About networks
You can create private networks on the private cloud to provide secure, isolated, and autonomous virtual network environments for cloud hosts.
You can create multiple subnets in a network, create a router, and attach the subnets to the router to enable the subnets to communicate with each other. You can assign a public IP address to the router and attach a firewall to the router to enable the subnets to access the Internet and provide protection to the communication between cloud hosts and between cloud hosts and the external network. You can also customize inner- and inter-security group access rules to further improve the network security.
|
To use the router, load balancer, firewall, public IP address, and public IP address pool services, deploy the UIS-Sec component. |
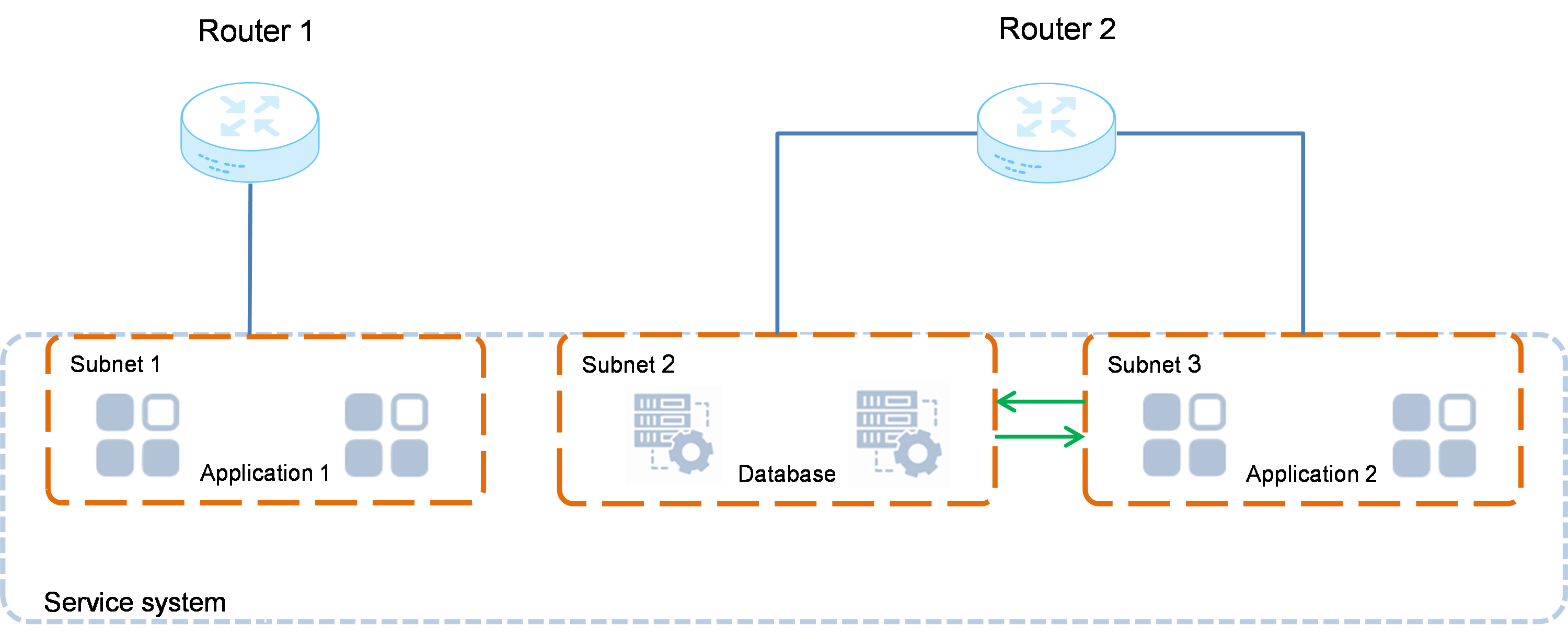
Isolation and communication between service systems
The service systems of different subnets are isolated from each other. You can isolate services by adding them to different subnets. To allow communication of services in some subnets, attach the subnets to the same router.
Figure-1 Isolation and communication between service systems
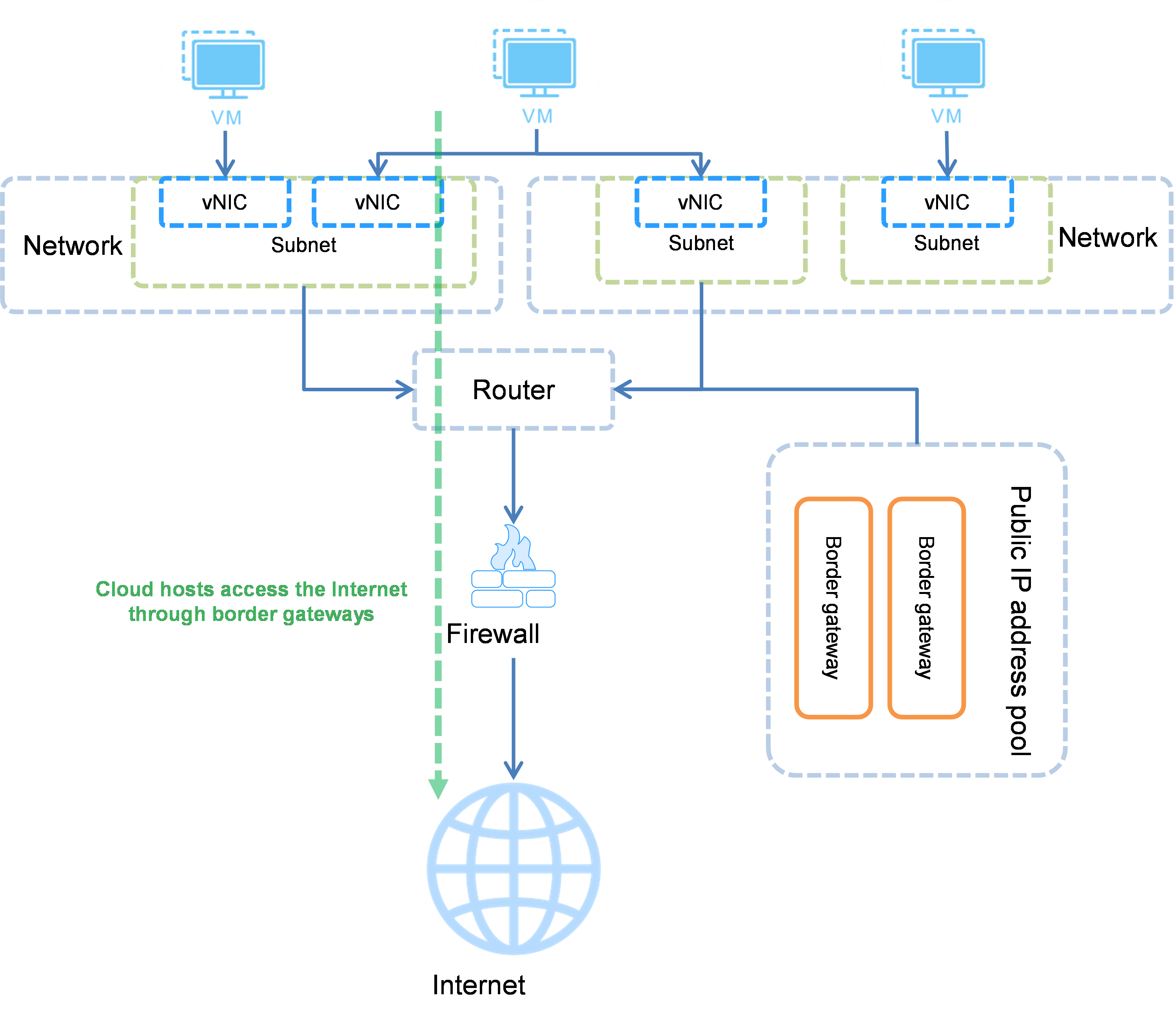
Cloud hosts accessing the public network
To enable applications on a cloud host to access the public network, configure a border gateway for the router to which the subnet of the cloud host is attached, and bind the router to a firewall. Then, all applications on the cloud hosts in the subnet can access the public network through the border gateway.
Figure-2 Cloud hosts accessing the public network
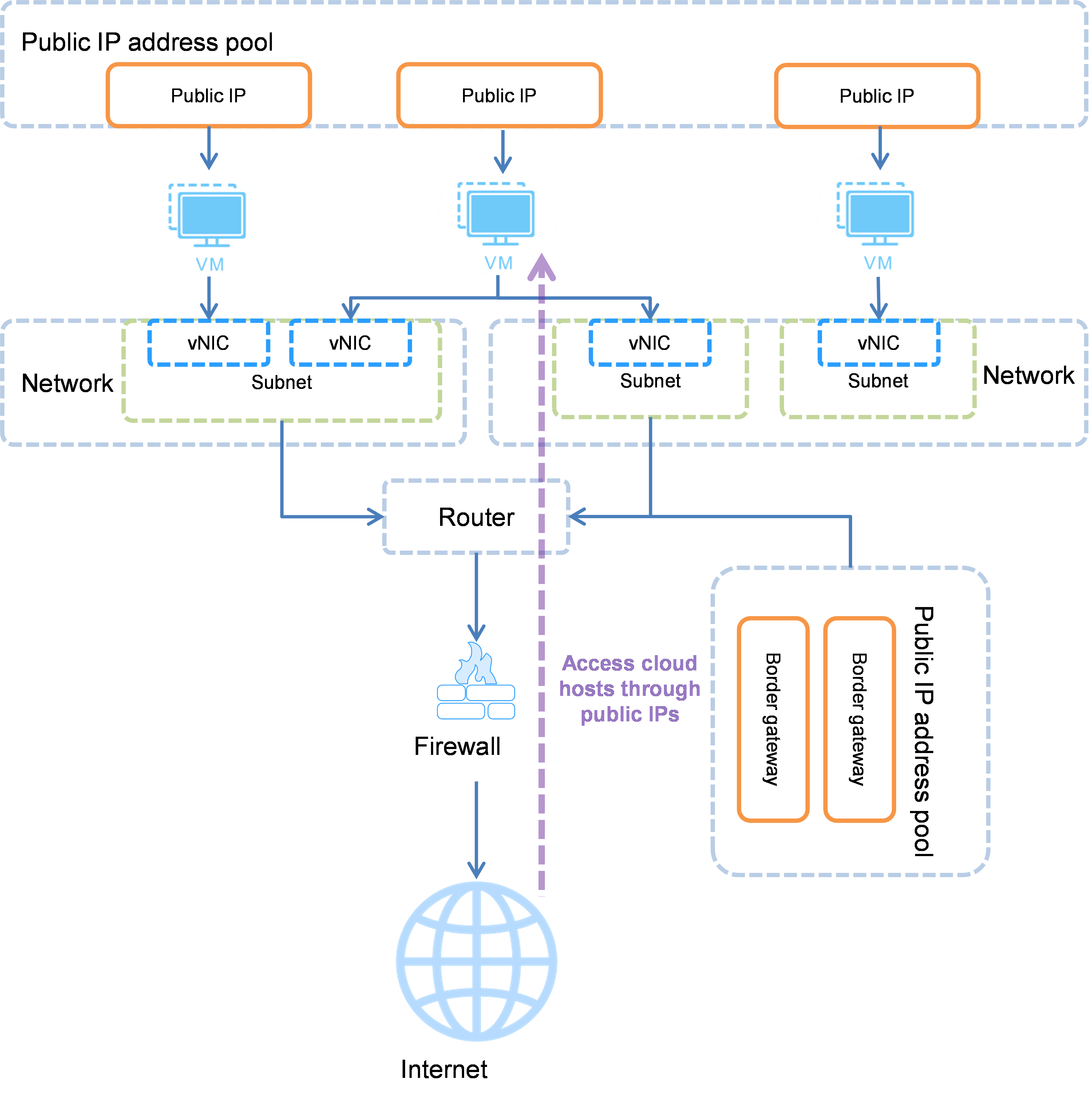
Public network accessing cloud hosts
To enable the public network to access a cloud host, assign a public IP address to the cloud host, configure a border gateway for the router to which the subnet of the cloud host is attached, and attach the router to a firewall. Then, the public network can access the cloud host through the public IP address.
Figure-3 Public network accessing cloud hosts
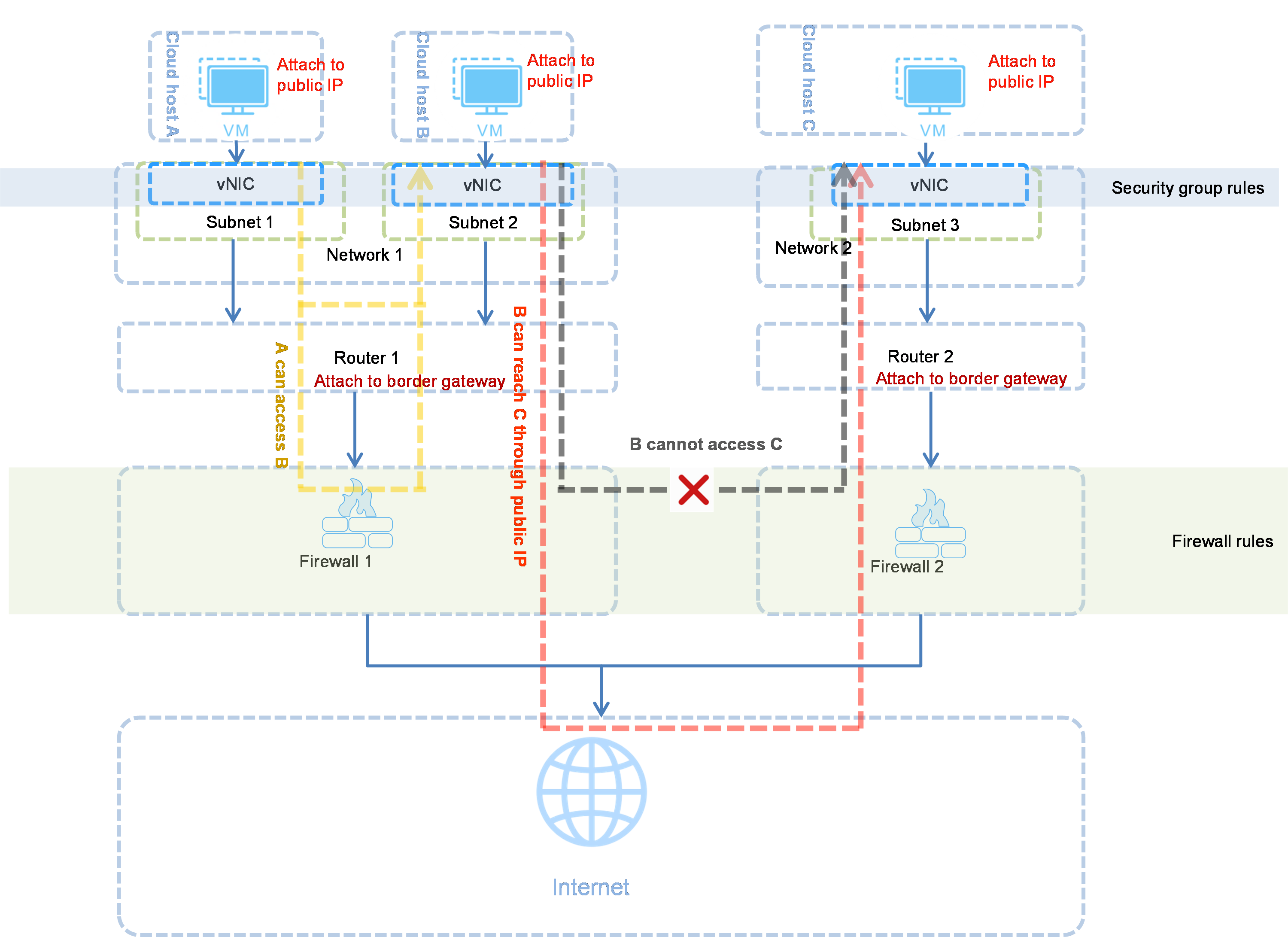
Cloud host protection
You can protect cloud hosts by configuring private networks, security groups, and firewalls.
Cloud hosts in the same private network can communicate with each other by default. To enable cloud hosts in different private networks to communicate with each other, you must configure firewall and public IP services.
You can assign cloud hosts in the same or different subnets attached to the same router to different security groups to further improve the cloud host security. You can create various access rules to control traffic received and sent by the cloud hosts. Traffic that does not match the access rules will be denied. A security group protects a cloud host immediately after the cloud host is added to the security group.
You can attach firewalls to routers to protect the communication between cloud hosts and between cloud hosts and the external network. Firewalls can be applied to scenarios that require high security.
Figure-4 Cloud host protection
Relationship with other cloud services
Hosts
The network service provides secure and isolated private network environments for cloud hosts in the private cloud.
vNICs
Cloud hosts use vNICs for communication in private networks. When you create a cloud host in a network, the system automatically creates a vNIC in the network. You can attach multiple vNICs of the same or different networks to a cloud host.
Public IP address pools
Public IP address pools provide public IP addresses to cloud hosts.
You can attach a router to a public IP address pool to configure a border gateway and attach the router to a firewall to enable cloud hosts in the subnets attached to the router to access the Internet.
You can assign public IP addresses to cloud hosts and configure a border gateway for the corresponding router to enable the Internet to access the cloud hosts.
Security groups
A security group is a logical group comprised of cloud hosts that trust each other and have the same security protection requirements. A security group protects a cloud host immediately after the cloud host is added to the security group.
Firewalls
Firewalls protect the communication between cloud hosts and between cloud hosts and the external network. To enable subnets in a network to communicate with the external network, you must attach the corresponding router to a firewall.
Load balancers
A load balancer distributes access traffic to multiple cloud hosts.
Concepts
Subnet
The cloud administrator can configure subnets and assign the subnets to organizations on the resource quota management page. You can create multiple subnets in a network to provide private IP addresses to cloud hosts with different service requirements.
Router
Routers provide source network address translation (SNAT) services to subnets. SNAT translates an IP address in the IP packet header to another IP address. For example, when a cloud host accesses the external network through a router, the router uses a public IP address to replace the source IP addresses in the packets sent by the cloud host and then records the mapping. When the external network sends a packet to the cloud host, the router replaces the destination address in the packet to the private IP address of the cloud host based on the recorded mapping and then forwards the packet to the cloud host.
QoS
QoS refers to quality of service. The factors that affect quality of network services include transport bandwidth, delay, and packet loss rate. On UIS Cloud, you can configure QoS policies to control network bandwidth for cloud hosts. Each QoS policy contains one bandwidth limit rule. QoS policies help you to improve the network resource usage.