign : Disabled
Port-block-withdraw : Disabled
Alarm : Disabled
NO-PAT IP usage : Disabled
NAT mapping behavior:
Mapping mode : Address and Port-Dependent
ACL : ---
Config status: Active
NAT ALG:
DNS : Enabled
FTP : Enabled
H323 : Enabled
ICMP-ERROR : Enabled
ILS : Enabled
MGCP : Enabled
NBT : Enabled
PPTP : Enabled
RTSP : Enabled
RSH : Enabled
SCCP : Enabled
SIP : Enabled
SQLNET : Enabled
TFTP : Enabled
XDMCP : Enabled
Static NAT load balancing: Disabled
# Display NAT statistics.
[Router] display nat statistics
Total session entries: 1
Session creation rate: 0
Total EIM entries: 0
Total inbound NO-PAT entries: 0
Total outbound NO-PAT entries: 0
Total static port block entries: 0
Total dynamic port block entries: 430
Active static port block entries: 0
Active dynamic port block entries: 1
# Display the dynamic port block entries.
[Router] display nat port-block dynamic
Slot 0:
Local VPN Local IP Global IP Port block Connections
Total mappings found: 0
Slot 2:
Local VPN Local IP Global IP Port block Connections
--- 192.168.1.10 202.38.1.2 65224-65523 1
Total mappings found: 1
Example: Configuring DS-Lite B4 address translation
Network configuration
As shown in Figure 25, configure DS-Lite tunneling and NAT to allow the DS-Lite host to access the IPv4 network over the IPv6 network.
Procedure
1. Configure the AFTR:
# Specify an IPv4 address for GigabitEthernet 1/0/1.
<AFTR> system-view
[AFTR] interface gigabitethernet 1/0/1
[AFTR-GigabitEthernet1/0/1] ip address 20.1.1.1 24
[AFTR-GigabitEthernet1/0/1] quit
# Specify an IPv6 address for GigabitEthernet 1/0/2.
[AFTR] interface gigabitethernet 1/0/2
[AFTR-GigabitEthernet1/0/2] ipv6 address 1::2 64
[AFTR-GigabitEthernet1/0/2] quit
# Create a tunnel interface on the AFTR.
[AFTR] interface tunnel 2 mode ds-lite-aftr
# Specify an IP address for the tunnel interface.
[AFTR-Tunnel2] ip address 30.1.2.2 255.255.255.0
# Specify GigabitEthernet 1/0/2 as the source interface for the tunnel.
[AFTR-Tunnel2] source gigabitethernet 1/0/2
[AFTR-Tunnel2] quit
# Enable DS-Lite tunneling on GigabitEthernet 1/0/1.
[AFTR] interface gigabitethernet 1/0/1
[AFTR-GigabitEthernet1/0/1] ds-lite enable
[AFTR-GigabitEthernet1/0/1] quit
# Create public address group 0.
[AFTR] nat address-group 0
# Add public IP addresses 20.1.1.11 and 20.1.1.12 to the NAT address group.
[AFTR-address-group-0] address 20.1.1.11 20.1.1.12
# Configure the port range as 1024 to 65535.
[AFTR-address-group-0] port-range 1024 65535
# Set the port block size to 300.
[AFTR-address-group-0] port-block block-size 300
[AFTR-address-group-0] quit
# Configure an IPv6 ACL to identify packets from subnet 1::/64.
[AFTR] acl ipv6 basic 2100
[AFTR-acl-ipv4-basic-2100] rule permit source 1::/64
[AFTR-acl-ipv4-basic-2100] quit
# Configure DS-Lite B4 address translation on GigabitEthernet 1/0/1.
[AFTR] interface gigabitethernet 1/0/1
[AFTR-GigabitEthernet1/0/1] nat outbound ds-lite-b4 2100 address-group 0
[AFTR-GigabitEthernet1/0/1] quit
2. Configure the DS-Lite host:
# Configure the IPv4 and IPv6 addresses of the DS-Lite host as 10.0.0.1 and 1::1/64. (Details not shown.)
# Configure a static route to the destination IPv4 network. (Details not shown.)
Verifying the configuration
# Use the display tunnel interface command to verify that the tunnel interface is up on the AFTR. (Details not shown.)
# Verify that the DS-Lite host can ping the IPv4 application server.
C:\> ping 20.1.1.2
Pinging 20.1.1.2 with 32 bytes of data:
Reply from 20.1.1.2: bytes=32 time=51ms TTL=255
Reply from 20.1.1.2: bytes=32 time=44ms TTL=255
Reply from 20.1.1.2: bytes=32 time=1ms TTL=255
Reply from 20.1.1.2: bytes=32 time=1ms TTL=255
Ping statistics for 20.1.1.2:
Packets: Sent = 4, Received = 4, Lost = 0 (0% loss),
Approximate round trip times in milli-seconds:
Minimum = 1ms, Maximum = 51ms, Average = 24ms
# Verify that the DS-Lite B4 address translation configuration is correct.
[AFTR] display nat outbound
NAT outbound information:
Totally 1 NAT outbound rules.
Interface: GigabitEthernet1/0/1
DS-Lite B4 ACL: 2100
Address group ID: 0
Port-preserved: N NO-PAT: N Reversible: N
Config status: Active
# Verify that the DS-Lite B4 address translation configuration takes effect by checking the port block assignment.
[AFTR] display nat statistics
Slot 1:
Total session entries: 1
Session creation rate: 0
Total EIM entries: 0
Total inbound NO-PAT entries: 0
Total outbound NO-PAT entries: 0
Total static port block entries: 0
Total dynamic port block entries: 430
Active static port block entries: 0
Active dynamic port block entries: 1
# Verify that a NAT444 mapping has been created for the DS-Lite host.
[AFTR] display nat port-block dynamic ds-lite-b4
Slot 1:
Local VPN DS-Lite B4 addr Global IP Port block Connections
--- 1::1 20.1.1.11 1024-1323 1
Total mappings found: 1
Example: Configuring NAT444 gateway unified with portal user authentication
Network configuration
As shown in Figure 26, the host is directly connected to the router and accesses the external network through the router. The router acts as the access device for portal authentication and also acts as the BRAS device and NAT444 gateway. Configure the router to meet the following requirements:
· The router uses shared key expert for secure RADIUS communication, and sends usernames with domain names to the RADIUS server.
· NAT444 cooperates with BRAS, and assigns a public IP address and a port block after the host passes authentication and obtains a private IP address.
· The host uses an IP address on the 10.210.0.0/24 subnet obtained through DHCP for portal authentication. Before passing portal authentication, the host can access only the portal Web server. After passing authentication, the host can access the external network.
Procedure
1. Configure the portal server. (Details not shown.)
2. Configure a RADIUS scheme:
# On the RADIUS server, set the shared key for secure communication to expert, and add a portal user account and password. (Details not shown.)
# On the router, create RADIUS scheme rad.
<Router> system-view
[Router] radius scheme rad
# Specify the IP address of the primary accounting server and the primary authentication server as 192.168.101.180.
[Router-radius-rad] primary accounting 192.168.101.180
[Router-radius-rad] primary authentication 192.168.101.180
# Set the shared key to plaintext expert for secure communication.
[Router-radius-rad] key accounting simple expert
[Router-radius-rad] key authentication simple expert
# Include domain names in the usernames sent to the RADIUS server.
[Router-radius-rad] user-name-format with-domain
[Router-radius-rad] quit
3. Configure an ISP domain:
# Create ISP domain cgn.
[Router] domain cgn
# Specify RADIUS scheme rad for portal user authentication, authorization, and accounting.
[Router-isp-cgn] authentication portal radius-scheme rad
[Router-isp-cgn] authorization portal radius-scheme rad
[Router-isp-cgn] accounting portal radius-scheme rad
# Specify the user address type as private IPv4 address.
[Router-isp-cgn] user-address-type private-ipv4
[Router-isp-cgn] quit
4. Configure portal authentication:
# Configure a portal authentication server.
[Router] portal server newpt
[Router-portal-server-newpt] ip 192.168.101.188 key simple portal
[Router-portal-server-newpt] quit
# Configure a portal Web server.
[Router] portal web-server newpt
[Router-portal-websvr-newpt] url http://192.168.101.188:8080/portal
[Router-portal-websvr-newpt] quit
# Enable direct portal authentication on GigabitEthernet 1/0/1.
[Router] interface gigabitethernet 1/0/1
[Router–GigabitEthernet1/0/1] portal enable method direct
# Specify portal Web server newpt on GigabitEthernet 1/0/1.
[Router–GigabitEthernet1/0/1] portal apply web-server newpt
# Configure the BAS-IP as 10.210.0.1 for portal packets sent from GigabitEthernet 1/0/1 to the portal authentication server.
[Router–GigabitEthernet1/0/1] portal bas-ip 10.210.0.1
[Router–GigabitEthernet1/0/1] portal domain cgn
[Router–GigabitEthernet1/0/1] quit
5. Configure NAT:
# Configure ACL 2000 to identify packets from subnet 10.210.0.0/24.
[Router] acl basic 2000
[Router-acl-ipv4-basic-2000] rule 0 permit source 10.210.0.0 0.0.0.255
[Router-acl-ipv4-basic-2000] quit
# Create address group 1. Add public address 111.8.0.200, specify the port range as 1024 to 65535, and set the port block size to 10.
[Router] nat address-group 1
[Router-address-group-1] port-block block-size 10
[Router-address-group-1] port-range 1024 65535
[Router-address-group-1] address 111.8.0.200 111.8.0.200
[Router-address-group-1] quit
# Configure outbound dynamic NAT on GigabitEthernet 1/0/2 to use address group 1 to translate packets permitted by ACL 2000.
[Router] interface gigabitethernet 1/0/2
[Router-GigabitEthernet1/0/2] ip address 111.8.0.101 255.255.255.0
[Router-GigabitEthernet1/0/2] nat outbound 2000 address-group 1
[Router-GigabitEthernet1/0/2] quit
Verifying the configuration
# Before passing the authentication, the user can access only the portal authentication page. After passing the authentication, the user can access the external network.
# Display portal user information after the user passes portal authentication by using the display portal user interface command. (Details not shown.)
# Verify that a dynamic port block mapping has been created for the user.
[Router] display nat port-block dynamic
Local VPN Local IP Global IP Port block Connections
--- 10.210.0.4 111.8.0.200 1024-1323 0
Total entries found: 1
Example: Configuring SIP on a network with two output interfaces
Network configuration
As shown in Figure 27, a company has two public IP addresses 202.38.1.2 and 202.38.2.2, and an internal SIP user uses an IP address on the 192.168.0.0/16 subnet. The router connects the Internet and the internal network of the company as a NAT gateway. The user can access SIP server A and SIP server B through GigabitEthernet 1/0/2 and GigabitEthernet 1/0/3 on the router, respectively. When the user accesses SIP server A, the router translates the source IP address in the packet into 202.38.1.2. When the user accesses SIP server B, the router translates the source IP address in the packet into 202.38.2.2.
After the user accesses SIP server A, the router generates a relation table to record the mappings of addresses in the SIP packet payloads. When the user accesses SIP server B, the router first looks up the relation table for a match to perform address translation. In this case, the router might translate the IP address in the packet payload to 202.38.1.2. Upon receiving the packet sent from the user, SIP server B returns a data packet in which the destination IP address is 202.38.1.2. Because ISP 2 does not have a route to address 202.38.1.2, the data packet sent by SIP server B cannot be forwarded normally.
To avoid such an issue, enable relation entry matching by the destination IP address for SIP on the router. With this feature enabled, the router matches the source IP address, source port number, and destination address in data packets against the relation entries to avoid address translation error.
Procedure
# Specify IP addresses for the interfaces on the router. (Details not shown.)
# Configure address group 0, and add address 202.38.1.2 to the group.
<Router> system-view
[Router] nat address-group 0
[Router-address-group-0] address 202.38.1.2 202.38.1.2
[Router-address-group-0] quit
# Configure address group 1, and add address 202.38.2.2 to the group.
[Router] nat address-group 1
[Router-address-group-1] address 202.38.2.2 202.38.2.2
[Router-address-group-1] quit
# Configure ACL 2000 to identify packets from subnet 192.168.1.0/24.
[Router] acl basic 2000
[Router-acl-ipv4-basic-2000] rule permit source 192.168.1.0 0.0.0.255
[Router-acl-ipv4-basic-2000] quit
# Enable outbound dynamic PAT on GigabitEthernet 1/0/2. The source IP addresses of the packets permitted by the ACL rule are translated into the address in address group 0.
[Router] interface gigabitethernet 1/0/2
[Router-GigabitEthernet1/0/2] nat outbound 2000 address-group 0
[Router-GigabitEthernet1/0/2] quit
# Enable outbound dynamic PAT on GigabitEthernet 1/0/3. The source IP addresses of the packets permitted by the ACL rule are translated into the address in address group 1.
[Router] interface gigabitethernet 1/0/3
[Router-GigabitEthernet1/0/3] nat outbound 2000 address-group 1
[Router-GigabitEthernet1/0/3] quit
# Enable NAT ALG for SIP.
[Router] nat alg sip
# Enable relation entry matching by the destination IP address for SIP.
[Router] session relation-table match destination-ip sip enable
Verifying the configuration
# Display NAT sessions that are generated when the user accesses SIP server A.
[Router] display nat session verbose
Slot 0:
Total sessions found: 0
Slot 2:
Initiator:
Source IP/port: 192.168.1.10/5060
Destination IP/port: 200.1.1.10/5060
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: TCP(6)
Inbound interface: GigabitEthernet1/0/1
Responder:
Source IP/port: 200.1.1.10/5060
Destination IP/port: 202.38.1.2/1024
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: TCP(6)
Inbound interface: GigabitEthernet1/0/2
State: TCP_ESTABLISHED
Application: SIP
Rule ID: -/-/-
Rule name:
Start time: 2022-07-08 14:53:29 TTL: 12s
Initiator->Responder: 1 packets 84 bytes
Responder->Initiator: 1 packets 84 bytes
Initiator:
Source IP/port: 192.168.1.10/1026
Destination IP/port: 200.1.1.10/1026
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: UDP(17)
Inbound interface: GigabitEthernet1/0/1
Responder:
Source IP/port: 200.1.1.10/1026
Destination IP/port: 202.38.1.2/1027
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: UDP(17)
Inbound interface: GigabitEthernet1/0/2
State: UDP_READY
Application: RTP
Rule ID: -/-/-
Rule name:
Start time: 2022-07-08 14:53:29 TTL: 12s
Initiator->Responder: 1 packets 84 bytes
Responder->Initiator: 1 packets 84 bytes
Total sessions found: 2
# Display NAT sessions that are generated when the user accesses SIP server B.
[Router] display nat session verbose
Slot 0:
Total sessions found: 0
Slot 2:
Initiator:
Source IP/port: 192.168.1.10/5060
Destination IP/port: 200.2.1.10/5060
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: TCP(6)
Inbound interface: GigabitEthernet1/0/1
Responder:
Source IP/port: 200.2.1.10/5060
Destination IP/port: 202.38.2.2/1024
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: TCP(6)
Inbound interface: GigabitEthernet1/0/2
State: TCP_ESTABLISHED
Application: SIP
Rule ID: -/-/-
Rule name:
Start time: 2022-07-08 14:53:29 TTL: 12s
Initiator->Responder: 1 packets 84 bytes
Responder->Initiator: 1 packets 84 bytes
Initiator:
Source IP/port: 192.168.1.10/1026
Destination IP/port: 200.2.1.10/1026
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: UDP(17)
Inbound interface: GigabitEthernet1/0/1
Responder:
Source IP/port: 200.2.1.10/1026
Destination IP/port: 202.38.2.2/1027
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: UDP(17)
Inbound interface: GigabitEthernet1/0/2
State: UDP_READY
Application: RTP
Rule ID: -/-/-
Rule name:
Start time: 2022-07-08 14:53:29 TTL: 12s
Initiator->Responder: 1 packets 84 bytes
Responder->Initiator: 1 packets 84 bytes
Total sessions found: 2