- Table of Contents
-
- 03-Layer 2 Configuration Guide
- 00-Preface
- 01-Ethernet Interface Configuration
- 02-Loopback and Null Interface Configuration
- 03-MAC Address Table Configuration
- 04-Spanning Tree Configuration
- 05-Loopback Detection Configuration
- 06-VLAN Configuration
- 07-Layer 2 Forwarding Configuration
- 08-PPP Configuration
- 09-Ethernet Link Aggregation Configuration
- 10-DCC Configuration
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 04-Spanning Tree Configuration | 503.58 KB |
Configuring spanning tree protocols·
Implementation of MSTP on devices
Spanning tree configuration task lists
Configuration restrictions and guidelines
Setting the spanning tree mode
Configuring the root bridge or a secondary root bridge
Configuring the current device as the root bridge of a specific spanning tree
Configuring the current device as a secondary root bridge of a specific spanning tree
Configuring the device priority
Configuring the maximum hops of an MST region
Configuring the network diameter of a switched network
Configuring spanning tree timers
Configuring the timeout factor
Configuring the maximum port rate
Configuration restrictions and guidelines
Configuring path costs of ports
Specifying a standard for the device to use when it calculates the default path cost
Configuring path costs of ports
Configuring the port link type
Configuration restrictions and guidelines
Configuring the mode a port uses to recognize and send MSTP packets
Enabling the spanning tree feature
Performing mCheck in interface view
Configuration restrictions and guidelines
Digest snooping configuration example
Configuring No Agreement Check
No Agreement Check configuration example
Configuring protection functions
Displaying and maintaining the spanning tree
As a Layer 2 management protocol, the Spanning Tree Protocol (STP) eliminates Layer 2 loops by selectively blocking redundant links in a network, putting them in a standby state, which still allows for link redundancy.
The recent versions of STP include the Rapid Spanning Tree Protocol (RSTP) and the Multiple Spanning Tree Protocol (MSTP).
STP
STP was developed based on the 802.1d standard of IEEE to eliminate loops at the data link layer in a LAN. Networks often have redundant links as backups in case of failures, but loops are a very serious problem. Devices that run STP detect loops in the network by exchanging information with one another, and eliminate loops by selectively blocking certain ports to prune the loop structure into a loop-free tree structure. This avoids proliferation and infinite cycling of packets that would occur in a loop network, and prevents received duplicate packets from decreasing the performance of network devices.
In the narrow sense, STP refers to IEEE 802.1d STP. In the broad sense, STP refers to the IEEE 802.1d STP and various improved spanning tree protocols derived from that protocol.
STP protocol packets
STP uses bridge protocol data units (BPDUs), also known as configuration messages, as its protocol packets. This chapter uses BPDU to represent all types of spanning tree protocol packet.
STP-enabled network devices exchange BPDUs to establish a spanning tree. BPDUs contain sufficient information for network devices to complete spanning tree calculations.
STP uses the following types of BPDUs:
· Configuration BPDUs—Used by network devices to calculate a spanning tree and maintain spanning tree topology.
· Topology change notification (TCN) BPDUs—Used to notify network devices of network topology changes.
Configuration BPDUs contain sufficient information for network devices to complete spanning tree calculations. Important fields in a configuration BPDU include the following:
· Root bridge ID—Comprises the priority and MAC address of the root bridge.
· Root path cost—The cost of the path to the root bridge.
· Designated bridge ID—Comprises the priority and MAC address of the designated bridge.
· Designated port ID—Comprises port priority and global port number.
· Message age—The times that the configuration BPDU has been forwarded on the network.
· Max age—The maximum age of the configuration BPDU.
· Hello time—The transmission interval of the configuration BPDU.
· Forward delay—The delay before a port transitions to the forwarding state.
Basic concepts in STP
Root bridge
A tree network must have a root bridge.
There is only one root bridge in the entire network. The entire network contains only one root bridge. All the other bridges in the network are called "leaf nodes." The root bridge is not permanent, but can change when the network topology changes.
Upon initialization of a network, each device generates and periodically sends configuration BPDUs with itself as the root bridge. After network convergence, only the root bridge generates and periodically sends configuration BPDUs. The other devices only forward BPDUs.
Root port
Designated bridge and designated port
Table 1 Description of designated bridges and designated ports
|
Classification |
Designated bridge |
Designated port |
|
For a device |
Device directly connected with the local device and responsible for forwarding BPDUs to the local device. |
Port through which the designated bridge forwards BPDUs to this device. |
|
For a LAN |
Device responsible for forwarding BPDUs to this LAN segment. |
Port through which the designated bridge forwards BPDUs to this LAN segment. |
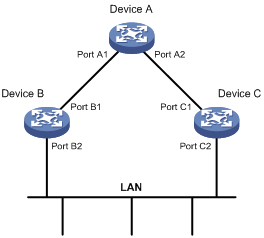
As shown in Figure 1, Device B and Device C are directly connected to a LAN. If Device A forwards BPDUs to Device B through port A1, the designated bridge for Device B is Device A, and the designated port of Device B is port A1 on Device A. If Device B forwards BPDUs to the LAN, the designated bridge for the LAN is Device B, and the designated port for the LAN is port B2 on Device B.
Figure 1 Schematic diagram of designated bridges and designated ports
Path cost
Path cost is a reference value used for link selection in STP. STP calculates path costs to select the most robust links and block redundant links that are less robust, to prune the network into a loop-free tree.
STP algorithm
The spanning tree calculation process described in the following sections is a simplified process for example only.
Calculation process
The STP algorithm uses the following calculation process:
1. Initialize the state.
2. Select the root bridge.
Initially, each STP-enabled device on the network assumes itself to be the root bridge, with its own device ID as the root bridge ID. By exchanging configuration BPDUs, the devices compare their root bridge IDs to elect the device with the smallest root bridge ID as the root bridge.
3. Select root ports and designated ports on non-root bridges.
When the network topology is stable, only the root port and designated ports forward user traffic, while other ports are all in the blocked state to receive BPDUs but not to forward BPDUs or user traffic. Table 2 shows the selection of the root ports and designated ports.
Table 2 Selection of the root port and designated ports
|
Step |
Description |
|
1 |
A non-root-bridge device regards the port on which it received the optimum configuration BPDU as the root port. Table 3 describes how the optimum configuration BPDU is selected. |
|
2 |
Based on the configuration BPDU and the path cost of the root port, the device calculates a designated port configuration BPDU for each of the other ports: · The root bridge ID is replaced with that of the configuration BPDU of the root port. · The root path cost is replaced with that of the configuration BPDU of the root port plus the path cost of the root port. · The designated bridge ID is replaced with the ID of this device. · The designated port ID is replaced with the ID of this port. |
|
3 |
The device compares the calculated configuration BPDU with the configuration BPDU on the port whose port role will be defined: · If the calculated configuration BPDU is superior, the device considers this port as the designated port, replaces the configuration BPDU on the port with the calculated configuration BPDU, and periodically sends the calculated configuration BPDU. · If the configuration BPDU on the port is superior, the device blocks this port without updating its configuration BPDU. The blocked port can receive BPDUs, but cannot send BPDUs or forward data traffic. |
Table 3 Selection of the optimum configuration BPDU
|
Step |
Actions |
|
1 |
Upon receiving a configuration BPDU on a port, the device compares the priority of the received configuration BPDU with that of the configuration BPDU generated by the port, and: · If the former priority is lower, the device discards the received configuration BPDU and keeps the configuration BPDU that the port generated. · If the former priority is higher, the device replaces the content of the configuration BPDU generated by the port with the content of the received configuration BPDU. |
|
2 |
The device compares the configuration BPDUs of all ports and chooses the optimum configuration BPDU. |
The following are the principles of configuration BPDU comparison:
· The configuration BPDU with the lowest root bridge ID has the highest priority.
· If configuration BPDUs have the same root bridge ID, their root path costs are compared. For example, the root path cost in a configuration BPDU plus the path cost of a receiving port is S. The configuration BPDU with the smallest S value has the highest priority.
· If all configuration BPDUs have the same ports value, their designated bridge IDs, designated port IDs, and the IDs of the receiving ports are compared in sequence. The configuration BPDU that contains the smallest ID wins.
A tree-shape topology forms when the root bridge, root ports, and designated ports are selected.
An example of STP algorithm calculations
Figure 2 provides an example of how the STP algorithm works.
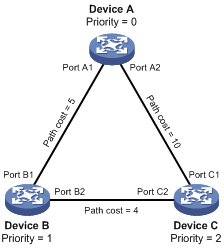
As shown in Figure 2, the priority values of Device A, Device B, and Device C are 0, 1, and 2, and the path costs of links among the three devices are 5, 10, and 4, respectively.
1. Initialize the state on each device.
In Table 4, each configuration BPDU contains the following fields: root bridge ID, root path cost, designated bridge ID, and designated port ID.
Table 4 Initial state of each device
|
Device |
Port name |
Configuration BPDU on the port |
|
Device A |
Port A1 |
{0, 0, 0, Port A1} |
|
Port A2 |
{0, 0, 0, Port A2} |
|
|
Device B |
Port B1 |
{1, 0, 1, Port B1} |
|
Port B2 |
{1, 0, 1, Port B2} |
|
|
Device C |
Port C1 |
{2, 0, 2, Port C1} |
|
Port C2 |
{2, 0, 2, Port C2} |
2. Compare BPDUs on each device.
In Table 5, each configuration BPDU contains the following fields: root bridge ID, root path cost, designated bridge ID, and designated port ID.
Table 5 Comparison process and result on each device
|
Device |
Comparison process |
Configuration BPDU on ports after comparison |
|
Device A |
· Port A1 receives the configuration BPDU of Port B1 {1, 0, 1, Port B1}, finds that its existing configuration BPDU {0, 0, 0, Port A1} is superior to the received configuration BPDU, and discards the received one. · Port A2 receives the configuration BPDU of Port C1 {2, 0, 2, Port C1}, finds that its existing configuration BPDU {0, 0, 0, Port A2} is superior to the received configuration BPDU, and discards the received one. · Device A finds that it is both the root bridge and designated bridge in the configuration BPDUs of all its ports, and considers itself as the root bridge. It does not change the configuration BPDU of any port and starts to periodically send configuration BPDUs. |
· Port A1: {0, 0, 0, Port A1} · Port A2: {0, 0, 0, Port A2} |
|
Device B |
· Port B1 receives the configuration BPDU of Port A1 {0, 0, 0, Port A1}, finds that the received configuration BPDU is superior to its existing configuration BPDU {1, 0, 1, Port B1}, and updates its configuration BPDU. · Port B2 receives the configuration BPDU of Port C2 {2, 0, 2, Port C2}, finds that its existing configuration BPDU {1, 0, 1, Port B2} is superior to the received configuration BPDU, and discards the received one. |
· Port B1: {0, 0, 0, Port A1} · Port B2: {1, 0, 1, Port B2} |
|
· Device B compares the configuration BPDUs of all its ports, decides that the configuration BPDU of Port B1 is the optimum, and selects Port B1 as the root port with the configuration BPDU unchanged. · Based on the configuration BPDU and path cost of the root port, Device B calculates a designated port configuration BPDU for Port B2 {0, 5, 1, Port B2}, and compares it with the existing configuration BPDU of Port B2 {1, 0, 1, Port B2}. Device B finds that the calculated one is superior, decides that Port B2 is the designated port, replaces the configuration BPDU on Port B2 with the calculated one, and periodically sends the calculated configuration BPDU. |
· Root port (Port B1): {0, 0, 0, Port A1} · Designated port (Port B2): {0, 5, 1, Port B2} |
|
|
Device C |
· Port C1 receives the configuration BPDU of Port A2 {0, 0, 0, Port A2}, finds that the received configuration BPDU is superior to its existing configuration BPDU {2, 0, 2, Port C1}, and updates its configuration BPDU. · Port C2 receives the original configuration BPDU of Port B2 {1, 0, 1, Port B2}, finds that the received configuration BPDU is superior to the existing configuration BPDU {2, 0, 2, Port C2}, and updates its configuration BPDU. |
· Port C1: {0, 0, 0, Port A2} · Port C2: {1, 0, 1, Port B2} |
|
· Device C compares the configuration BPDUs of all its ports, decides that the configuration BPDU of Port C1 is the optimum, and selects Port C1 as the root port with the configuration BPDU unchanged. · Based on the configuration BPDU and path cost of the root port, Device C calculates the configuration BPDU of Port C2 {0, 10, 2, Port C2}, and compares it with the existing configuration BPDU of Port C2 {1, 0, 1, Port B2}. Device C finds that the calculated configuration BPDU is superior to the existing one, selects Port C2 as the designated port, and replaces the configuration BPDU of Port C2 with the calculated one. |
· Root port (Port C1): {0, 0, 0, Port A2} · Designated port (Port C2): {0, 10, 2, Port C2} |
|
|
· Port C2 receives the updated configuration BPDU of Port B2 {0, 5, 1, Port B2}, finds that the received configuration BPDU is superior to its existing configuration BPDU {0, 10, 2, Port C2}, and updates its configuration BPDU. · Port C1 receives a periodic configuration BPDU {0, 0, 0, Port A2} from Port A2, finds that it is the same as the existing configuration BPDU, and discards the received one. |
· Port C1: {0, 0, 0, Port A2} · Port C2: {0, 5, 1, Port B2} |
|
|
· Device C finds that the root path cost of Port C1 (10) (root path cost of the received configuration BPDU (0) plus path cost of Port C1 (10)) is larger than that of Port C2 (9) (root path cost of the received configuration BPDU (5) plus path cost of Port C2 (4)), decides that the configuration BPDU of Port C2 is the optimum, and selects Port C2 as the root port with the configuration BPDU unchanged. · Based on the configuration BPDU and path cost of the root port, Device C calculates a designated port configuration BPDU for Port C1 {0, 9, 2, Port C1} and compares it with the existing configuration BPDU of Port C1 {0, 0, 0, Port A2}. Device C finds that the existing configuration BPDU is superior to the calculated one and blocks Port C1 with the configuration BPDU unchanged. Then Port C1 does not forward data until a new event triggers a spanning tree calculation process, for example, the link between Device B and Device C is down. |
· Blocked port (Port C1): {0, 0, 0, Port A2} · Root port (Port C2): {0, 5, 1, Port B2} |
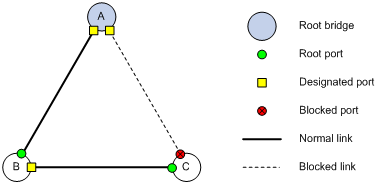
After the comparison processes described in Table 5, a spanning tree with Device A as the root bridge is established, and the new topology is shown in Figure 3.
Figure 3 The final calculated spanning tree
The configuration BPDU forwarding mechanism of STP
The configuration BPDUs of STP are forwarded according to these guidelines:
· Upon network initiation, every device regards itself as the root bridge, generates configuration BPDUs with itself as the root, and sends the configuration BPDUs at a regular hello interval.
· If the root port received a configuration BPDU and the received configuration BPDU is superior to the configuration BPDU of the port, the device increases the message age carried in the configuration BPDU following a certain rule and starts a timer to time the configuration BPDU while sending this configuration BPDU through the designated port.
· If the configuration BPDU received on a designated port has a lower priority than the configuration BPDU of the local port, the port immediately sends its own configuration BPDU in response.
· If a path becomes faulty, the root port on this path no longer receives new configuration BPDUs and the old configuration BPDUs will be discarded due to timeout. The device generates a configuration BPDU with itself as the root and sends the BPDUs and TCN BPDUs. This triggers a new spanning tree calculation process to establish a new path to restore network connectivity.
However, the newly calculated configuration BPDU cannot be propagated throughout the network immediately, so the old root ports and designated ports that have not yet detected the topology change continue to forward data along the old path. If the new root ports and designated ports begin to forward data as soon as they are elected, a temporary loop might occur.
STP timers
The most important timing parameters in STP calculation are as follows:
· Forward delay—Forward delay is the delay time for port state transition.
A path failure can cause spanning tree recalculation to adapt the spanning tree structure to the change. However, the resulting new configuration BPDU cannot propagate throughout the network immediately. If the newly elected root ports and designated ports start to forward data right away, a temporary loop will likely occur.
For this reason, as a mechanism for state transition in STP, the newly elected root ports or designated ports require twice the forward delay time before they transition to the forwarding state to make sure the new configuration BPDU has propagated throughout the network.
· Hello time—The device sends hello packets at the hello time interval to neighboring devices to make sure the paths are valid.
· Max age—The device uses the max age to determine whether a stored configuration BPDU has expired, and discards it if the max age is exceeded.
RSTP
RSTP achieves rapid network convergence by allowing a newly elected root port or designated port to enter the forwarding state much faster than STP.
A newly elected RSTP root port rapidly enters the forwarding state if the old root port on the device has stopped forwarding data and the upstream designated port has started forwarding data.
A newly elected RSTP designated port rapidly enters the forwarding state if it is an edge port (which directly connects to a user terminal rather than to another network device or a shared LAN segment), or it connects to a point-to-point link (to another device). Edge ports directly enter the forwarding state. When connecting to a point-to-point link, a designated port enters the forwarding state immediately after the device receives a handshake response from the directly connected device.
MSTP
STP and RSTP limitations
STP does not support rapid state transition of ports. A newly elected port must wait twice the forward delay time before it transitions to the forwarding state, even if it connects to a point-to-point link or is an edge port.
Although RSTP supports rapid network convergence, it has the same drawback as STP. All bridges within a LAN share the same spanning tree, and packets from all VLANs are forwarded along the same spanning tree, so redundant links cannot be blocked based on VLAN, and load sharing among VLANs cannot be implemented.
MSTP features
Developed based on IEEE 802.1s, MSTP overcomes the limitations of STP and RSTP. In addition to supporting rapid network convergence, it also provides a better load sharing mechanism for redundant links by allowing data flows from different VLANs to be forwarded along separate paths.
MSTP provides the following features:
· Divides a switched network into multiple regions, each of which contains multiple spanning trees that are independent of one another.
· Supports mapping VLANs to spanning tree instances by means of a VLAN-to-instance mapping table. MSTP can reduce communication overheads and resource usage by mapping multiple VLANs to one instance.
· Prunes a looped network into a loop-free tree, which avoids proliferation and endless cycling of packets. In addition, it supports load balancing of VLAN data by providing multiple redundant paths for data forwarding.
· Compatible with STP and RSTP.
MSTP basic concepts
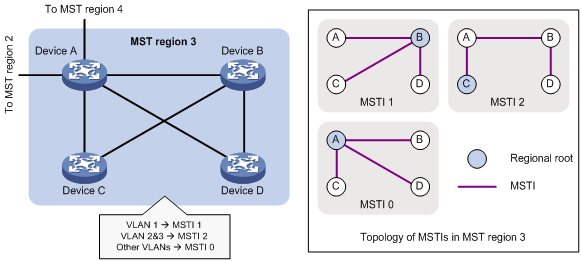
Figure 4 shows a switched network that comprises four MST regions, with each MST region comprising four MSTP devices. Figure 5 shows the network topology of MST region 3.
Figure 4 Basic concepts in MSTP
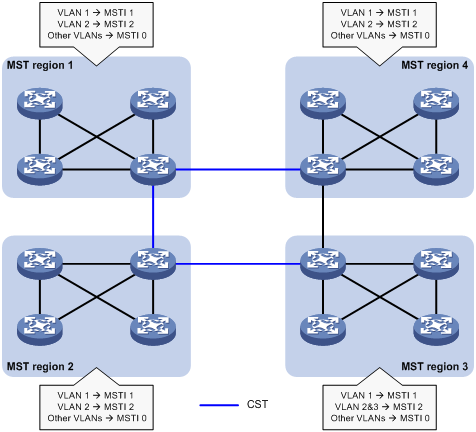
Figure 5 Network diagram and topology of MST region 3
MST region
A multiple spanning tree region (MST region) consists of multiple devices in a switched network and the network segments among them. All these devices have the following characteristics:
· A spanning tree protocol is enabled.
· Same region name.
· Same VLAN-to-instance mapping configuration.
· Same MSTP revision level.
· Physically linked together.
Multiple MST regions can exist in a switched network. You can assign multiple devices to the same MST region. In Figure 4, the switched network comprises MST region 1 through MST region 4, and all devices in each MST region have the same MST region configuration.
MSTI
MSTP can generate multiple independent spanning trees in an MST region, and each spanning tree is mapped to specific VLANs. Each spanning tree is called a "multiple spanning tree instance (MSTI)."
In Figure 5, MST region 3 comprises MSTI 1, MSTI 2, and MSTI 0.
VLAN-to-instance mapping table
As an attribute of an MST region, the VLAN-to-instance mapping table describes mapping relationships between VLANs and MSTIs.
In Figure 5, the VLAN-to-instance mapping table of MST region 3 is: VLAN 1 to MSTI 1, VLAN 2 and VLAN 3 to MSTI 2, and other VLANs to MSTI 0. MSTP achieves load balancing by means of the VLAN-to-instance mapping table.
CST
The common spanning tree (CST) is a single spanning tree that connects all MST regions in a switched network. If you regard each MST region as a device, the CST is a spanning tree calculated by these devices through STP or RSTP.
The blue lines in Figure 4 represent the CST.
IST
An internal spanning tree (IST) is a spanning tree that runs in an MST region. It is also called MSTI 0, a special MSTI to which all VLANs are mapped by default.
In Figure 4, MSTI 0 is the IST in MST region 3.
CIST
The common and internal spanning tree (CIST) is a single spanning tree that connects all devices in a switched network. It consists of the ISTs in all MST regions and the CST.
In Figure 4, the ISTs (MSTI 0) in all MST regions plus the inter-region CST constitute the CIST of the entire network.
Regional root
The root bridge of the IST or an MSTI within an MST region is the regional root of the IST or MSTI. Based on the topology, different spanning trees in an MST region might have different regional roots.
In MST region 3 in Figure 5, the regional root of MSTI 1 is Device B, the regional root of MSTI 2 is Device C, and the regional root of MSTI 0 (also known as the IST) is Device A.
Common root bridge
The common root bridge is the root bridge of the CIST.
In Figure 4, the common root bridge is a device in MST region 1.
Port roles
A port can play different roles in different MSTIs. As shown in Figure 6, an MST region comprises Device A, Device B, Device C, and Device D. Port A1 and port A2 of Device A connect to the common root bridge. Port B2 and Port B3 of Device B form a loop. Port C3 and Port C4 of Device C connect to other MST regions. Port D3 of Device D directly connects to a host.
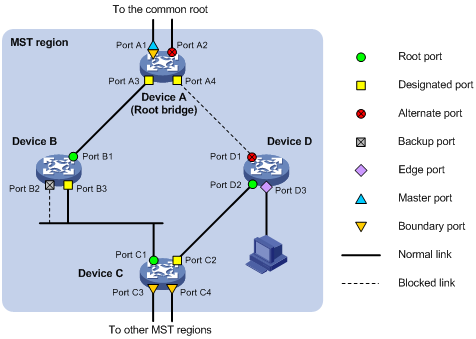
MSTP calculation involves the following port roles:
· Root port—Forwards data for a non-root bridge to the root bridge. The root bridge does not have any root port.
· Designated port—Forwards data to the downstream network segment or device.
· Alternate port—The backup port for a root port or master port. When the root port or master port is blocked, the alternate port takes over.
· Backup port—The backup port of a designated port. When the designated port is invalid, the backup port becomes the new designated port. A loop occurs when two ports of the same spanning tree device are interconnected, so the device blocks one of the ports. The blocked port acts as the backup.
· Edge port—An edge port does not connect to any network device or network segment, but directly connects to a user host.
· Master port—A port on the shortest path from the local MST region to the common root bridge. The master port is not always located on the regional root. It is a root port on the IST or CIST and still a master port on other MSTIs.
· Boundary port—Connects an MST region to another MST region or to an STP/RSTP-running device. In MSTP calculation, a boundary port's role on an MSTI is consistent with its role on the CIST. But that is not true with master ports. A master port on MSTIs is a root port on the CIST.
Port states
In MSTP, a port can be in one of the following states:
· Forwarding—The port receives and sends BPDUs, learns MAC addresses, and forwards user traffic.
· Learning—The port receives and sends BPDUs, learns MAC addresses, but does not forward user traffic. Learning is an intermediate port state.
· Discarding—The port receives and sends BPDUs, but does not learn MAC addresses or forward user traffic.
When in different MSTIs, a port can be in different states. A port state is not exclusively associated with a port role. Table 6 lists port states that each port role supports. A check mark [√] indicates that the port supports this state, while a dash [—] indicates that the port does not support this state.
Table 6 Port states that different port roles support
|
Port role (right) Port state (below) |
Root port/master port |
Designated port |
Alternate port |
Backup port |
|
Forwarding |
√ |
√ |
— |
— |
|
Learning |
√ |
√ |
— |
— |
|
Discarding |
√ |
√ |
√ |
√ |
How MSTP works
MSTP divides an entire Layer 2 network into multiple MST regions, which are connected by a calculated CST. Inside an MST region, multiple spanning trees are calculated. Each spanning tree is called an "MSTI." Among these MSTIs, MSTI 0 is the IST.
Like STP, MSTP uses configuration BPDUs to calculate spanning trees. An important difference is that an MSTP BPDU carries the MSTP configuration of the bridge from which the BPDU is sent.
CIST calculation
The calculation of a CIST tree is also the process of configuration BPDU comparison. During this process, the device with the highest priority is elected as the root bridge of the CIST. MSTP generates an IST within each MST region through calculation. At the same time, MSTP regards each MST region as a single device and generates a CST among these MST regions through calculation. The CST and ISTs constitute the CIST of the entire network.
MSTI calculation
Within an MST region, MSTP generates different MSTIs for different VLANs based on VLAN-to-instance mappings. For each spanning tree, MSTP performs a separate calculation process similar to spanning tree calculation in STP. For more information, see "STP algorithm."
In MSTP, a VLAN packet is forwarded along the following paths:
· Within an MST region, the packet is forwarded along the corresponding MSTI.
· Between two MST regions, the packet is forwarded along the CST.
Implementation of MSTP on devices
MSTP is compatible with STP and RSTP. Devices that run MSTP can recognize STP and RSTP protocol packets used for spanning tree calculation.
In addition to basic MSTP functions, the following functions are provided for ease of management:
· Root bridge hold
· Root bridge backup
· Root guard
· BPDU guard
· TC-BPDU guard
Protocols and standards
· IEEE 802.1d, Media Access Control (MAC) Bridges
· IEEE 802.1w, Part 3: Media Access Control (MAC) Bridges—Amendment 2: Rapid Reconfiguration
· IEEE 802.1s, Virtual Bridged Local Area Networks—Amendment 3: Multiple Spanning Trees
Spanning tree configuration task lists
Configuration prerequisites
Before configuring a spanning tree, you must determine the spanning tree protocol to be used (STP, RSTP, or MSTP) and plan device roles (the root bridge or leaf node).
Configuration restrictions and guidelines
· The spanning tree configurations made in system view take effect globally. Configurations made in Ethernet interface view take effect on the interface only. Configurations made in port group view take effect on all member ports in the port group. Configurations made in Layer 2 aggregate interface view take effect only on the aggregate interface. Configurations made on an aggregation member port can take effect only after the port is removed from the aggregation group.
· After you enable a spanning tree protocol on a Layer 2 aggregate interface, the system performs spanning tree calculation on the Layer 2 aggregate interface but not on the aggregation member ports. The spanning tree protocol enable state and forwarding state of each selected member port is consistent with those of the corresponding Layer 2 aggregate interface.
· Though the member ports of an aggregation group do not participate in spanning tree calculation, the ports still reserve their spanning tree configurations for participating in spanning tree calculation after leaving the aggregation group.
STP configuration task list
|
Task |
Remarks |
|
|
Configuring the root bridge |
Required. Configure the device to operate in STP mode. |
|
|
Optional. |
||
|
Optional. |
||
|
Optional. |
||
|
Optional. |
||
|
Optional. |
||
|
Optional. |
||
|
Configuring the mode a port uses to recognize and send MSTP packets |
Optional. |
|
|
Required. |
||
|
Configuring the leaf nodes |
Required. Configure the device to operate in STP mode. |
|
|
Optional. |
||
|
Optional. |
||
|
Optional. |
||
|
Optional. |
||
|
Optional. |
||
|
Configuring the mode a port uses to recognize and send MSTP packets |
Optional. |
|
|
Required. |
||
|
Optional. |
||
RSTP configuration task list
|
Task |
Remarks |
|
|
Configuring the root bridge |
Required. Configure the device to operate in RSTP mode. |
|
|
Optional. |
||
|
Optional. |
||
|
Optional. |
||
|
Optional. |
||
|
Optional. |
||
|
Optional. |
||
|
Optional. |
||
|
Optional. |
||
|
Configuring the mode a port uses to recognize and send MSTP packets |
Optional. |
|
|
Required. |
||
|
Configuring the leaf nodes |
Required. Configure the device to operate in RSTP mode. |
|
|
Optional. |
||
|
Optional. |
||
|
Optional. |
||
|
Optional. |
||
|
Optional. |
||
|
Optional. |
||
|
Optional. |
||
|
Configuring the mode a port uses to recognize and send MSTP packets |
Optional. |
|
|
Required. |
||
|
Optional. |
||
|
Optional. |
||
MSTP configuration task list
|
Task |
Remarks |
|
|
Configuring the root bridge |
Optional. By default, the device operates in MSTP mode. |
|
|
Required. |
||
|
Optional. |
||
|
Optional. |
||
|
Optional. |
||
|
Optional. |
||
|
Optional. |
||
|
Optional. |
||
|
Optional. |
||
|
Optional. |
||
|
Optional. |
||
|
Configuring the mode a port uses to recognize and send MSTP packets |
Optional. |
|
|
Required. |
||
|
Configuring the leaf nodes |
Optional. By default, the device operates in MSTP mode. |
|
|
Required. |
||
|
Optional. |
||
|
Optional. |
||
|
Optional. |
||
|
Optional. |
||
|
Optional. |
||
|
Optional. |
||
|
Optional. |
||
|
Configuring the mode a port uses to recognize and send MSTP packets |
Optional. |
|
|
Required. |
||
|
Optional. |
||
|
Optional. |
||
|
Optional. |
||
|
Optional. |
||
Setting the spanning tree mode
The spanning tree includes the following modes:
· STP mode—All ports of the device send STP BPDUs. Select this mode when the peer device of a port supports only STP.
· RSTP mode—All ports of the device send RSTP BPDUs. When an RSTP port receives STP BPDUs from a peer device, it automatically transitions to STP mode. When an RSTP port receives MSTP BPDUs from a peer device, it stays in RSTP mode.
· MSTP mode—All ports of the device send MSTP BPDUs. When an MSTP port receives STP BPDUs from a peer device, it automatically transitions to STP mode. When an MSTP port receives RSTP BPDUs from a peer device, it stays in MSTP mode.
MSTP mode is compatible with RSTP mode, and RSTP mode is compatible with STP mode.
To set the spanning tree mode:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Set the spanning tree mode. |
stp mode { mstp | rstp | stp } |
The default setting is MSTP mode. |
Configuring an MST region
Two or more spanning tree devices belong to the same MST region only if they are configured to have the same format selector (0 by default, not configurable), MST region name, MST region revision level, and VLAN-to-instance mapping entries in the MST region, and they are connected through a physical link.
The configuration of MST region-related parameters, especially the VLAN-to-instance mapping table, will result in a new spanning tree calculation. To reduce the possibility of topology instability, the MST region configuration takes effect only after you activate it by using the active region-configuration command, or enable a spanning tree protocol by using the stp enable command if the spanning tree protocol is disabled.
To configure an MST region:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter MST region view. |
stp region-configuration |
N/A |
|
3. Configure the MST region name. |
region-name name |
Optional. The MST region name is the MAC address by default. |
|
4. Configure the VLAN-to-instance mapping table. |
instance instance-id vlan vlan-list Or vlan-mapping modulo modulo |
Optional. All VLANs in an MST region are mapped to the CIST (or MSTI 0) by default. |
|
5. Configure the MSTP revision level of the MST region. |
revision-level level |
Optional. The default setting is 0. |
|
6. Display the MST region configurations that are not activated yet. |
check region-configuration |
Optional. |
|
7. Activate MST region configuration manually. |
active region-configuration |
N/A |
|
8. Display the activated configuration information of the MST region. |
display stp region-configuration [ | { begin | exclude | include } regular-expression ] |
Optional. Available in any view. |
Configuring the root bridge or a secondary root bridge
You can have MSTP determine the root bridge of a spanning tree through MSTP calculation, or you can specify the current device as the root bridge or as a secondary root bridge.
A device has independent roles in different spanning trees. It can act as the root bridge in one spanning tree and as a secondary root bridge in another. However, one device cannot be the root bridge and a secondary root bridge in the same spanning tree.
A spanning tree can have one root bridge only. If two or more devices are selected as the root bridge at the same time, the device with the lowest MAC address wins.
When the root bridge of an instance fails or is shut down, the secondary root bridge (if you have specified one) can take over the role of the primary root bridge. However, if you specify a new primary root bridge for the instance, the one that you specify, and not the secondary root bridge, will become the root bridge. If you have specified multiple secondary root bridges for an instance, when the root bridge fails, the secondary root bridge with the lowest MAC address is selected as the new root bridge.
You can specify one root bridge for each spanning tree, regardless of the device priority settings. Once you specify a device as the root bridge or a secondary root bridge, you cannot change its priority.
You can configure the current device as the root bridge by setting the device priority to 0. For the device priority configuration, see "Configuring the device priority."
Configuring the current device as the root bridge of a specific spanning tree
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Configure the current device as the root bridge. |
·
In STP/RSTP mode: ·
In MSTP mode: |
Use one of the commands. By default, a device does not function as the root bridge. |
Configuring the current device as a secondary root bridge of a specific spanning tree
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Configure the current device as a secondary root bridge. |
·
In STP/RSTP mode: ·
In MSTP mode: |
Use one of the commands. By default, a device does not function as a secondary root bridge. |
Configuring the device priority
Priority is a factor in spanning tree calculations. The priority of a device determines whether the device can be elected as the root bridge of a spanning tree. A lower numeric value indicates a higher priority. You can set the priority of a device to a low value to specify the device as the root bridge of the spanning tree. A spanning tree device can have different priorities in different MSTIs.
You cannot change the priority of a device after it is configured as the root bridge or as a secondary root bridge.
During root bridge selection, if all devices in a spanning tree have the same priority, the one with the lowest MAC address will be selected as the root bridge of the spanning tree.
To configure the priority of a device in a specified MSTI:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Configure the priority of the current device. |
·
In STP/RSTP mode: ·
In MSTP mode: |
Use one of the commands. The default setting is 32768. |
Configuring the maximum hops of an MST region
By setting the maximum hops of an MST region, you can restrict the region size. The maximum hops configured on the regional root bridge will be used as the maximum hops of the MST region.
Configuration BPDUs sent by the regional root bridge always have a hop count set to the maximum value. When a device receives this configuration BPDU, it decrements the hop count by 1 and uses the new hop count in BPDUs that it propagates. When the hop count of a BPDU reaches 0, it is discarded by the device that received it. This prevents devices beyond the reach of the maximum hop from participating in spanning tree calculation, so the size of the MST region is limited.
Make this configuration on the root bridge only. All other devices in the MST region use the maximum hop value set for the root bridge.
To configure the maximum number of hops of an MST region:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Configure the maximum hops of the MST region. |
stp max-hops hops |
The default setting is 20. |
Configuring the network diameter of a switched network
Any two terminal devices in a switched network are connected through a specific path composed of a series of devices. The network diameter is the number of devices on the path composed of the most devices. The network diameter is a parameter that indicates the network size. A bigger network diameter indicates a larger network size. Based on the network diameter you configured, the system automatically sets an optimal hello time, forward delay, and max age for the device.
To configure the network diameter of a switched network:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Configure the network diameter of the switched network in STP, RSTP, or MSTP mode. |
stp bridge-diameter diameter |
The default setting is 7. |
In STP, RSTP, or MSTP mode, each MST region is considered as a device and the configured network diameter is effective only for the CIST (or the common root bridge), but not for MSTIs.
Configuring spanning tree timers
The following timers are used for spanning tree calculations:
· Forward delay—The delay time for port state transition. To prevent temporary loops on a network, the spanning tree sets an intermediate port state, the learning state, before it transitions from the discarding state to the forwarding state. The port transitions its state after a forward delay timer expires, to make sure the state transition of the local port remains synchronized with the peer.
· Hello time—The device detects whether a link failure has occurred with the hello time interval. The spanning tree sends a configuration BPDU during every hello time interval. If the device receives no configuration BPDUs within the hello time interval, it recalculates the spanning tree.
· Max age—In the CIST of an MSTP network, the device uses the max age parameter to determine whether a configuration BPDU received by a port has expired. If it has, a new spanning tree calculation process starts. The max age timer is ineffective for MSTIs.
To prevent network instability, make sure the timer settings meet the following formulas:
· 2 × (forward delay – 1 second) ≥ max age
· Max age ≥ 2 × (hello time + 1 second)
H3C does not recommend manually setting the spanning tree timers. Instead, H3C recommends specifying the network diameter and using the automatically calculated timers based on the network diameter. If the network diameter uses the default value, the timers also use their default values.
Configure timers on the root bridge only. Timer settings on the root bridge apply to all devices on the entire switched network.
Configuration guidelines
· The length of the forward delay timer is related to the network diameter of the switched network. The larger the network diameter is, the longer the forward delay time should be. If the forward delay timer is too short, temporary redundant paths might occur. If the forward delay timer is too long, network convergence might take a long time. H3C recommends you to use the default setting.
· An appropriate hello time setting enables the device to promptly detect link failures on the network without using excessive network resources. If the hello time is too long, the device will mistake packet loss as a link failure and trigger a new spanning tree calculation process. If the hello time is too short, the device will frequently send the same configuration BPDUs, which add the device burden and waste network resources. H3C recommends you to use the default setting.
· If the max age timer is too short, the device will frequently launch spanning tree calculation and may mistake network congestion as a link failure. If the max age timer is too long, the device may fail to detect link failures and launch spanning tree calculations promptly, reducing the auto-sensing capability of the network. H3C recommends you to use the default setting.
Configuration procedure
To configure the spanning tree timers:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Configure the forward delay timer in STP, RSTP, or MSTP mode. |
stp timer forward-delay time |
Optional. The default setting is 15 seconds. |
|
3. Configure the hello timer in STP, RSTP, or MSTP mode. |
stp timer hello time |
Optional. The default setting is 2 seconds. |
|
4. Configure the max age timer in STP, RSTP, or MSTP mode. |
stp timer max-age time |
Optional. The default setting is 20 seconds. |
Configuring the timeout factor
The timeout factor is a parameter used to calculate the timeout time in the following formula: Timeout time = timeout factor × 3 × hello time.
After the network topology stabilizes, each non-root-bridge device forwards configuration BPDUs to downstream devices at the interval of hello time to determine whether any link is faulty. If a device does not receive a BPDU from the upstream device within nine times (the default timeout factor x 3) the hello time, it assumes that the upstream device has failed and starts a new spanning tree calculation process.
Sometimes a device might fail to receive a BPDU from the upstream device because the upstream device is busy. In this case, if a spanning tree calculation occurs, the calculation can fail and also waste network resources. In a stable network, you can prevent undesired spanning tree calculations by setting the timeout factor to 5, 6, or 7, resulting in a longer timeout time.
To configure the timeout factor:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Configure the timeout factor of the device. |
stp timer-factor factor |
The default setting is 3. |
Configuring the maximum port rate
The maximum rate of a port refers to the maximum number of BPDUs the port can send within each hello time. The maximum rate of a port is related to the physical status of the port and the network structure.
The higher the maximum port rate is, the more BPDUs will be sent within each hello time, and the more system resources will be used. By setting an appropriate maximum port rate, you can limit the rate at which the port sends BPDUs and prevent spanning tree protocols from using excessive network resources when the network becomes unstable. H3C recommends you to use the default setting.
To configure the maximum rate of a port or a group of ports:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view or port group view. |
·
Enter Ethernet interface view or Layer 2 aggregate interface view: ·
Enter port group view: |
Use one of the commands. |
|
3. Configure the maximum rate of the ports. |
stp transmit-limit limit |
The default setting is 10. |
Configuring edge ports
If a port directly connects to a user terminal rather than another device or a shared LAN segment, this port is regarded as an edge port. When network topology changes occur, an edge port will not cause a temporary loop. Because a device does not determine whether a port is directly connected to a terminal, you must manually configure the port as an edge port. After that, the port can transition rapidly from the blocked state to the forwarding state.
Configuration restrictions and guidelines
· If BPDU guard is disabled, a port set as an edge port will become a non-edge port again if it receives a BPDU from another port. To restore the edge port, re-enable it.
· If a port directly connects to a user terminal, configure it as an edge port and enable BPDU guard for it. This enables the port to transition to the forwarding state quickly while ensuring network security.
· You cannot configure edge port settings and loop guard on a port at the same time.
Configuration procedure
To configure edge ports:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view or port group view. |
·
Enter Ethernet interface view or Layer 2 aggregate interface view: ·
Enter port group view: |
Use one of the commands. |
|
3. Configure the current ports as edge ports. |
stp edged-port enable |
All ports are non-edge ports by default. |
Configuring path costs of ports
Path cost is a parameter related to the rate of a port. On a spanning tree device, a port can have different path costs in different MSTIs. Setting appropriate path costs allows VLAN traffic flows to be forwarded along different physical links, achieving VLAN-based load balancing.
You can have the device automatically calculate the default path cost, or you can configure the path cost for ports.
Specifying a standard for the device to use when it calculates the default path cost
|
|
CAUTION: If you change the standard that the device uses to calculate the default path costs, you restore the path costs to the default. |
You can specify a standard for the device to use in automatic calculation of the default path cost. The device supports the following standards:
· dot1d-1998—The device calculates default path costs for ports based on IEEE 802.1d-1998.
· dot1t—The device calculates default path costs for ports based on IEEE 802.1t.
· legacy—The device calculates default path costs for ports based on a private standard.
Table 7 shows a comparison between link speeds and path costs for each of these standards.
Table 7 Mappings between the link speed and the path cost
|
Link speed |
Port type |
Path cost |
||
|
IEEE 802.1d-1998 |
IEEE 802.1t |
Private standard |
||
|
0 |
N/A |
65535 |
200,000,000 |
200,000 |
|
10 Mbps |
Single port |
100 |
2,000,000 |
2000 |
|
Aggregate interface containing 2 Selected ports |
1,000,000 |
1800 |
||
|
Aggregate interface containing 3 Selected ports |
666,666 |
1600 |
||
|
Aggregate interface containing 4 Selected ports |
500,000 |
1400 |
||
|
100 Mbps |
Single port |
19 |
200,000 |
200 |
|
Aggregate interface containing 2 Selected ports |
100,000 |
180 |
||
|
Aggregate interface containing 3 Selected ports |
66,666 |
160 |
||
|
Aggregate interface containing 4 Selected ports |
50,000 |
140 |
||
|
1000 Mbps |
Single port |
4 |
20,000 |
20 |
|
Aggregate interface containing 2 Selected ports |
10,000 |
18 |
||
|
Aggregate interface containing 3 Selected ports |
6666 |
16 |
||
|
Aggregate interface containing 4 Selected ports |
5000 |
14 |
||
|
10 Gbps |
Single port |
2 |
2000 |
2 |
|
Aggregate interface containing 2 Selected ports |
1000 |
1 |
||
|
Aggregate interface containing 3 Selected ports |
666 |
1 |
||
|
Aggregate interface containing 4 Selected ports |
500 |
1 |
||
Configuration guidelines
· When it calculates path cost for an aggregate interface, IEEE 802.1t takes into account the number of Selected ports in its aggregation group, but IEEE 802.1d-1998 does not. The calculation formula of IEEE 802.1t is: Path cost = 200,000,000/link speed (in 100 kbps), where link speed is the sum of the link speed values of the Selected ports in the aggregation group.
· When the link speed of a single port exceeds 10 Gbps and the standard for default path cost calculation is dot1d-1998 or legacy, the path cost of a single port or an aggregate interface takes the smallest value. This affects the reasonableness of forwarding path selection. To solve this problem, use dot1t as the standard for default path cost calculation, or manually set the path cost for a port. For how to set the path costs of ports, see "Configuring path costs of ports.".
Configuration procedure
To specify a standard for the device to use when it calculates the default path cost:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Specify a standard for the device to use when it calculates the default path costs of its ports. |
stp pathcost-standard { dot1d-1998 | dot1t | legacy } |
Optional. By default, legacy is used as the standard to calculate the default path costs of its ports. |
Configuring path costs of ports
When the path cost of a port changes, the system recalculates the role of the port and initiates a state transition.
To configure the path cost of ports:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view or port group view. |
·
Enter Ethernet interface view or Layer 2 aggregate interface view: ·
Enter port group view: |
Use one of the commands. |
|
3. Configure the path cost of the ports. |
·
In STP/RSTP mode: ·
In MSTP mode: |
Use one of the commands. By default, the system automatically calculates the path cost of each port. |
Configuration example
# In MSTP mode, specify the device to use IEEE 802.1d-1998 to calculate the default path costs of its ports, and set the path cost of GigabitEthernet 1/0/1 to 200 on MSTI 2.
<Sysname> system-view
[Sysname] stp pathcost-standard dot1d-1998
[Sysname] interface GigabitEthernet 1/0/1
[Sysname-GigabitEthernet1/0/1] stp instance 2 cost 200
Configuring the port priority
The priority of a port is an important factor in determining whether the port can be elected as the root port of a device. If all other conditions are the same, the port with the highest priority will be elected as the root port.
On a spanning tree device, a port can have different priorities and play different roles in different spanning trees, so that data from different VLANs can be propagated along different physical paths to implement per-VLAN load balancing. You can set port priority values based on your actual network requirements.
If the port priority changes, the system re-calculates the port role and initiate a state transition.
To configure the priority of a port or a group of ports:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view or port group view. |
·
Enter Ethernet interface view or Layer 2 aggregate interface view: ·
Enter port group view: |
Use one of the commands. |
|
3. Configure the port priority. |
·
In STP/RSTP mode: ·
In MSTP mode: |
Use one of the commands. The default setting is 128. |
Configuring the port link type
A point-to-point link directly connects two devices. If two root ports or designated ports are connected over a point-to-point link, they can rapidly transition to the forwarding state after a proposal-agreement handshake process.
Configuration restrictions and guidelines
· You can configure the link type as point-to-point for a Layer 2 aggregate interface or a port that operates in full duplex mode. H3C recommends you to use the default setting and let the device to automatically detect the port link type.
· The stp point-to-point force-false or stp point-to-point force-true command configured on a port in MSTP mode is effective for all MSTIs.
· If the physical link to which the port connects is not a point-to-point link but you set it to be one, the configuration might cause temporary loops.
Configuration procedure
To configure the link type of a port or a group of ports:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view or port group view. |
·
Enter Ethernet interface view or Layer 2 aggregate interface view: ·
Enter port group view: |
Use one of the commands. |
|
3. Configure the port link type. |
stp point-to-point { auto | force-false | force-true } |
By default, the link type is auto and the port automatically detects the link type. |
Configuring the mode a port uses to recognize and send MSTP packets
A port can receive and send MSTP packets in the following formats:
· dot1s—802.1s-compliant standard format
· legacy—Compatible format
By default, the packet format recognition mode of a port is auto. The port automatically distinguishes the two MSTP packet formats, and determines the format of packets that it will send based on the recognized format.
You can configure the MSTP packet format on a port. When operating in MSTP mode after the configuration, the port sends and receives only MSTP packets of the format that you have configured to communicate with devices that send packets of the same format.
MSTP provides MSTP packet format incompatibility guard. In MSTP mode, if a port is configured to recognize/send MSTP packets in a mode other than auto, and if it receives a packet in a format different from the specified type, the port becomes a designated port and remains in the discarding state to prevent the occurrence of a loop.
MSTP provides MSTP packet format frequent change guard. If a port receives MSTP packets of different formats frequently, the MSTP packet format configuration contains errors. If the port is operating in MSTP mode, it will be shut down for protection. Ports disabled in this way can be re-activated after a detection interval. For more information about the detection interval, see Fundamentals Configuration Guide.
To configure the MSTP packet format to be supported on a port or a group of ports:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view or port group view. |
·
Enter Ethernet interface view or Layer 2 aggregate interface view: ·
Enter port group view: |
Use one of the commands. |
|
3. Configure the mode that the port uses to recognize/send MSTP packets. |
stp compliance { auto | dot1s | legacy } |
The default setting is auto. |
Enabling the spanning tree feature
You must enable the spanning tree feature for the device before any other spanning tree related configurations can take effect. You can disable the spanning tree feature for certain ports with the undo stp enable command to exclude them from spanning tree calculation and save CPU resources of the device.
In STP, RSTP, or MSTP mode, make sure the spanning tree feature is enabled globally and on the desired ports.
To enable the spanning tree feature in STP, RSTP, or MSTP mode:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enable the spanning tree feature globally. |
stp enable |
By default, the spanning tree feature is globally disabled. |
|
3. Enter interface view or port group view. |
·
Enter Ethernet interface view or Layer 2 aggregate interface view: ·
Enter port group view: |
Use one of the commands. |
|
4. Enable the spanning tree feature for the port or group of ports. |
stp enable |
Optional. By default, the spanning tree feature is enabled on all ports. |
Performing mCheck
If a port on a device that is running MSTP or RSTP connects to an STP device, this port automatically migrates to STP mode. However, it cannot automatically transition back to the original mode when:
· The STP device is shut down or removed.
· The STP device transitions to MSTP or RSTP mode.
Suppose Device A running STP, Device B with no spanning tree feature enabled, and Device C running RSTP or MSTP are connected in order. Device B will transparently transmit STP BPDUs, and the port on Device C and connecting to Device B will transition to the STP mode. After you enable the spanning tree feature on Device B, to run RSTP or MSTP between Device B and Device C, you must perform an mCheck operation on the ports interconnecting Device B and Device C, in addition to configuring the spanning tree to operate in RSTP or MSTP mode on Device B.
To forcibly transition the port to operate in the original mode, you can perform an mCheck operation. An mCheck operation takes effect on a device that operates in MSTP or RSTP mode.
The following methods for performing mCheck produce the same result.
Performing mCheck globally
|
Step |
Command |
|
1. Enter system view. |
system-view |
|
2. Perform mCheck. |
stp mcheck |
Performing mCheck in interface view
|
Step |
Command |
|
1. Enter system view. |
system-view |
|
2. Enter Ethernet interface view or Layer 2 aggregate interface view. |
interface interface-type interface-number |
|
3. Perform mCheck. |
stp mcheck |
Configuring digest snooping
As defined in IEEE 802.1s, connected devices are in the same region only when their MST region-related configurations (region name, revision level, and VLAN-to-instance mappings) are identical. A spanning tree device identifies devices in the same MST region by determining the configuration ID in BPDU packets. The configuration ID includes the region name, revision level, and configuration digest, which is in 16-byte length and is the result calculated by the HMAC-MD5 algorithm based on VLAN-to-instance mappings.
Because spanning tree implementations vary with vendors, the configuration digests calculated through private keys are different. Devices of different vendors in the same MST region cannot communicate with each other.
To enable communication between an H3C device and a third-party device, enable the digest snooping feature on the port that connects the H3C device to the third-party device in the same MST region.
Configuration prerequisites
Configuration restrictions and guidelines
· With the digest snooping feature enabled, in-the-same-region verification does not need comparison of configuration digest, so the VLAN-to-instance mappings must be the same on associated ports.
· When digest snooping is globally enabled, if you modify the VLAN-to-instance mapping or use the undo stp region-configuration command to restore the default MST region configuration, traffic may be interrupted because the local VLAN-to-instance mapping is different from that on a neighbor device. Perform these operations with caution.
· To make digest snooping take effect, you must enable it both globally and on associated ports. H3C recommends that you enable digest snooping on all associated ports first and then globally. This will make the configuration take effect on all configured ports and reduce impact on the network.
· To avoid loops, do not enable digest snooping on MST region edge ports.
· H3C recommends you to enable digest snooping first and then the spanning tree feature. To avoid traffic interruption, do not configure digest snooping when the network is already working well.
Configuration procedure
You can enable digest snooping only on an H3C device that is connected to a third-party device which uses its private key to calculate the configuration digest.
To configure digest snooping:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view or port group view. |
·
Enter Ethernet interface view or Layer 2 aggregate interface view: ·
Enter port group view: |
Use one of the commands. |
|
3. Enable digest snooping on the interface or port group. |
stp config-digest-snooping |
By default, digest snooping is disabled on a port. |
|
4. Return to system view. |
quit |
N/A |
|
5. Enable global digest snooping. |
stp config-digest-snooping |
By default, digest snooping is disabled globally. |
Digest snooping configuration example
Network requirements
As shown in Figure 7, AP 1 and AP 2 connect to Device C, which is a third-party device. All these devices are in the same region.
Enable digest snooping on the ports of AP 1 and AP 2 that connect to Device C, so that the three devices can communicate with one another.
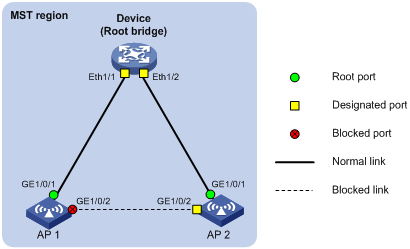
Configuration procedure
# Enable digest snooping on GigabitEthernet 1/0/1 of AP 1 and enable global digest snooping on AP 1.
<AP1> system-view
[AP1] interface GigabitEthernet 1/0/1
[AP1-GigabitEthernet1/0/1] stp config-digest-snooping
[AP1-GigabitEthernet1/0/1] quit
[AP1] stp config-digest-snooping
# Enable digest snooping on GigabitEthernet 1/0/1 of AP 2 and enable global digest snooping on AP 2.
<AP2> system-view
[AP2] interface GigabitEthernet 1/0/1
[AP2-GigabitEthernet1/0/1] stp config-digest-snooping
[AP2-GigabitEthernet1/0/1] quit
[AP2] stp config-digest-snooping
Configuring No Agreement Check
In RSTP and MSTP, the following types of messages are used for rapid state transition on designated ports:
· Proposal—Sent by designated ports to request rapid transition
· Agreement—Used to acknowledge rapid transition requests
Both RSTP and MSTP devices can perform rapid transition on a designated port only when the port receives an agreement packet from the downstream device. RSTP and MSTP devices have the following differences:
· For MSTP, the root port of the downstream device sends an agreement packet only after it receives an agreement packet from the upstream device.
· For RSTP, the downstream device sends an agreement packet regardless of whether an agreement packet is received from the upstream device.
Figure 8 Rapid state transition of an MSTP designated port
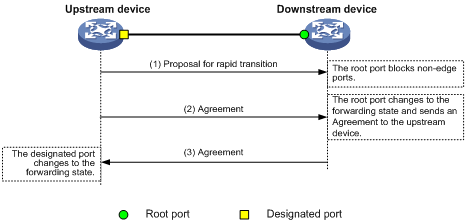
Figure 9 Rapid state transition of an RSTP designated port
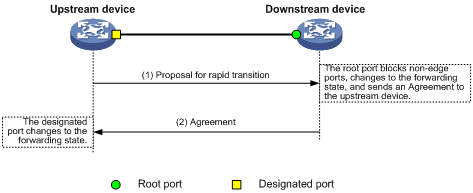
If the upstream device is a third-party device, the rapid state transition implementation might be limited. For example, when the upstream device uses a rapid transition mechanism similar to that of RSTP, and the downstream device adopts MSTP and does not operate in RSTP mode, the root port on the downstream device receives no agreement packet from the upstream device and sends no agreement packets to the upstream device. As a result, the designated port of the upstream device fails to transit rapidly, and can only change to the forwarding state after a period that is twice the Forward Delay.
You can enable the No Agreement Check feature on the downstream device's port to enable the designated port of the upstream device to transit its state rapidly.
Configuration prerequisites
Before you configure the No Agreement Check function, complete the following tasks:
· Connect a device to a third-party upstream device that supports spanning tree protocols with a point-to-point link.
· Configure the same region name, revision level and VLAN-to-instance mappings on the two devices, assigning them to the same region.
Configuration procedure
To make the No Agreement Check feature take effect, enable it on the root port.
To configure No Agreement Check:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface or port group view. |
·
Enter Ethernet interface view or Layer 2 aggregate interface view: ·
Enter port group view: |
Use one of the commands. |
|
3. Enable No Agreement Check. |
stp no-agreement-check |
By default, No Agreement Check is disabled. |
No Agreement Check configuration example
Network requirements
As shown in Figure 10:
· The AP connects to a third-party switch that has a different spanning tree implementation. Both devices are in the same region.
· The switch is the regional root bridge, and the AP is the downstream device.
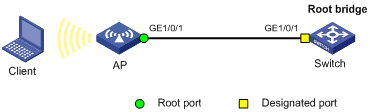
Configuration procedure
# Enable No Agreement Check on GigabitEthernet 1/0/1 of the AP.
<AP> system-view
[AP] interface GigabitEthernet 1/0/1
[AP-GigabitEthernet1/0/1] stp no-agreement-check
Configuring protection functions
A spanning tree device supports the following protection functions:
· BPDU guard
· Root guard
· Loop guard
· TC-BPDU guard
Enabling BPDU guard
For access layer devices, access ports can directly connect to user terminals (such as PCs) or file servers. Access ports are configured as edge ports to allow rapid transition. When these ports receive configuration BPDUs, the system automatically sets the ports as non-edge ports and starts a new spanning tree calculation process. This causes a change of network topology. Under normal conditions, these ports should not receive configuration BPDUs. However, if someone forges configuration BPDUs maliciously to attack the devices, the network will become unstable.
The spanning tree protocol provides the BPDU guard function to protect the system against such attacks. With the BPDU guard function enabled on devices, when edge ports receive configuration BPDUs, the system closes these ports and notifies the NMS that they have been closed by the spanning tree protocol. The device will reactivate closed ports after the port status detection timer expires. For more information about the port status detection timer, see Fundamentals Configuration Guide.
Configure BPDU guard on a device with edge ports configured. BPDU guard does not take effect on loopback testing-enabled ports. For more information about loopback testing, see Layer 2 Configuration Guide.
To enable BPDU guard:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enable the BPDU guard function for the device. |
stp bpdu-protection |
By default, BPDU guard is disabled. |
Enabling root guard
The root bridge and secondary root bridge of a spanning tree should be located in the same MST region. Especially for the CIST, the root bridge and secondary root bridge are put in a high-bandwidth core region during network design. However, because of possible configuration errors or malicious attacks on the network, the legal root bridge might receive a configuration BPDU with a higher priority. Another device will supersede the current legal root bridge, causing an undesired change in the network topology. The traffic that should go over high-speed links is switched to low-speed links, resulting in network congestion.
To prevent this situation, MSTP provides the root guard function. If the root guard function is enabled on a port of a root bridge, this port plays the role of designated port on all MSTIs. After this port receives a configuration BPDU with a higher priority from an MSTI, it immediately sets that port to the listening state in the MSTI, without forwarding the packet. This is equivalent to disconnecting the link connected with this port in the MSTI. If the port receives no BPDUs with a higher priority after a period that is twice the forwarding delay, it reverts to its original state.
Configure root guard on a designated port. You cannot configure root guard and loop guard on a port at the same time.
To enable root guard:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view or port group view. |
·
Enter Ethernet interface view or Layer 2 aggregate interface view: ·
Enter port group view: |
Use one of the commands. |
|
3. Enable the root guard function for the ports. |
stp root-protection |
By default, root guard is disabled. |
Enabling loop guard
By continuing to receive BPDUs from the upstream device, a device can maintain the state of the root port and blocked ports. However, link congestion or unidirectional link failures might cause these ports to fail to receive BPDUs from upstream devices. The device will reselect the port roles: Those ports in forwarding state that failed to receive upstream BPDUs will become designated ports, and the blocked ports will transition to the forwarding state, resulting in loops in the switched network. The loop guard function can suppress the occurrence of such loops.
The initial state of a loop guard-enabled port is discarding in every MSTI. When the port receives BPDUs, its state transitions normally. Otherwise, it stays in the discarding state to prevent temporary loops.
Configuration restrictions and guidelines
· Configure loop guard on the root port and alternate ports of a device.
· Do not enable loop guard on a port that connects user terminals. Otherwise, the port will stay in the discarding state in all MSTIs because it cannot receive BPDUs.
· You cannot configure edge port settings and loop guard, or configure root guard and loop guard on a port at the same time.
Configuration procedure
To enable loop guard:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view or port group view. |
·
Enter Ethernet interface view or Layer 2 aggregate interface view: ·
Enter port group view: |
Use one of the commands. |
|
3. Enable the loop guard function for the ports. |
stp loop-protection |
By default, loop guard is disabled. |
Enabling TC-BPDU guard
When a device receives topology change (TC) BPDUs (the BPDUs that notify devices of topology changes), the device flushes the forwarding address entries. If someone forges TC-BPDUs to attack the device, the device will receive a large number of TC-BPDUs within a short time and be busy with flushing forwarding address entries. This affects network stability.
With the TC-BPDU guard function, you can set the maximum number of immediate forwarding address entry flushes that the device can perform every a specified period of time (10 seconds). For TC-BPDUs received in excess of the limit, the device performs a forwarding address entry flush when the time period expires. This prevents frequent flushing of forwarding address entries.
H3C does not recommend you disable this feature.
To enable TC-BPDU guard:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enable the TC-BPDU guard function. |
stp tc-protection enable |
Optional. By default, TC-BPDU guard is enabled. |
|
3. Configure the maximum number of forwarding address entry flushes that the device can perform every 10 seconds. |
stp tc-protection threshold number |
Optional. The default setting is 6. |
Displaying and maintaining the spanning tree
|
Task |
Command |
Remarks |
|
Display information about ports blocked by spanning tree protection functions. |
display stp abnormal-port [ | { begin | exclude | include } regular-expression ] |
Available in any view. |
|
Display BPDU statistics on ports. |
display stp bpdu-statistics [ interface interface-type interface-number [ instance instance-id ] ] [ | { begin | exclude | include } regular-expression ] |
Available in any view. |
|
Display information about ports shut down by spanning tree protection functions. |
display stp down-port [ | { begin | exclude | include } regular-expression ] |
Available in any view. |
|
Display historical information about port role calculations for the specified MSTI or all MSTIs. |
display stp [ instance instance-id ] history [ | { begin | exclude | include } regular-expression ] |
Available in any view. |
|
Display statistics about TC/TCN BPDUs sent and received by all ports in the specified MSTI or all MSTIs. |
display stp [ instance instance-id ] tc [ | { begin | exclude | include } regular-expression ] |
Available in any view. |
|
Display spanning tree status and statistics. |
display stp [ instance instance-id ] [ interface interface-list ] [ brief ] [ | { begin | exclude | include } regular-expression ] |
Available in any view. |
|
Display MST region configuration information in effect. |
display stp region-configuration [ | { begin | exclude | include } regular-expression ] |
Available in any view. |
|
Display root bridge information for all MSTIs. |
display stp root [ | { begin | exclude | include } regular-expression ] |
Available in any view. |
|
Clear spanning tree statistics. |
reset stp [ interface interface-list ] |
Available in user view. |
MSTP configuration example
Network requirements
As shown in Figure 11, all devices on the network are in the same MST region, WDS links are established among APs, and AP 1, AP 2, and AP 3 work at the access layer.
Configure MSTP so that packets of VLAN 10 are forwarded along MSTI 1, and those of VLAN 20 are forwarded along MSTI 2.
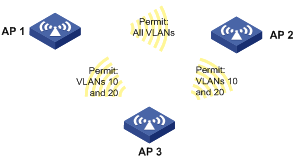
Configuration procedure
Configuring AP 1
# Enter MST region view, configure the MST region name as example, map VLAN 10 and VLAN 20 to MSTI 1 and MSTI 2 respectively, and configure the revision level of the MST region as 0.
<AP1> system-view
[AP1] stp region-configuration
[AP1-mst-region] region-name example
[AP1-mst-region] instance 1 vlan 10
[AP1-mst-region] instance 2 vlan 20
[AP1-mst-region] revision-level 0
# Activate MST region configuration.
[AP1-mst-region] active region-configuration
[AP1-mst-region] quit
# Enable the spanning tree feature globally.
[AP1] stp enable
# Display effective MST region configuration information.
[AP1] display stp region-configuration
Oper configuration
Format selector :0
Region name :example
Revision level :0
Configuration digest :0x9357ebb7a8d74dd5fef4f2bab50531aa
Instance Vlans Mapped
0 1 to 9, 11 to 19, 21 to 4094
1 10
2 20
Configuring AP 2
# Enter MST region view, configure the MST region name as example, map VLAN 10 and VLAN 20 to MSTI 1 and MSTI 2 respectively, and configure the revision level of the MST region as 0.
<AP2> system-view
[AP2] stp region-configuration
[AP2-mst-region] region-name example
[AP2-mst-region] instance 1 vlan 10
[AP2-mst-region] instance 2 vlan 20
[AP2-mst-region] revision-level 0
# Activate MST region configuration.
[AP2-mst-region] active region-configuration
[AP2-mst-region] quit
# Enable the spanning tree feature globally.
[AP2] stp enable
# Display effective MST region configuration information.
[AP2] display stp region-configuration
Oper configuration
Format selector :0
Region name :example
Revision level :0
Configuration digest :0x9357ebb7a8d74dd5fef4f2bab50531aa
Instance Vlans Mapped
0 1 to 9, 11 to 19, 21 to 4094
1 10
2 20
Configuring AP 3
# Enter MST region view, configure the MST region name as example, map VLAN 10 and VLAN 20 to MSTI 1 and MSTI 2 respectively, and configure the revision level of the MST region as 0.
<AP3> system-view
[AP3] stp region-configuration
[AP3-mst-region] region-name example
[AP3-mst-region] instance 1 vlan 10
[AP3-mst-region] instance 2 vlan 20
[AP3-mst-region] revision-level 0
# Activate MST region configuration.
[AP3-mst-region] active region-configuration
[AP3-mst-region] quit
# Enable the spanning tree feature globally.
[AP3] stp enable
# Display effective MST region configuration information.
[AP3] display stp region-configuration
Oper configuration
Format selector :0
Region name :example
Revision level :0
Configuration digest :0x9357ebb7a8d74dd5fef4f2bab50531aa
Instance Vlans Mapped
0 1 to 9, 11 to 19, 21 to 4094
1 10
2 20